German authorities have identified Daniil Maksimovich Shchukin, 31, as the elusive hacker known as "UNKN" who led the notorious ransomware groups GandCrab and REvil, responsible for over $2 billion in extortions and 130 cyberattacks causing 35 million euros in damages.
German authorities have unmasked the shadowy figure behind two of the most destructive ransomware operations in cybercrime history, identifying 31-year-old Russian Daniil Maksimovich Shchukin as the mastermind known online as "UNKN" who led both the GandCrab and REvil ransomware gangs.
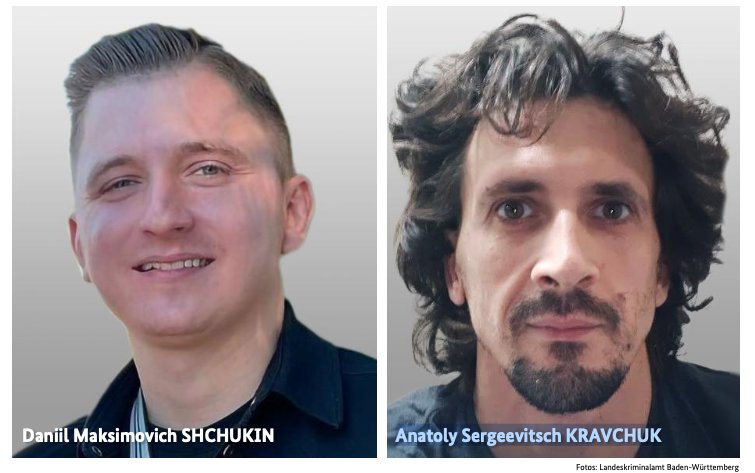
The Bundeskriminalamt (BKA), Germany's federal criminal police, published an advisory naming Shchukin as the head of one of the world's largest ransomware operations. According to the BKA, Shchukin and 43-year-old Russian Anatoly Sergeevitsch Kravchuk extorted nearly 2 million euros across two dozen cyberattacks that caused more than 35 million euros in total economic damage between 2019 and 2021.
Shchukin's identity emerged from a February 2023 U.S. Justice Department filing seeking seizure of cryptocurrency accounts tied to REvil's activities. The filing revealed a digital wallet associated with Shchukin contained over $317,000 in ill-gotten cryptocurrency.
The Rise and Fall of GandCrab
GandCrab first appeared in January 2018 as a ransomware-as-a-service operation that paid hackers substantial shares of profits for gaining initial access to corporate networks. The malware's developers released five major revisions, each introducing new features and bug fixes designed to evade security detection.
The operation proved extraordinarily lucrative, with the group announcing its shutdown on May 31, 2019, after extorting more than $2 billion from victims. In a now-infamous farewell message, GandCrab declared, "We are a living proof that you can do evil and get off scot-free."
REvil's Evolution into Big-Game Hunting
As GandCrab wound down, REvil emerged almost immediately, fronted by UNKNOWN who deposited $1 million in escrow on a Russian cybercrime forum to demonstrate credibility. Cybersecurity experts quickly recognized REvil as essentially a reorganization of GandCrab.
UNKNOWN gave an interview to Dmitry Smilyanets of Recorded Future, describing a dramatic personal transformation: "As a child, I scrounged through the trash heaps and smoked cigarette butts. I walked 10 km one way to the school. I wore the same clothes for six months. In my youth, in a communal apartment, I didn't eat for two or even three days. Now I am a millionaire."
REvil pioneered the "double extortion" technique, charging victims once for decryption keys and separately for promises not to publish stolen data. The group evolved into a sophisticated operation that reinvested earnings into improving their infrastructure and mirroring legitimate business practices.
As detailed in The Ransomware Hunting Team by Renee Dudley and Daniel Golden, "Just as a real-world manufacturer might hire other companies to handle logistics or web design, ransomware developers increasingly outsourced tasks beyond their purview, focusing instead on improving the quality of their ransomware."
The authors described how ancillary service providers emerged to support the ransomware economy: "'Cryptor' providers ensured ransomware could not be detected by standard anti-malware scanners. 'Initial access brokerages' specialized in stealing credentials and finding vulnerabilities in target networks, selling that access to ransomware operators and affiliates."
REvil targeted organizations with over $100 million in annual revenues and cyber insurance policies known to pay out. The group's most notorious attack came over the July 4, 2021 weekend when they hacked Kaseya, affecting over 1,500 businesses, nonprofits, and government agencies.
The FBI's Infiltration and REvil's Demise
The FBI had infiltrated REvil's servers prior to the Kaseya attack but couldn't reveal their presence. The group never recovered from this compromise, particularly after the FBI released a free decryption key for REvil victims who couldn't or didn't pay.
Connecting the Dots
While little directly connects Shchukin to UNKNOWN's various accounts on Russian crime forums, investigators found links to an earlier hacker identity called "Ger0in." Ger0in operated large botnets and sold "installs"—allowing other cybercriminals to deploy malware to thousands of PCs simultaneously—between 2010 and 2011, well before UNKNOWN's appearance.
Image comparison analysis using Pimeyes found matches between BKA mugshots and birthday celebration photos from 2023 in Krasnodar, Russia, where Shchukin is believed to reside. The photos show a young man named Daniel wearing the same expensive watch visible in the BKA's released images.

German authorities believe Shchukin is likely in Russia, though they haven't ruled out travel. The identification represents a significant breakthrough in tracking one of cybercrime's most elusive figures, whose operations have caused billions in damages and disrupted thousands of organizations worldwide.
The case highlights the growing sophistication of international law enforcement cooperation in pursuing cybercriminals who once believed they could operate with impunity from Russian territory.

Comments
Please log in or register to join the discussion