An exploration of how a curious researcher accidentally dismantled a police honeypot operation, revealing the complex world of cybersecurity enforcement and its questionable effectiveness.
The digital landscape continues to evolve in fascinating ways, particularly in the ongoing battle between law enforcement and cybercriminals. Recently, a researcher known as lina stumbled upon an intriguing case study in this perpetual cat-and-mouse game: a honeypot website created by the Dutch Police as part of Operation PowerOFF, an international initiative targeting DDoS-for-hire services. What began as casual research ended with the researcher inadvertently causing the entire operation to be shut down, raising important questions about the effectiveness and resource allocation of such cybersecurity enforcement strategies.
Operation PowerOFF: A Global Effort with Dutch Roots
Operation PowerOFF represents a significant international collaboration among various law enforcement agencies, including the FBI, the UK National Crime Agency, and Europol. However, evidence suggests that the Dutch Police play a particularly central role in this operation, likely managing much of the underlying infrastructure. Over the years, this operation has resulted in the seizure of approximately one hundred domains and several arrests, demonstrating a sustained commitment to combating cybercrime.
The operation's approach appears twofold, as evidenced by the discovery of two distinct types of websites: covert honeypots designed to lure potential criminals into revealing their identities, and overt warning sites intended to deter through fear and education. This dual strategy reflects a sophisticated understanding of psychological manipulation in the digital realm.
Cyberzap: The Convincing Yet Flawed Honeypot
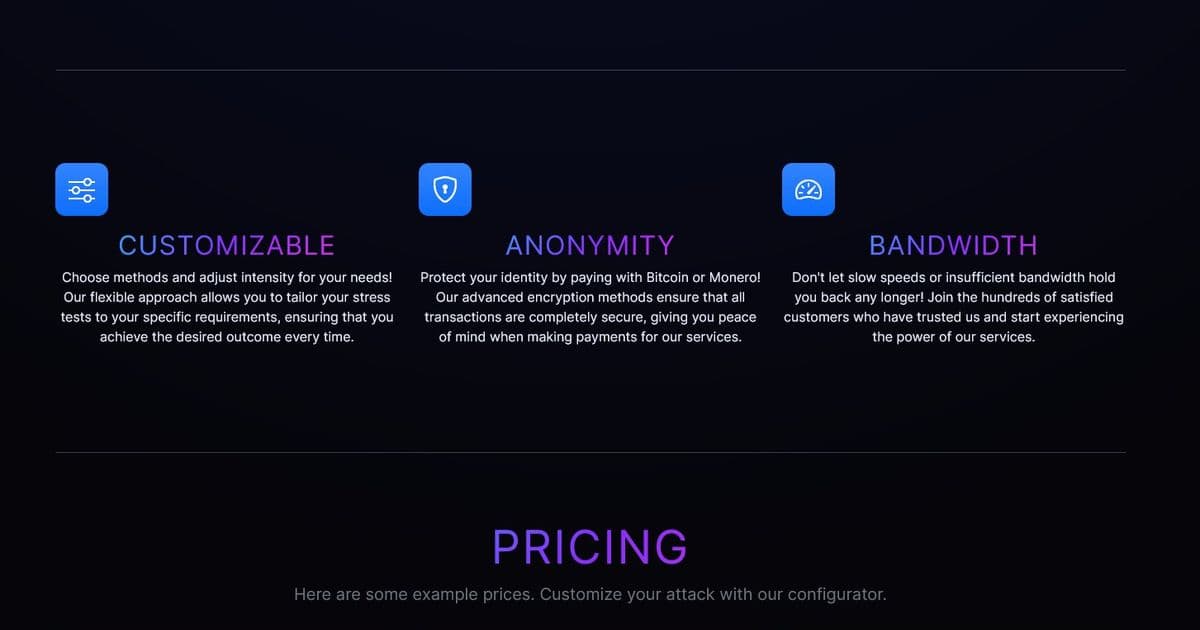
The researcher's discovery of Cyberzap.fun revealed a surprisingly well-crafted honeypot that mirrored the appearance of legitimate DDoS-for-hire services. The site included professional touches such as robots.txt files, sitemaps, SEO-friendly meta tags, and a functional registration process complete with activation emails. The dashboard featured realistic-looking network speed graphs and bot counters that updated in real-time, creating an illusion of a fully operational service.
However, several tell-tale signs betrayed the site's true nature. Most notably, the use of bit.nl as the server host and mail server provider immediately raised suspicions, as this appears to be a common hosting choice for Dutch police operations. Additionally, the payment process was deliberately designed to fail at every attempt, regardless of the payment method selected, ensuring that no actual attacks would be carried out while still capturing the user's information.
The researcher's approach to testing the honeypot was methodical and cautious. Using a research-specific email address ([email protected]), they registered and explored the site's functionality without attempting any actual criminal activity. This careful approach allowed the researcher to document the honeypot's features while maintaining ethical boundaries.
Netcrashers: The Overt Warning Alternative
In contrast to the subtle Cyberzap honeypot, Netcrashers.net represents the overt arm of Operation PowerOFF. This site immediately redirects users to a police warning page the moment any button is clicked, explicitly stating that the domain is owned by the Dutch Police and that DDoS attacks are illegal with serious consequences. The message emphasizes that cybercriminals always leave traces online, serving as both a warning and a psychological deterrent.
This approach targets a different demographic than the covert honeypot, likely aiming to scare away curious teenagers or individuals who might otherwise be tempted to explore DDoS services. The stark contrast between these two approaches demonstrates the operation's comprehensive strategy, addressing potential criminals at various stages of their decision-making process.
The Accidental Take Down: Unintended Consequences
The most intriguing aspect of this story is how the researcher's activities inadvertently led to the shutdown of the Cyberzap honeypot. After documenting the site's features and taking screenshots, the researcher attempted to access the site again only to encounter a 401 Unauthorized error. The site was completely locked down, with the researcher's distinctive email address likely being the key factor that triggered this response.
The police's reaction appears to have been one of panic, as they also shut down an unrelated domain (bytecannon.net) with the same authorization message. This overreaction suggests that the operation may not have been as robust as intended, with a single researcher's activities causing significant disruption. The fact that Netcrashers.net remained online indicates that the police maintained their overt warning service while abandoning their covert honeypot, suggesting a prioritization of visible deterrence over intelligence gathering.
Questionable Effectiveness: Resources vs. Results
The discovery that only 14 "attacks" had been ordered on Cyberzap raises serious questions about the operation's effectiveness and resource allocation. Given the relatively small number of interactions, it's reasonable to speculate that most of these were likely from police officers testing their own system rather than actual criminals. This raises the question of whether the substantial investment in developing and maintaining such honeypots represents an efficient use of taxpayer money.
The operation's recent AI propaganda video further calls into question its priorities. The video, which depicts law enforcement raiding a teenager's home in connection with Minecraft server attacks, appears to be more focused on self-promotion than effective crime prevention. The agency's own description of it as a "cool video" on their "branding page" suggests a concerning emphasis on public relations over substantive results.
Psychological Warfare: Creating Paranoia in the Cybercrime Community
Despite questions about their effectiveness, honeypot operations do serve a psychological purpose. By creating uncertainty and paranoia in the cybercrime community, law enforcement can potentially deter individuals from using DDoS-for-hire services altogether. The knowledge that any such service could be a police honeypot logging their IP addresses and communications creates a significant barrier to entry for potential criminals.
This psychological approach represents a form of digital deterrence that doesn't require catching every offender. If enough individuals are deterred from using these services due to fear of being caught, the operation can achieve its broader goal of reducing the prevalence of DDoS attacks, even if it doesn't result in many arrests or prosecutions.
The Ethics of Deception: Law Enforcement as Deceivers
The use of honeypots by law enforcement raises important ethical questions about the boundaries of acceptable deception. While the goal of preventing cybercrime is legitimate, the methods employed by operations like PowerOFF blur the line between law enforcement and entrapment. The deliberate creation of fake services designed to lure individuals into revealing potentially incriminating information challenges traditional notions of due process and fair play.
Moreover, the operation's focus on creating fear and uncertainty through overt warnings and the shutdown of legitimate services raises concerns about freedom of access to information and the potential for overreach. While the intention may be to protect potential victims of DDoS attacks, the methods employed may have unintended consequences for the broader digital ecosystem.
The Future of Cybersecurity Enforcement
The case of Cyberzap and Netcrashers offers valuable insights into the future of cybersecurity enforcement. As technology continues to evolve, so too will the methods used by both criminals and law enforcement. The fact that a single researcher was able to identify and disrupt a police honeypot suggests that these operations may become increasingly difficult to maintain effectively.
Moving forward, cybersecurity enforcement agencies may need to focus more on collaboration with private sector partners and invest in more sophisticated detection and prevention technologies rather than relying heavily on deceptive honeypots. The development of more transparent and educational approaches that focus on prevention rather than punishment may ultimately prove more effective in reducing cybercrime.
The story of Cyberzap serves as a reminder that the digital landscape is a complex and ever-changing environment where the lines between criminal and researcher, deception and transparency, are often blurred. As we navigate this evolving space, it's essential to maintain a critical perspective on the methods used by law enforcement and to ensure that the pursuit of security does not come at the cost of fundamental rights and freedoms.
For those interested in exploring Operation PowerOFF further, the official Wikipedia page provides a comprehensive overview of the initiative. Additionally, the seized domains database offers insights into the scope of the operation's activities. The archived version of the Cyberzap website can be viewed here, preserving a fascinating case study in digital law enforcement for future analysis.
Comments
Please log in or register to join the discussion