A security expert warns against the dangerous practice of using passkeys for encrypting user data, highlighting how this creates irreversible data loss risks when users delete their credentials.
When a technology promises to solve one of the internet's oldest problems, it's tempting to extend its use to related challenges. Passkeys have emerged as a phishing-resistant authentication solution that finally offers a viable alternative to passwords. But in our enthusiasm to leverage this new capability, many organizations have made a critical error: using passkeys to encrypt user data.
The Core Problem: Authentication vs. Encryption
The fundamental issue lies in conflating two distinct security functions. Authentication verifies identity - proving you are who you claim to be. Encryption protects data - ensuring only authorized parties can access it. When we use the same credential for both purposes, we create a dangerous coupling.
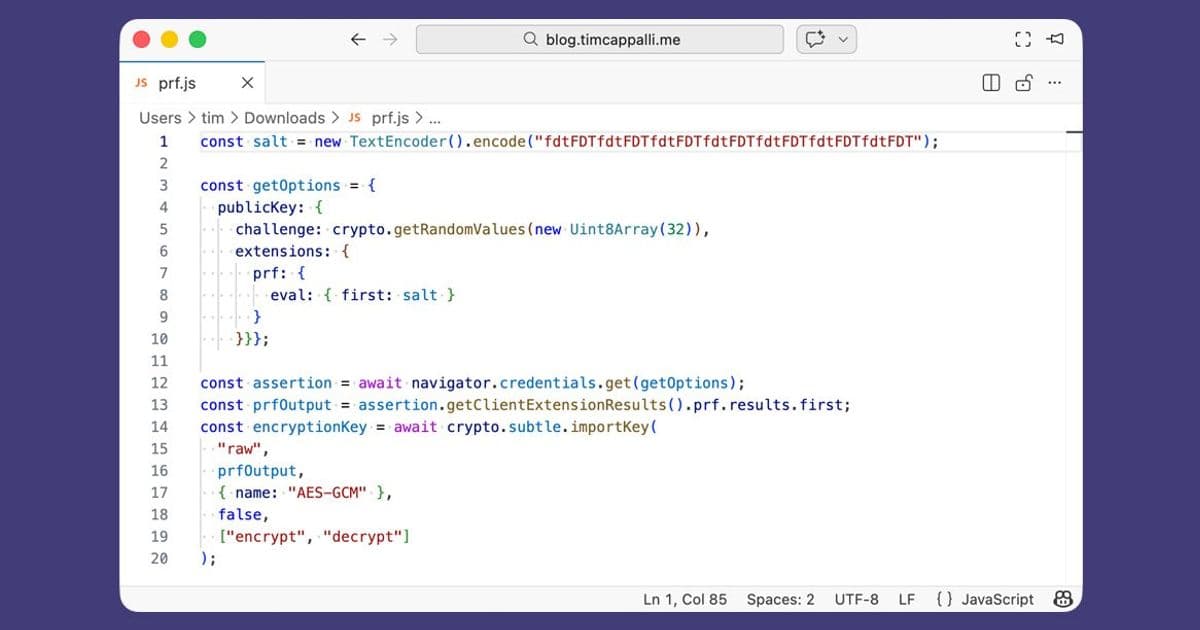
Consider what happens when Erika, a typical user, enables encrypted backups in her messaging app using her passkey. The app uses the WebAuthn PRF (Pseudo-Random Function) extension to derive encryption keys from her passkey. This seems elegant - one credential serving dual purposes. But this elegance masks a critical vulnerability.
The Cascade of Data Loss
A few months later, Erika decides to clean up her credential manager. She sees a passkey she doesn't recognize for a messaging app and deletes it. No warning appears about the consequences. No indication that this passkey protects years of messages and photos from deceased loved ones.
When she gets a new phone and tries to restore her backup, she's prompted for the passkey she no longer has. The app offers no recovery path. The data is gone forever. The blast radius of losing an authentication credential has expanded to include irreplaceable personal data.
This scenario isn't hypothetical. I've seen it happen across messaging apps, document storage services, crypto wallets, and credential managers. The pattern repeats: users lose access to encrypted data when they delete or lose their passkeys.
Why PRF Exists in WebAuthn
It's worth understanding why the PRF extension exists in the first place. The designers of WebAuthn included PRF specifically for credential managers and operating systems. Here, the use case makes sense: a passkey with PRF can unlock your credential manager vault more quickly and securely than alternatives.
Credential managers have built-in safeguards - master passwords, per-device keys, recovery keys, and social recovery mechanisms. Losing access to a passkey used to unlock your credential manager rarely results in complete data loss because these additional protections exist.
The problem arises when we extend this pattern to user data encryption without those safeguards.
The User Experience Failure
Look at what users actually see when deleting a passkey:
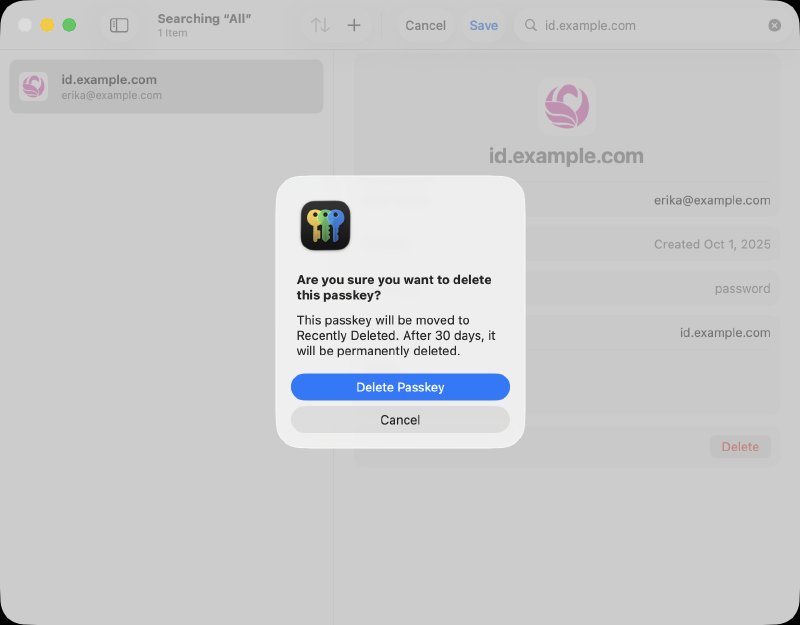 Example: deleting a passkey in Apple Passwords
Example: deleting a passkey in Apple Passwords
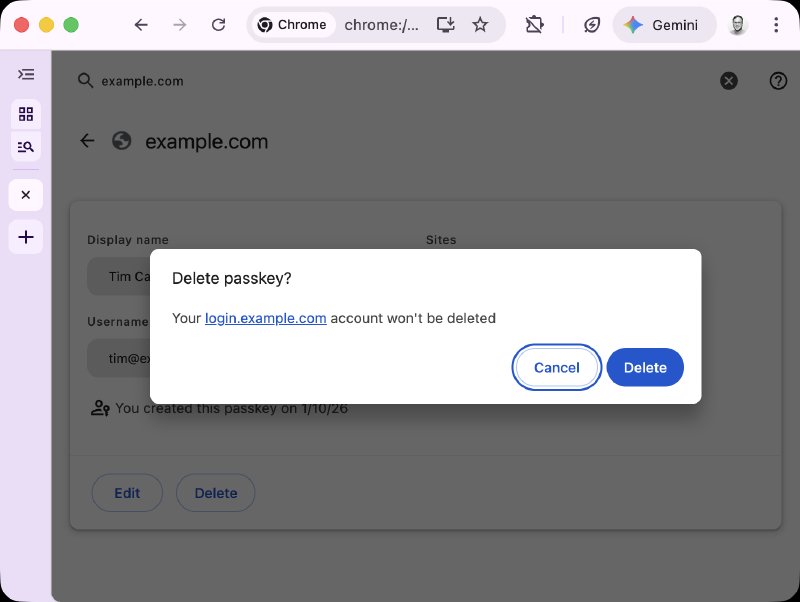 Example: deleting a passkey in Google Password Manager
Example: deleting a passkey in Google Password Manager
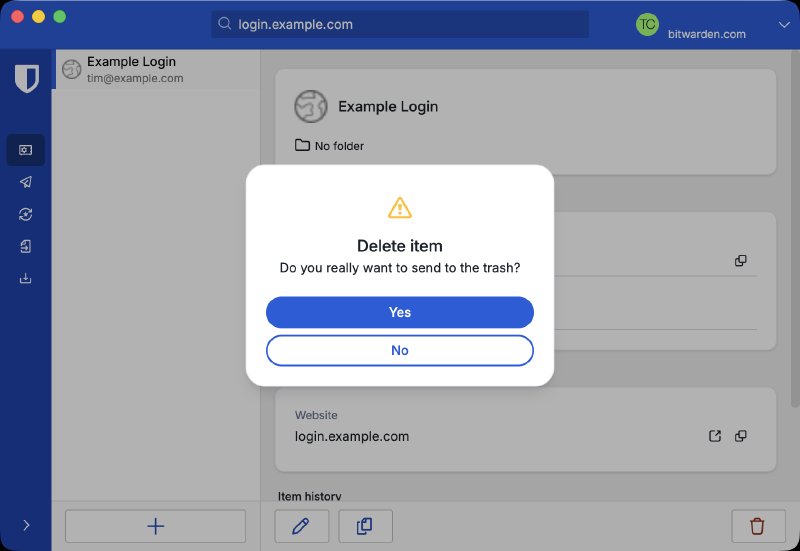 Example: deleting a passkey in Bitwarden
Example: deleting a passkey in Bitwarden
None of these interfaces communicate that deleting the passkey might destroy encrypted data. Users cannot be expected to understand the technical implications or remember them months later when they need their data back.
A Better Path Forward
Passkeys should remain focused on what they do best: providing phishing-resistant authentication. Let them be great at that one thing rather than mediocre at two.
For organizations that still need to use PRF for encryption despite these risks, several mitigations are possible:
- Add prominent warnings when users enable PRF-based encryption
- Create support pages explaining the dual-use nature of passkeys
- List these pages in the Well-Known URL for Relying Party Passkey Endpoints (prfUsageDetails)
- Provide clear warnings when users attempt to delete passkeys with PRF
- Consider alternative encryption key management approaches
The Industry's Responsibility
The identity industry has a responsibility to promote best practices, not just convenient ones. We need to stop treating passkeys as a universal solution and recognize their limitations. Credential managers should prioritize user warnings. Services should be transparent about their use of PRF.
Passkeys represent genuine progress in authentication security. But extending them to data encryption creates more problems than it solves. The cost - irreversible data loss for users - far outweighs the convenience.
Let's keep passkeys focused on authentication and find better solutions for data encryption. Our users' memories, documents, and digital assets depend on it.
Comments
Please log in or register to join the discussion