A concrete example shows how 2‑out‑of‑4 secret sharing combined with Beaver triples lets four friends compute a consensus restaurant score without revealing individual affordability or preference numbers, and without raising the reconstruction threshold.
Beaver Triples Make Private Group Decisions Feasible
Published May 7 2026 – Stoffel Labs
Author: Mikerah Quintyne‑Collins, Founder & CEO
The problem: private scoring for a dinner decision
Four friends – Alice, Ben, Chloe and Stoffel – want to pick a restaurant among three candidates (A, B, C). Each friend rates every restaurant on two private dimensions:
- Affordability (a_{ij}) – how much they can spend (0‑10).
- Desire (f_{ij}) – how much they want to eat there (0‑10).
The friend‑level contribution for friend (i) and restaurant (j) is
[s_{ij}=a_{ij}\cdot f_{ij}]
and the group‑level score for restaurant (j) is the sum
[S_j=\sum_i s_{ij}]
The group wants to reveal only the three (S_j) values (and thus the winner) while keeping every (a_{ij}) and (f_{ij}) secret.
Input data (for illustration)
| Restaurant | Alice (a,f) | Ben (a,f) | Chloe (a,f) | Stoffel (a,f) |
|---|---|---|---|---|
| A | 8,5 | 7,6 | 9,4 | 6,5 |
| B | 6,9 | 8,8 | 7,7 | 5,9 |
| C | 9,3 | 4,7 | 6,6 | 8,4 |
If we multiplied directly, the friend‑level scores would be:
- A: 40, 42, 36, 30 → (S_A=148)
- B: 54, 64, 49, 45 → (S_B=212)
- C: 27, 28, 36, 32 → (S_C=123)
The challenge is to obtain the three (S_j) without ever exposing the individual (a_{ij}) or (f_{ij}).
Secret sharing basics
We use a Shamir‑style (t)-out‑of‑(n) scheme with (t=2) and (n=4). Each secret (x) is encoded as a random degree‑1 polynomial
[p_x(z)=x+\alpha z]
and each participant receives a share (p_x(z_i)) for a distinct public point (z_i). The secret is recovered by any two participants using Lagrange interpolation at (z=0).
Linear operations are trivial:
- Addition: ([x]+[y]=[x+y])
- Scalar multiplication: (a\cdot[x]=[a x])
Multiplication, however, raises the polynomial degree from 1 to 2, which would require three shares to reconstruct – breaking our 2‑out‑of‑4 requirement. Beaver triples provide a way around this.
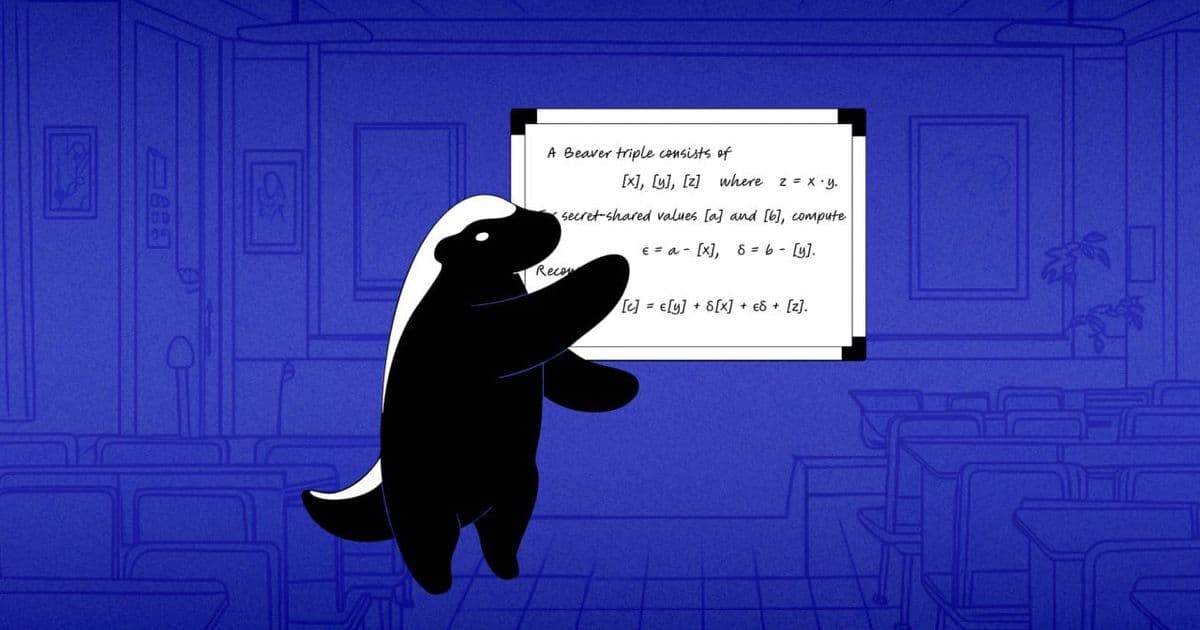
Beaver triples: the core trick
A Beaver triple consists of three correlated secrets ((a,b,c)) with the relation (c = a\cdot b). The parties receive shares ([a]), ([b]) and ([c]) generated offline by a trusted source (or via a distributed randomness protocol). Crucially, each triple is used once and the masks (a,b) are uniformly random.
Multiplication using a triple
Given secret‑shared values ([x]) and ([y]), the parties compute
- ([d] = [x] - [a]) and ([e] = [y] - [b]).
- Open the masks: each participant reveals its share of (d) and (e). Because (a,b) are random, the revealed (d = x-a) and (e = y-b) leak no information about (x) or (y).
- Reconstruct (d) and (e) publicly.
- Compute the product shares using the identity [[xy] = [c] + d\cdot[b] + e\cdot[a] + d\cdot e] where the terms (d\cdot[b]) and (e\cdot[a]) are scalar‑multiplications of a public constant with a secret share, and (d\cdot e) is a public constant.
The resulting shares ([xy]) are still degree‑1 polynomials, so any two participants can later reconstruct the product.
Applying the triple to the dinner example
We need 12 multiplications (one per friend‑restaurant pair). Therefore we pre‑generate 12 fresh Beaver triples ([a_k],[b_k],[c_k]).
Step‑by‑step for Ben’s score at Restaurant B
- Private inputs: (x= a_{B}^{\text{Ben}} = 8), (y= f_{B}^{\text{Ben}} = 8).
- Triple (offline): (a=5,; b=6,; c=30) – only shares ([5],[6],[30]) are distributed.
- Compute ([d] = [8] - [5]) and ([e] = [8] - [6]).
- Open (d=3) and (e=2).
- Form the product shares: [[64] = [30] + 3\cdot[6] + 2\cdot[5] + 3\cdot2] which simplifies to ([64]).
All other friend‑restaurant pairs follow the same pattern, each consuming its own triple.
Aggregating to restaurant scores
Because secret sharing is linear, the group simply adds the 4 friend‑level product shares for each restaurant:
- ([S_A] = [40] + [42] + [36] + [30] = [148])
- ([S_B] = [54] + [64] + [49] + [45] = [212])
- ([S_C] = [27] + [28] + [36] + [32] = [123])
Now any two friends (e.g., Alice and Chloe) reveal their shares of ([S_A],[S_B],[S_C]). Using Lagrange interpolation at (z=0) they reconstruct the three cleartext scores. The winner is Restaurant B with a score of 212.
Why the threshold stays at two
The only public values are the masks (d) and (e) for each multiplication. Since the masks (a,b) are freshly sampled random field elements, (d) and (e) are one‑time pads for (x) and (y). Revealing them does not reduce the secrecy of the underlying inputs, and the degree of the resulting product shares remains 1. Consequently the reconstruction threshold never increases beyond the original 2‑out‑of‑4 setting.
Practical considerations
- Triple generation – In production you would either trust a randomness beacon (e.g., NIST’s DRBG, satellite entropy) or run a distributed generation protocol such as SPDZ preprocessing.
- Communication cost – Each multiplication requires two rounds: (i) exchange of masked shares, (ii) broadcast of (d) and (e). For 12 multiplications the overhead is modest for a small group chat.
- Security model – The protocol is secure against semi‑honest adversaries (participants follow the protocol but may try to learn extra information). With additional MAC checks (as in SPDZ) it can be hardened against malicious behavior.
- Scalability – The same pattern scales to larger groups and more complex functions (e.g., federated averaging) by reusing the linearity of secret sharing and the Beaver‑triple multiplication primitive.
Recap checklist
- Pre‑compute 12 fresh Beaver triples ([a],[b],[c]).
- Secret‑share each (a_{ij}) and (f_{ij}) among the four friends (2‑out‑of‑4).
- For each pair (i,j) perform the triple‑based multiplication to obtain ([s_{ij}]).
- Add the four ([s_{ij}]) per restaurant to get ([S_j]).
- Two designated friends open their shares of ([S_j]) and reconstruct the three scores.
- Pick the restaurant with the highest (S_j).
The raw affordability and preference numbers never leave the owners’ devices, yet the group reaches a unanimous, privacy‑preserving decision.
For more on secret‑sharing‑based MPC, see the MPC Primer and the Beaver triple generation guide.
Comments
Please log in or register to join the discussion