A comprehensive guide to implementing private_key_jwt authentication for connecting Entra External ID to Entra ID, examining the security benefits, technical implementation challenges, and business impact compared to traditional client_secret authentication methods.
The cloud identity landscape continues to evolve with Microsoft's Entra External ID (EEID) platform offering organizations a robust solution for external identity management. Recent technical implementations reveal a significant security enhancement through the adoption of private_key_jwt authentication when connecting EEID to Entra ID as an external provider. This approach fundamentally changes how authentication occurs between these two services, offering substantial security improvements over traditional client_secret methods.
Technical Implementation of Private Key JWT Authentication
The private_key_jwt authentication method represents a shift from shared secrets to asymmetric cryptography, aligning with modern security best practices. Unlike client_secret authentication where a static secret is exchanged between services, private_key_jwt utilizes JSON Web Tokens (JWTs) signed with private keys to authenticate requests to the token endpoint.
The implementation process involves several critical steps:
Key Registration: EEID registers its public key with Entra ID through the JSON Web Key Set (JWKS) endpoint. This establishes the cryptographic foundation for secure authentication.
JWT Construction: EEID creates a JWT with specific claims including issuer (iss), subject (sub), audience (aud), unique identifier (jti), expiration time (exp), and issued-at time (iat). These claims ensure the token's integrity and prevent replay attacks.
Token Signing: The JWT is signed using EEID's private key, with the key ID (kid) header identifying which corresponding public key should be used for verification.
Authentication Request: EEID posts the signed JWT to Entra ID's token endpoint for validation.
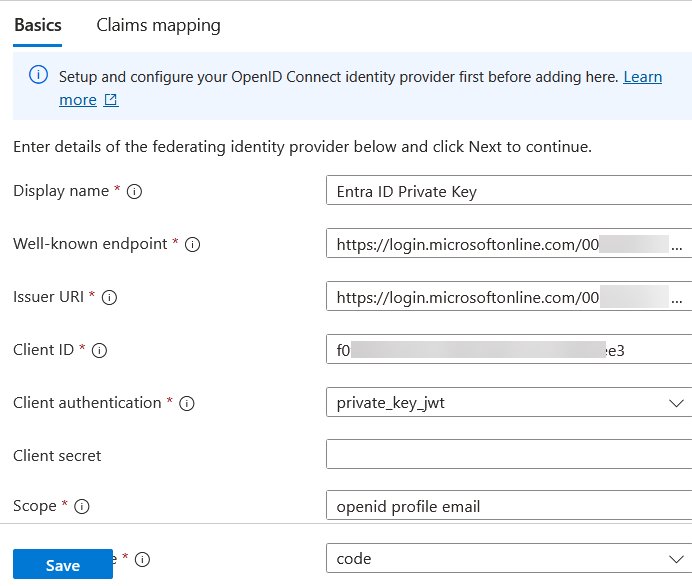 Custom OIDC identity provider configuration with private_key_jwt authentication method
Custom OIDC identity provider configuration with private_key_jwt authentication method
Entra ID then performs several verification steps:
- Looks up EEID's registered public key via JWKS URI or pre-registered key
- Verifies the JWT signature using the corresponding public key
- Validates critical claims including audience, expiration, issuer, subject, and unique identifier
- Issues an access token if all validations pass
Comparative Analysis: Private Key JWT vs Client Secret Authentication
The shift from client_secret to private_key_jwt authentication represents a significant security evolution:
Security Posture:
- Client_secret relies on a shared secret that must be stored securely and transmitted securely
- Private_key_jwt eliminates the need to transmit secrets, reducing attack surfaces
- Private keys remain within EEID's environment, never exposed to external services
Operational Complexity:
- Client_secret implementation is straightforward but requires careful secret management
- Private_key_jwt requires more complex key management and periodic key rotation
- The six-key implementation in EEID adds redundancy but increases maintenance overhead
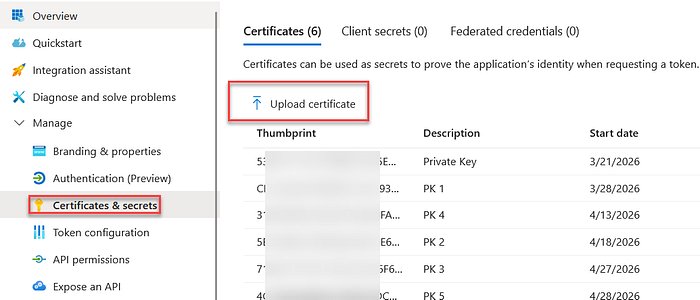 Certificate upload interface in Entra ID application registration
Certificate upload interface in Entra ID application registration
Lifecycle Management:
- Client_secret requires periodic rotation but remains relatively static
- Private_key_jwt keys in EEID have a five-year validity period, reducing rotation frequency
- Key rollover requires coordination between both systems but can be automated
Business Impact and Strategic Considerations
Organizations implementing this enhanced authentication method should consider several strategic implications:
Security Benefits: The elimination of shared secrets reduces the risk of credential theft and unauthorized access. Asymmetric cryptography provides stronger authentication guarantees and aligns with zero-trust security principles.
Compliance Alignment: This approach better satisfies regulatory requirements for secure authentication mechanisms, particularly in industries with stringent data protection requirements.
Operational Considerations: While the implementation requires more technical expertise, the long-term security benefits justify the investment. Organizations should develop standardized processes for key management and certificate handling.
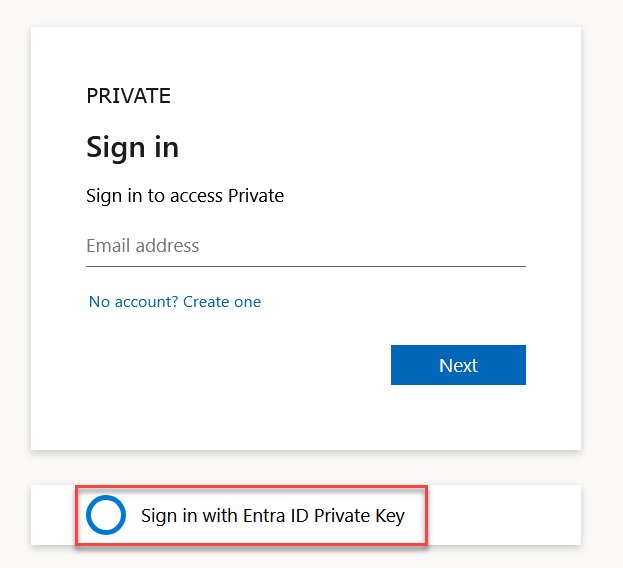 Testing the federation sign-in process with error diagnostics
Testing the federation sign-in process with error diagnostics
Migration Path: Organizations transitioning from client_secret to private_key_jwt authentication should plan for a gradual migration, potentially maintaining both authentication methods during the transition period.
Future-Proofing: As cloud security standards continue to evolve, private_key_jwt authentication positions organizations to meet future requirements without significant architectural changes.
The implementation process, as detailed in Rory Braybrook's technical guide, requires careful attention to certificate formatting and key management. The necessity of uploading all six keys from EEID's JWKS endpoint highlights the importance of redundancy in cloud authentication systems.
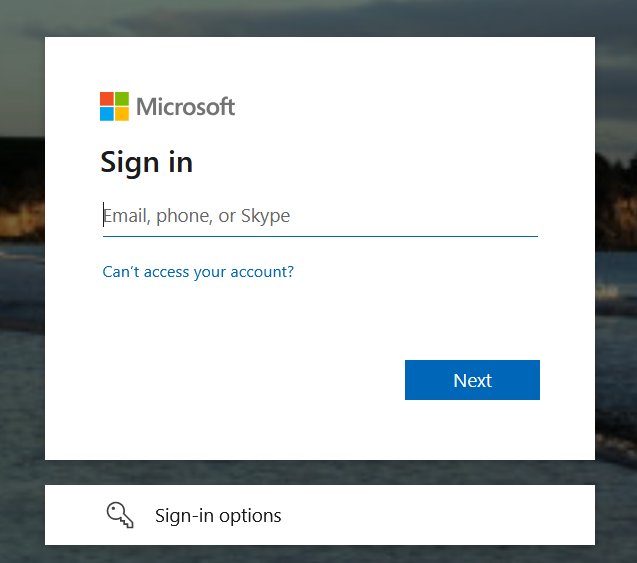 Successful federation sign-in with identity mapping
Successful federation sign-in with identity mapping
For organizations implementing this solution, the Entra External ID documentation provides essential context for the configuration process. The technical implementation, while complex, offers substantial security improvements that justify the operational investment.
As cloud-native ecosystems continue to mature, authentication methods like private_key_jwt will become standard practice, reflecting the industry's broader shift toward cryptographic security models over traditional secret-based authentication. Organizations adopting these practices now will benefit from enhanced security posture and alignment with emerging cloud identity standards.
For detailed implementation instructions, refer to the original technical guide by Rory Braybrook, which provides step-by-step configuration instructions and troubleshooting guidance.

Comments
Please log in or register to join the discussion