Google unveiled Cloud Fraud Defense at Next ’26, extending reCAPTCHA into a full‑stack fraud‑prevention service. The announcement reshapes how enterprises compare managed bot‑defense solutions, influences pricing and migration planning, and forces a rethink of fraud‑mitigation across multi‑cloud environments.
Google Cloud Fraud Defense Replaces reCAPTCHA – What It Means for Multi‑Cloud Security Strategies

What changed?
At Next ’26 Google announced Google Cloud Fraud Defense, the evolution of reCAPTCHA from a simple bot‑challenge widget into a platform that protects login, account‑creation, and payment flows from sophisticated fraud. The service keeps the familiar reCAPTCHA APIs, site keys and pricing model, but adds a risk‑scoring engine that evaluates every request against Google’s global threat intelligence and machine‑learning models.
Key points of the launch:
- Zero‑migration path – existing reCAPTCHA customers are automatically enrolled; no code changes are required.
- Unified risk API – the same
grecaptcha.enterprise.executecall now returns a fraud‑risk score and a set of reason codes that can be used to drive automated policies. - Broader coverage – detection now spans account take‑over, credential stuffing, and AI‑generated identity fraud, not just automated bots.
- Pricing continuity – the first 10 000 assessments per month remain free; usage‑based charges apply beyond that, identical to the current reCAPTCHA model.
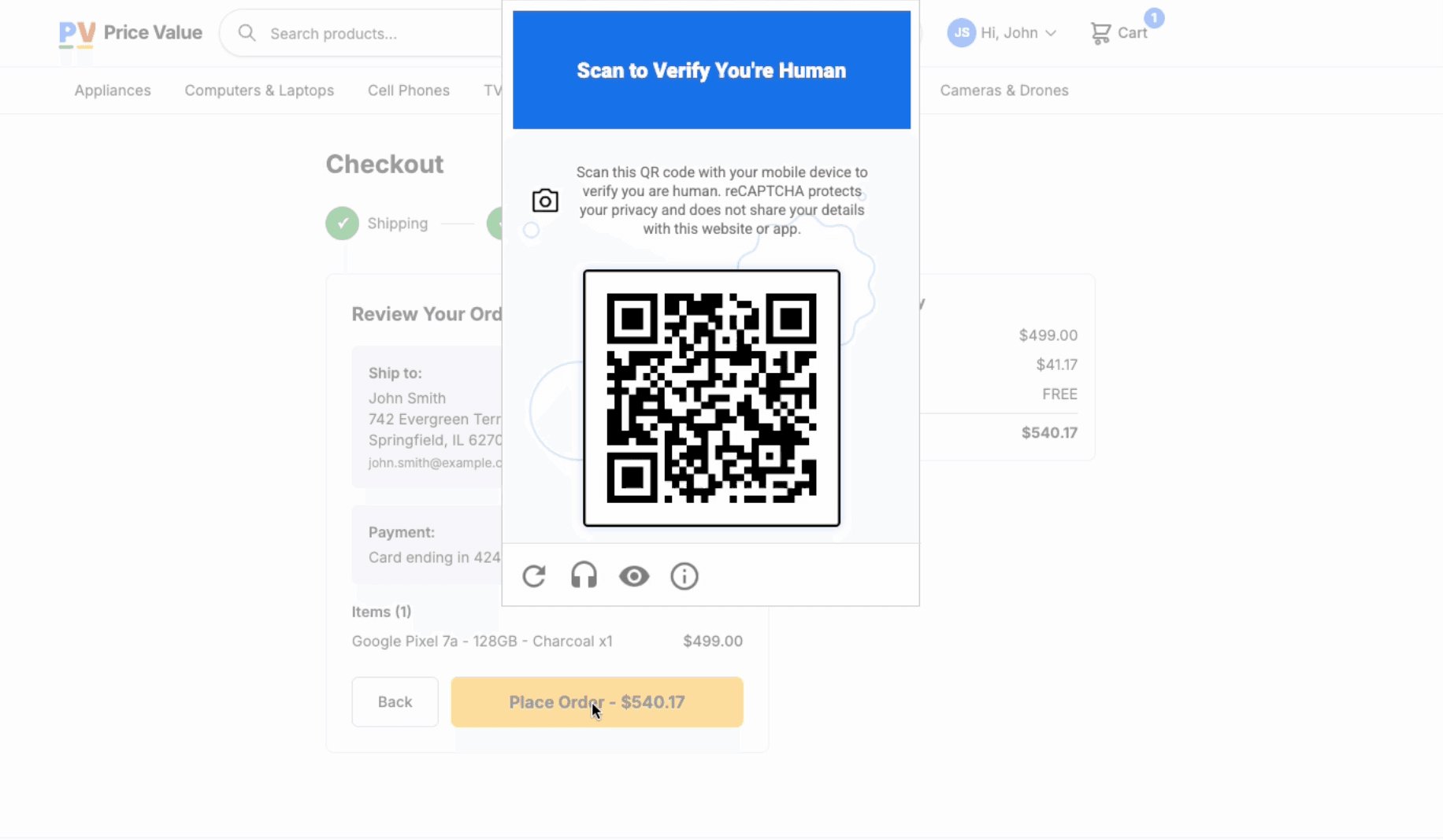
Google frames the shift as a response to the “agentic economy”, where friction kills conversion and attackers exploit large language models to synthesize human‑like behavior. The new platform aims to verify users silently in the background, replacing visual puzzles with invisible risk analysis.
Provider comparison
| Feature | Google Cloud Fraud Defense | Cloudflare Turnstile | AWS WAF + CAPTCHA |
|---|---|---|---|
| Core model | Risk‑score + reason codes via existing reCAPTCHA API | Privacy‑first challenge‑less widget, returns a simple pass/fail token | WAF rule triggers CAPTCHA/Challenge actions; separate API for token validation |
| Signal sources | Global Google threat intel, Chrome Safe Browsing, Safe Search, device fingerprint, interaction telemetry | Browser‑level bot detection, TLS fingerprint, device reputation | IP reputation lists, AWS Shield Advanced signals, custom header inspection |
| AI‑driven fraud detection | ML models trained on billions of requests, includes LLM‑generated traffic patterns | Primarily heuristic + ML on bot behavior, no explicit AI‑agent detection | Relies on rule‑based thresholds; AI features are limited to Shield Advanced alerts |
| Pricing | Free tier 10 k assessments/mo, then usage‑based (same as reCAPTCHA v3) | Free tier 1 M passes/mo, then flat rate per 1 M passes | WAF pricing + per‑request CAPTCHA cost; no free tier for challenge actions |
| Integration effort | Drop‑in replacement for reCAPTCHA; same site key, same client script | New widget script, token verification endpoint | Requires WAF rule creation and optional Lambda@Edge for token validation |
| Data handling | reCAPTCHA now a data processor; customers retain controller responsibilities | No personal data collected beyond token; privacy‑first by design | Data processed within AWS; customers control logs via CloudTrail |
| Multi‑cloud suitability | Works on any origin (GCP, AWS, Azure, on‑prem) as long as API calls are reachable | Cloud‑agnostic; can be embedded on any site | |
| Support for compliance | GDPR‑ready, CCPA, ISO‑27001; Google Cloud’s compliance suite applies | GDPR‑compatible, no PII stored | |
| Developer experience | Same client library (grecaptcha.enterprise), new risk‑score fields in response JSON |
Simple turnstile script, token verification via Cloudflare API |
Pricing and migration considerations
Because Google kept the existing reCAPTCHA pricing tier, the immediate cost impact for most enterprises is negligible. However, the risk‑score API introduces new data points that can trigger downstream automation (e.g., deny login, require MFA, flag transaction). Companies must plan for:
- Policy updates – Map risk thresholds to security actions in IAM, identity‑provider, or payment gateway workflows.
- Observability – Export reason codes to SIEMs (e.g., Splunk, Azure Sentinel) for correlation with other fraud signals.
- Compliance review – Verify that the data‑processor model aligns with internal data‑governance policies, especially for regulated sectors.
- Cost monitoring – Track request volume beyond the free tier; usage can spike during promotional campaigns or bot‑driven attacks.
In contrast, Cloudflare Turnstile offers a higher free quota but lacks the granular reason codes that enable fine‑grained automation. AWS customers may need to combine WAF with custom Lambda functions to emulate similar behavior, which adds operational overhead and can increase latency.
Business impact
Faster conversion, lower friction
By moving verification to the background, Cloud Fraud Defense promises higher conversion rates for e‑commerce and SaaS sign‑ups. Early tests shared by Google’s developer advocate Rasu indicate a 3‑5 % lift in completed registrations when the invisible flow replaces traditional image challenges.
Centralized fraud signal across clouds
Enterprises that run workloads on multiple clouds can now centralize fraud intelligence in a single service. The risk‑score API is reachable from any environment, meaning a microservice on Azure can call the same endpoint used by a GCP‑hosted checkout process. This reduces the need for duplicated bot‑defense tooling and simplifies audit trails.
Shift in security architecture
The introduction of a risk‑score layer encourages a zero‑trust approach to user interactions. Instead of a binary “human vs bot” decision, applications can apply progressive authentication: low‑risk users proceed silently, medium‑risk users receive step‑up challenges, and high‑risk users are blocked or routed to manual review.
Competitive pressure on other providers
Cloudflare’s Turnstile and AWS’s WAF‑based CAPTCHA solutions now face a feature gap: they lack native AI‑driven fraud scoring and the seamless upgrade path that Google offers to its massive reCAPTCHA base. Providers may respond by adding richer risk APIs or by bundling third‑party fraud‑intelligence services.
Migration strategy for existing reCAPTCHA users
- Audit current usage – Identify pages that call
grecaptcha.executeand note any custom score thresholds. - Enable risk‑score logging – Turn on the
debugflag in the client library to capture the newriskScoreandreasonCodesfields. - Define policy thresholds – Start with Google’s recommended low‑risk cutoff (e.g.,
riskScore < 0.3) and adjust based on observed false‑positive rates. - Integrate with existing IAM – Map high‑risk scores to MFA challenges in your identity provider (Okta, Azure AD, etc.).
- Monitor cost – Use the Cloud Billing reports to watch for usage beyond the free tier; set alerts at 80 % of the quota.
Long‑term considerations
- AI‑generated attacks will evolve – As large language models improve, the invisible verification layer must be continuously retrained. Organizations should plan for periodic model‑performance reviews.
- Data‑processor responsibilities – Companies must maintain a clear record of how user data is processed, especially when integrating third‑party analytics.
- Vendor lock‑in risk – While the API remains compatible, the underlying intelligence is Google‑specific. Multi‑cloud strategies may still need a fallback or secondary provider for redundancy.
Bottom line
Google Cloud Fraud Defense turns a ubiquitous widget into a comprehensive, low‑friction fraud‑prevention platform that works across any cloud. For enterprises, the immediate benefit is a painless upgrade path and richer risk data that can be baked into zero‑trust user flows. Compared with Cloudflare Turnstile and AWS’s CAPTCHA‑based approach, Google offers deeper AI‑driven insights and a unified pricing model, but it also concentrates fraud intelligence in a single provider. Companies should weigh the operational simplicity against potential vendor lock‑in, and they must adapt their security policies to exploit the new risk‑score and reason‑code capabilities.
For a deeper dive, watch the breakout session “Preventing Fraud and Abuse: Securing the New Agent Economy” on the Next ’26 YouTube channel and review the official Google Cloud Fraud Defense documentation.

Comments
Please log in or register to join the discussion