Multitude's migration from on-premises databases to Azure Database for PostgreSQL and MySQL demonstrates how financial institutions can achieve scalability, compliance, and operational efficiency in cloud environments.
Multitude's Cloud Migration: Scaling Banking Infrastructure with Azure Database Services
Expanding into new markets typically indicates business success, but for digital banking platforms, growth brings unique technical challenges. More customers, more data, and stricter regulatory requirements create pressure on infrastructure that must remain highly available, secure, and compliant. Multitude, operating across 17 countries with over 400 microservices, faced these challenges head-on by migrating their database infrastructure from on-premises environments to Microsoft Azure's managed database services.
The Challenge: Scaling Banking Infrastructure in Regulated Environments
Multitude delivers digital banking, credit services, payment processing, and regulatory reporting through a platform composed of more than 400 microservices. Each service encapsulates a defined business capability, including onboarding, risk assessment, collections, and compliance workflows. Historically, these services relied on on-premises PostgreSQL and MySQL environments deployed within Multitude's own data centers.
The traditional architecture used vertical scaling on shared compute and storage resources, creating contention between unrelated workloads. This model limited independent scaling capabilities, as expanding capacity required adding or upgrading physical hardware—a process involving demand forecasting, procurement, delivery coordination, and installation. As Multitude expanded across markets, these constraints became increasingly problematic.

In regulated financial environments, these infrastructure limitations carry broader implications. Frameworks such as DORA (Digital Operational Resilience Act) and GDPR require predictable availability, controlled recovery procedures, and governed access to sensitive data. As workload demands increased, sustaining both growth and compliance required structural changes at the database layer.
The Solution: Azure Database Services with Bounded Context Architecture
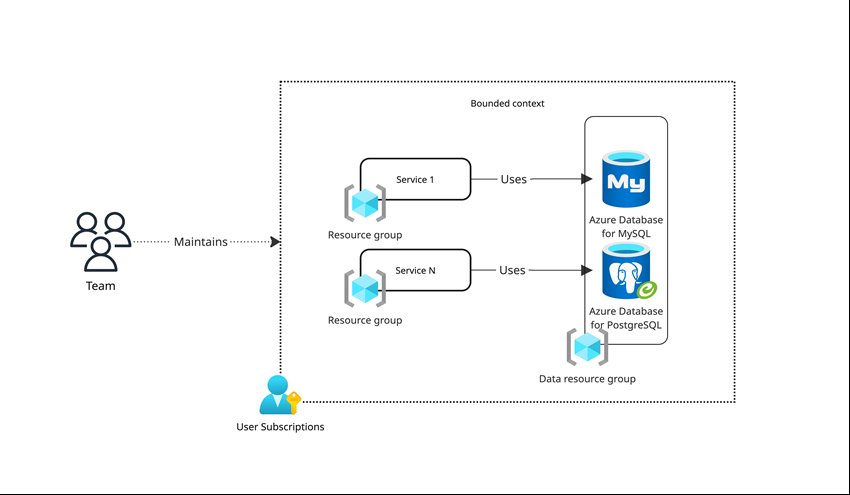
Multitude initiated their architectural redesign by migrating database workloads to Microsoft Azure and standardizing on Azure Database for PostgreSQL and Azure Database for MySQL for core application services. Central to this redesign was the adoption of bounded contexts—a concept where each bounded context represents a logical business domain and encapsulates the services and schemas required to support that capability.
Instead of maintaining a small number of large, shared database instances, Multitude provisioned dedicated database instances aligned to defined business domains, establishing domain-level isolation at the database layer. Today, approximately 35 database instances support more than 400 microservices across the platform. Each instance hosts multiple schemas serving related services within the same domain, while cross-domain database dependencies are intentionally avoided.
This structure limits the blast radius of configuration changes or workload spikes and allows scaling adjustments to be applied within clearly defined domain boundaries. The bounded context model balances domain-level isolation with operational manageability—a database-per-microservice pattern would significantly increase provisioning, monitoring, and lifecycle overhead without materially improving data ownership boundaries.
Technical Implementation: High Availability and Backup Strategy
To support availability requirements, Multitude deployed Azure Database for PostgreSQL and Azure Database for MySQL with zone-redundant high availability, placing primary and standby replicas in separate availability zones within the same Azure region. This replication preserves transactional consistency while zone separation reduces exposure to localized infrastructure failures. The team periodically exercises failover procedures as part of operational validation to confirm recovery behavior under defined conditions.
Availability controls are complemented by a layered backup strategy. Azure Database for PostgreSQL and Azure Database for MySQL provide automated backups with a retention window of up to 35 days and point-in-time restore capabilities. These features allow restoration to a specific timestamp within the retention window, supporting recovery from application-level errors or unintended data modifications without custom snapshot orchestration.
Restore operations require documented justification and follow established approval workflows, ensuring that recovery actions remain controlled, traceable, and auditable. The team also enforces consistency through lifecycle management, as Azure's managed service model standardizes engine patching and version updates across environments, reducing configuration drift.
For migration and synchronization scenarios, Multitude uses Azure Data Migration Service to orchestrate controlled cutovers between database environments. Engineers validate configuration and readiness before initiating synchronization, after which Azure-managed replication maintains data alignment until final switchover. All provisioning decisions and structural modifications remain subject to internal governance approvals to preserve change control and oversight.
Compliance by Design: Identity Integration and Governance
In regulated financial environments, governance must be embedded directly into platform operations. Multitude achieves this by integrating Azure Database services with Microsoft Entra ID, aligning database authentication with centrally managed corporate identities. Role-based access control is enforced through enterprise identity policies, providing centralized visibility into access assignments and authentication events across environments.
The team extends these controls into production access management, implementing approval-based, time-bound privileged access with no permanently assigned administrative roles. Access requests follow defined workflows, and all privileged actions are logged for review under established oversight procedures.
Database isolation reinforces these identity controls. By aligning database instances with bounded contexts, each business domain maintains a discrete data boundary at the database layer. This structure limits lateral access across domains and confines sensitive data to clearly defined ownership scopes, simplifying monitoring and audit review. These architectural controls support compliance requirements under frameworks such as DORA and GDPR.
Business Impact: From Operational Overhead to Strategic Focus
The migration to Azure Database services has transformed Multitude's operational capabilities. Previously, expanding database capacity meant procuring hardware and planning installation in the data center—a process taking weeks or months. Now, capacity adjustments happen directly within Azure and can be applied to individual database instances, allowing near real-time scaling as workload demands change.
Maintenance effort has decreased significantly. Managed patching, version alignment, and automated backups have reduced the need for manual coordination and reactive capacity management. Infrastructure-level tasks that once required continuous oversight are now handled within the managed service boundary. As a result, Multitude's database administrators can focus on improving performance and stability rather than maintaining basic infrastructure.
The architectural changes reflect a deliberate long-term strategy. Multitude's database architecture now aligns with the operating model they expect to sustain over the next five years and beyond. With bounded contexts defining discrete data domains and Azure Database services providing managed high availability, scaling controls, and standardized lifecycle management, the company scales responsibly in regulated markets while maintaining strict governance and availability standards.
Provider Comparison: Azure vs. On-Premises for Financial Services
When evaluating database infrastructure options, financial institutions must consider several factors beyond raw performance. The on-premises approach that Multitude previously used offers maximum control but comes with significant operational overhead. Capacity planning requires forecasting needs months in advance, hardware procurement involves vendor selection and logistics, and maintenance requires dedicated personnel.
Cloud providers like Microsoft Azure offer contrasting advantages. With Azure Database for PostgreSQL and Azure Database for MySQL, Multitude gained:
- Elastic scalability: Resources can be adjusted based on actual demand rather than projected needs
- Reduced operational overhead: Managed services handle patching, backups, and maintenance
- Built-in compliance features: Azure services offer controls aligned with financial regulations
- Geographic distribution: Azure's global presence supports Multitude's multi-country operations
- Cost efficiency: Pay-as-you-go pricing reduces capital expenditure and aligns costs with actual usage
For financial institutions evaluating similar migrations, the decision often comes down to control versus agility. On-premises solutions provide maximum control but at the cost of slower response to changing requirements. Cloud solutions offer agility and reduced operational burden while providing sufficient controls for regulated environments when properly configured.
Migration Considerations for Financial Institutions
Organizations considering similar migrations should focus on several key areas:
- Domain boundary definition: Clearly identify business domains and map them to appropriate database instances
- Identity integration: Plan how database authentication will integrate with existing identity management systems
- Compliance alignment: Ensure that cloud configurations meet regulatory requirements for data residency, access control, and auditability
- Operational procedures: Develop new procedures for monitoring, alerting, and incident response in the cloud environment
- Team skills: Assess and address any skills gaps in cloud database administration
For Multitude, the migration represented not just a technology change but a shift in operational philosophy—from infrastructure ownership to service consumption. This transformation required changes in team responsibilities, skills development, and operational procedures.
Conclusion: Cloud as a Strategic Enabler
Multitude's migration demonstrates how cloud database services can enable growth in regulated industries. By adopting Azure Database for PostgreSQL and MySQL with bounded context architecture, the company achieved the scalability needed for expansion while maintaining the governance and compliance required in financial services.
The key to success lies in treating cloud migration not as a simple lift-and-shift exercise but as an opportunity to rethink data architecture. By aligning technical boundaries with business domains and leveraging managed services for operational efficiency, organizations can build infrastructure that supports both current needs and future growth.
For financial institutions considering similar journeys, the message is clear: cloud database services can provide the agility, scalability, and compliance controls needed to thrive in today's rapidly evolving financial landscape. The challenge lies not in the technology itself, but in designing an architecture that aligns technical capabilities with business requirements while maintaining the rigorous standards expected in regulated environments.

Comments
Please log in or register to join the discussion