Security researchers have identified three malicious versions of the popular Node.js package node-ipc that contain sophisticated stealer malware targeting developer credentials and cloud secrets.
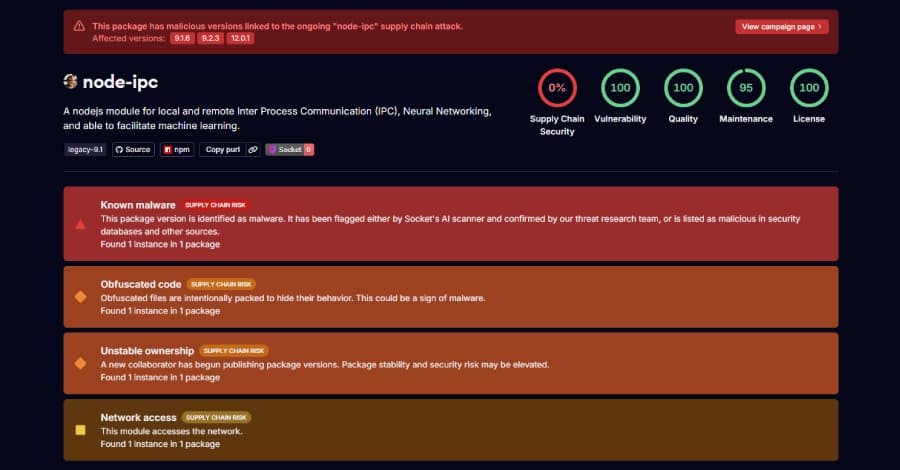
Security researchers at Socket and StepSecurity have discovered a sophisticated supply chain attack targeting developers through three malicious versions of the widely-used npm package node-ipc. The compromised versions—9.1.6, 9.2.3, and 12.0.1—contain a stealer/backdoor that harvests developer secrets and cloud credentials, with potentially devastating consequences for affected organizations.
The Discovery
"Early analysis indicates that [email protected], [email protected], and [email protected] contain obfuscated stealer/backdoor behavior," explained Socket researchers in their analysis. "The malware appears to fingerprint the host environment, enumerate and read local files, compress and chunk collected data, wrap the payload in a cryptographic envelope, and attempt exfiltration through a network endpoint selected via DNS/address logic."
The compromised versions were published by an account named "atiertant," which has no connection to the package's original author, "riaevangelist." Although "atiertant" appears in the maintainer list, the account has no prior publish history with the node-ipc package. The previous legitimate update to the package was in August 2024, indicating a 21-month dormant period before this compromise.
Technical Analysis of the Malware
The malicious payload is triggered when the package is required at runtime, attempting to exfiltrate a broad set of developer and cloud secrets to an external command-and-control (C2) server. According to StepSecurity, the harvested data includes 90 categories of credentials, including:
- Amazon Web Services, Google Cloud, Microsoft Azure credentials
- SSH keys and Kubernetes tokens
- GitHub CLI configs and development environment settings
- Claude AI and Kiro IDE settings
- Terraform state files
- Database passwords
- Shell history files
The harvested data is compressed into a GZIP archive and transmitted to the "sh.azurestaticprovider[.]net" domain—a domain impersonating Azure services to evade detection.
Sophisticated Delivery Mechanism
What makes this attack particularly concerning is its sophisticated delivery mechanism. Unlike typical malicious npm packages that rely on lifecycle hooks like preinstall, install, or postinstall scripts, this attack appends the malicious payload as an Immediately Invoked Function Expression (IIFE) to the end of "node-ipc.cjs."
"This means the malware fires unconditionally on every require('node-ipc')," explained Sai Likhith, a researcher at StepSecurity. "The payload performs a SHA-256 fingerprint check and compares it against a hard-coded hash assembled from eight obfuscated table fragments embedded in the code."
The 12.0.1 version includes an additional targeting mechanism:
"12.0.1 is entirely inert on any machine whose primary module path does not hash to the target value," Likhith noted. "The attacker knows exactly which project or developer is being targeted and pre-computed the hash of their entry point before publishing. The 9.x versions do not have this gate and will execute the full payload on any system that loads them."
Stealthy Exfiltration Techniques
The malware employs multiple exfiltration channels to bypass security controls. Besides the HTTPS POST to the fake Azure domain, it also uses a DNS-based exfiltration technique:
"It first resolves sh.azurestaticprovider.net using 1.1.1.1 (primary) or 8.8.8.8 (fallback) to obtain the C2 IP," StepSecurity explained. "Then it re-targets the resolver directly at the C2 IP for all exfiltration queries."
This DNS sinkhole technique is particularly stealthy:
"The direct-to-C2 DNS sink is a notable anti-detection technique," the researchers noted. "Because the exfiltration queries never touch public DNS resolvers, there is no observable bt.node.js activity in public DNS logs. Organizations relying solely on DNS logging through corporate resolvers would not see this traffic."
Additionally, the malware attempts to maintain persistence by forking itself into detached background child processes, allowing exfiltration to continue even after the parent application terminates.
Broader Implications
"This campaign reflects how software supply chain attacks are evolving beyond simple malicious packages into infrastructure-aware credential harvesting operations," said Avital Harel, security research lead at Upwind. "Attackers are increasingly targeting the identities and automation systems powering modern software delivery pipelines while designing malware specifically to blend into normal developer and application behavior."
This isn't the first time node-ipc has been compromised. In March 2022, the maintainer deliberately introduced destructive capability to versions 10.1.1 and 10.1.2 by overwriting files on systems in Russia or Belarus as a political protest. Subsequent versions included a "peacenotwar" dependency with similar motivations.
"The latest incident appears to involve a suspicious republishing or reintroduction of malicious code into versions of a known package, rather than a typosquatting attempt," Socket researchers noted.
Recommended Actions
For developers and organizations that may have been affected by this compromise, security experts recommend the following immediate actions:
- Remove compromised versions: Uninstall node-ipc versions 9.1.6, 9.2.3, and 12.0.1 immediately
- Reinstall clean versions: Install known clean versions (9.2.1 and 12.0.0)
- Assume compromise and rotate credentials: Rotate all potentially exposed credentials and secrets
- Audit npm publish activity: Review npm publish logs for any packages accessible with the rotated tokens
- Review workflow logs: Check CI/CD pipeline run logs for suspicious activity
- Audit cloud logs: Examine cloud logs for unauthorized actions by IAM identities whose credentials were available during the compromised window
- Block egress traffic: Implement network controls to block traffic to the C2 domain (sh.azurestaticprovider[.]net)
The discovery highlights the ongoing challenges in securing software supply chains, particularly as attackers increasingly target developer environments and automation systems that form the backbone of modern software development and deployment processes.
Comments
Please log in or register to join the discussion