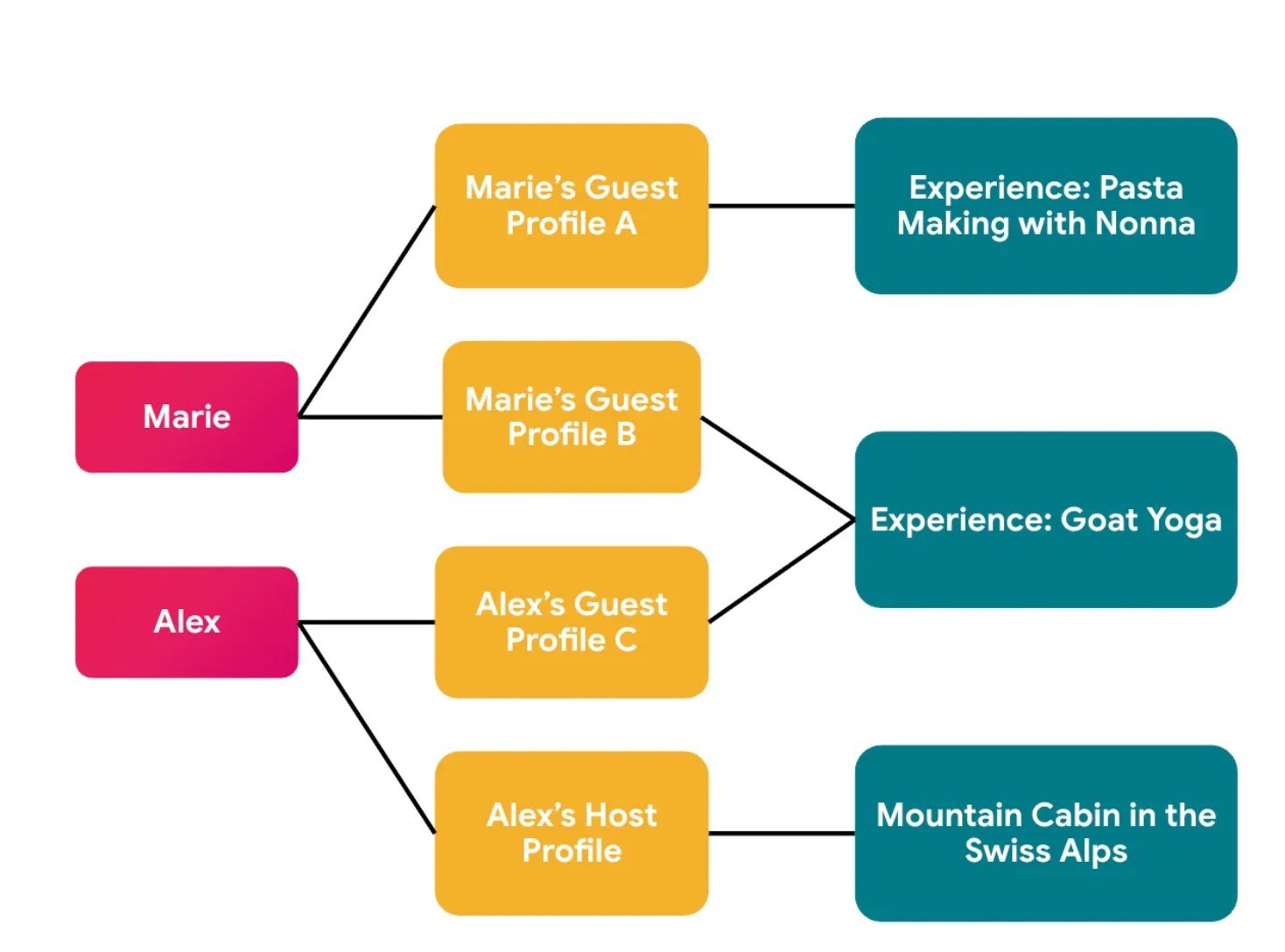
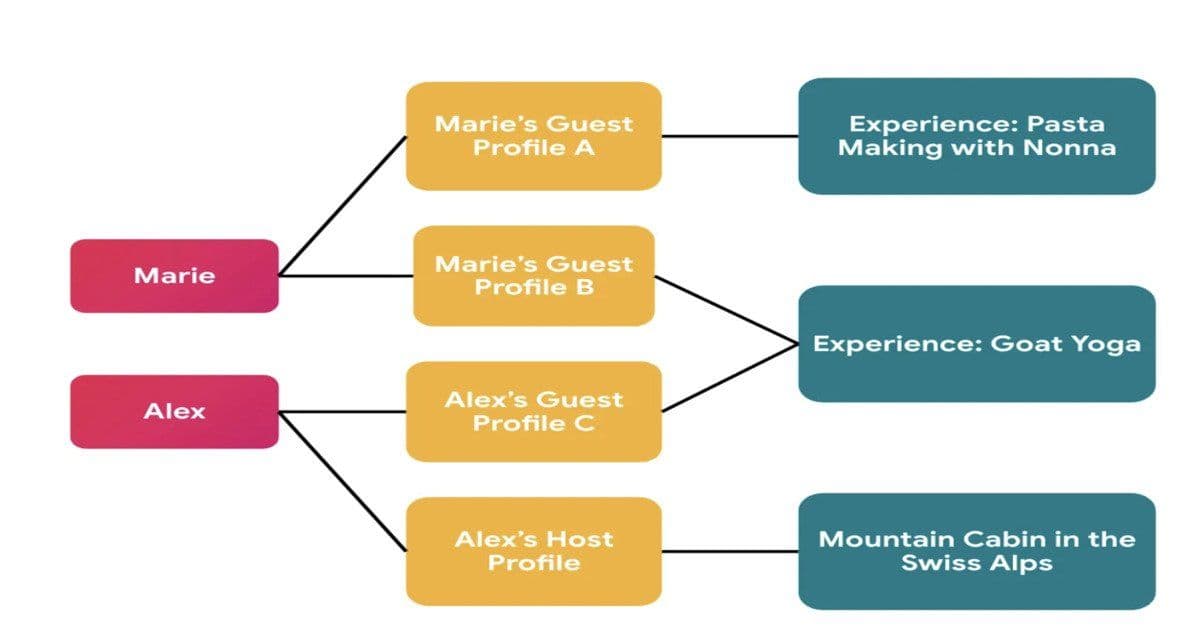
Airbnb has re‑architected its identity layer, separating internal user IDs from context‑specific public profiles. The new model, enforced by the Himeji authorization service, lets participants interact in Experiences without exposing a global identity, while providing clear trade‑offs around complexity, latency, and data governance.
Airbnb Deploys Context‑Aware Identity Model for Privacy‑First Social Experiences
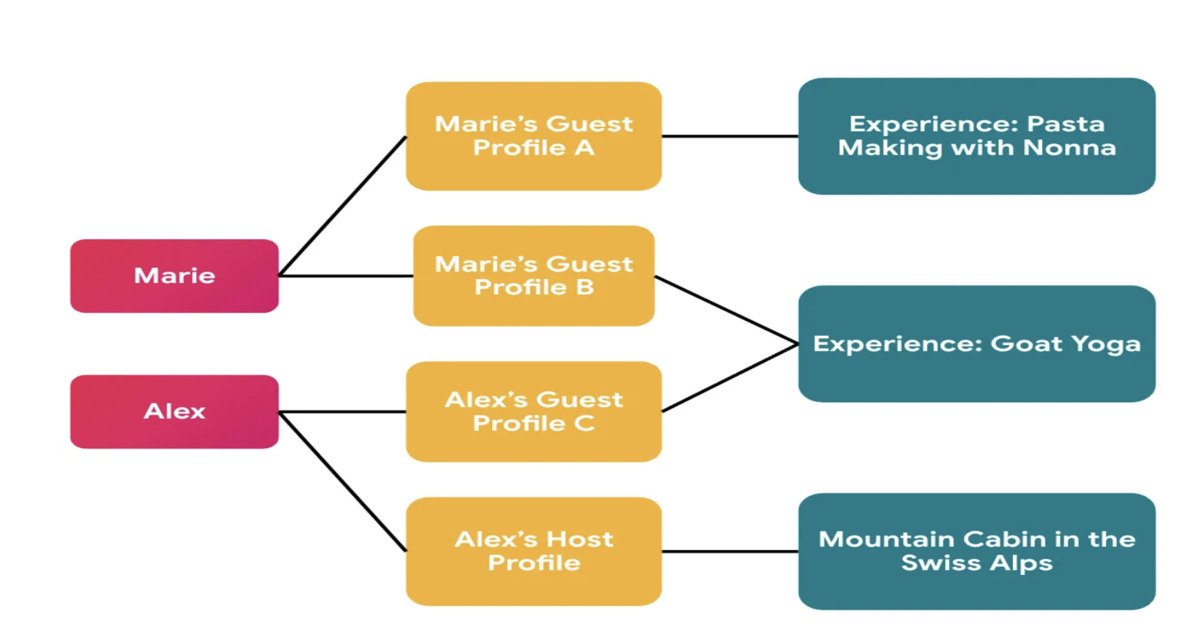
Airbnb announced a major redesign of its identity and connection subsystem to support the next generation of social features in Experiences. The core change replaces a single, platform‑wide user profile with a set of context‑specific profiles that exist only within the boundaries of a given Experience (e.g., a cooking class, a city tour, or a virtual workshop). This shift is driven by the need to keep participants’ personal data isolated when they join activities with strangers, while still enabling rich interaction patterns such as messaging, reviews, and shared media.
Service update – what changed?
| Component | Old behavior | New behavior |
|---|---|---|
| User identifier | Global UUID (user_id) used everywhere, exposed through APIs and UI. |
Internal UUID (internal_id) stays private; each Experience gets a scoped profile ID (exp_profile_id). |
| Profile storage | Single users table with global attributes. |
Separate exp_profiles table linked to the internal user and the Experience ID. |
| Authorization | UI‑level checks; occasional back‑end guards. | Runtime relationship‑based policies in Himeji (Airbnb’s internal RBAC/ABAC engine). |
| Data exposure | Global profile visible to any service that requests it. | Profile data returned only when the requester shares the same Experience context. |
The migration was orchestrated with a combination of static code analysis, automated audit tooling, and AI‑assisted refactoring. Airbnb published the full migration guide on its engineering blog: airbnb.com/engineering/context‑aware‑identity.
Use cases enabled by the new model
- Private group chats for a weekend getaway – Participants can exchange messages without revealing their full Airbnb profile. The chat service queries Himeji to confirm that both users belong to the same
experience_idbefore returning any profile fields. - Dynamic review attribution – After an Experience, the system can show a reviewer’s name only to other attendees of that same event, preserving anonymity for the broader platform.
- Cross‑service analytics – Marketing can aggregate engagement metrics per Experience without ever linking back to a global user ID, satisfying GDPR‑style data minimisation.
- Third‑party integrations – Partners that embed Airbnb Experiences (e.g., a travel portal) receive a token that maps to the scoped profile, not the global account, reducing the risk of data leakage.
These patterns illustrate how context‑driven identity can unlock social interaction while keeping privacy guarantees intact.
Trade‑offs and architectural considerations
| Aspect | Benefit | Cost / Complexity |
|---|---|---|
| Privacy | Users cannot be tracked across unrelated Experiences. | Requires careful propagation of internal_id for internal services that still need a global view (e.g., fraud detection). |
| Performance | Authorization checks are localized; Himeji can cache relationship graphs per Experience. | Additional lookup to resolve exp_profile_id → internal_id adds a hop for services that need the full identity. |
| Data consistency | Scoped profiles are updated only within the context, reducing accidental cross‑contamination. | Migration of existing data needed; legacy accounts were back‑filled with per‑Experience rows, increasing storage footprint. |
| Developer experience | Clear contract: If you need a global view, request internal_id; otherwise work with the scoped profile. |
Teams must audit all code paths that previously assumed a single user object, which can be error‑prone. |
| Governance | Auditing is centralized in Himeji, making policy changes auditable and versioned. | Himeji policies become a critical piece of the stack; any outage impacts many services. |
Airbnb mitigated the latency impact by deploying a relationship cache inside Himeji that stores the set of active Experience IDs per user for the last 24 hours. Cache miss rates dropped from 12 % to under 2 % after the rollout, according to internal metrics shared in the blog post.
Migration tooling and lessons learned
- Static analysis – A custom linter scanned the monorepo for any reference to
global_user_profile. The tool emitted a CSV of file paths and line numbers, which was fed into a ticketing system for owners. - AI‑assisted refactoring – Airbnb leveraged an internal LLM that suggested code patches, automatically replacing
user.profilewithexperience.getProfile(user)where appropriate. Engineers reviewed each suggestion, achieving a 30 % reduction in manual edit time. - Human‑in‑the‑loop validation – Before any change reached production, a cross‑functional review board (engineering, privacy, legal) signed off on the impact assessment. This step prevented accidental exposure of personally identifiable information (PII) during early testing.
The overall effort spanned three quarters and involved over 40 teams. The final rollout was staged by region, with real‑time monitoring of Himeji policy violations via the internal observability platform.
What this means for the broader cloud‑native community
Airbnb’s approach demonstrates a practical way to embed privacy as a first‑class concern in a large, event‑driven platform. By moving identity enforcement from the UI layer down to the data‑access layer, the company achieves consistent guarantees without scattering checks across dozens of microservices. The pattern aligns well with managed services such as AWS IAM Identity Center, Google Cloud Identity-Aware Proxy, and emerging relationship‑based access control (ReBAC) offerings.
Developers building similar social or marketplace experiences can take the following pointers:
- Model identity as a first‑class resource – Treat the profile itself as an entity that can have its own ACLs.
- Separate internal and external identifiers – Keep a stable, private key for backend logic and expose only context‑bound tokens.
- Centralize policy evaluation – A dedicated authorization service (like Himeji) reduces duplication and simplifies audits.
- Invest in migration automation – Static analysis combined with AI‑driven code suggestions can accelerate large‑scale refactors while keeping risk low.
Airbnb’s next steps include extending the model to host‑to‑host interactions and exploring zero‑knowledge proofs for verifying participation without revealing identities at all.
For a deeper dive into the technical details, see the official blog post and the open‑source audit tooling repository:
Comments
Please log in or register to join the discussion