Amazon Web Services is revolutionizing networking with proprietary hardware and software that not only improves performance but also enhances security and privacy protections for global customers.
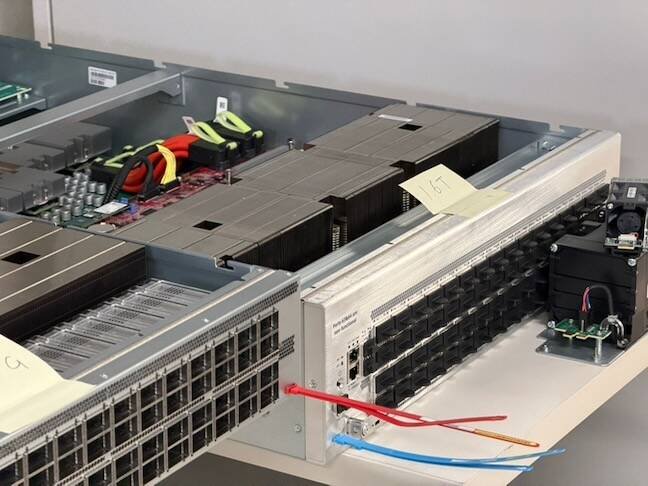
In an unassuming three-story office building in Cupertino, California, engineers from Amazon Web Services are working to make networking so seamless and reliable that it becomes virtually invisible to users. This "invisible network" approach represents not just a technical achievement but a significant advancement in data protection and regulatory compliance for the cloud giant.
"A network should be like a light switch," said Matt Rehder, VP of global network engineering at AWS, during a recent tour of AWS's Torre Avenue lab. "It should be something that just works. No one really cares about the network at the end of the day. It serves a function. You care about it when it's broken. But otherwise you want it to be out of your way."
This philosophy of making networking "disappear" has profound implications for data protection and privacy compliance. By controlling both the hardware and software stack, AWS can implement security measures that would be impossible with third-party networking equipment, potentially helping customers meet stringent regulatory requirements like GDPR and CCPA.

The Security Imperative Behind Vertical Integration
AWS's decision to develop its own networking technology wasn't initially driven by security concerns but by scalability limitations. In 2010, James Hamilton, SVP and distinguished engineer at Amazon, declared that "Datacenter Networks are in my Way." The vertically integrated networking stack of the time was slowing innovation and keeping margins high for network equipment manufacturers.
"This was in the very early days of the cloud," Rehder explained. "But even at that time, with the growth of bandwidth we were seeing, it was very clear that the way networks had been built wasn't going to scale into the future and that something fundamentally different had to happen."
However, as the cloud evolved, security and privacy concerns became increasingly important. By controlling the entire networking stack, AWS can implement end-to-end encryption, secure monitoring, and rapid patching capabilities that provide stronger data protection for customers.
"From a security perspective, it means the code's all ours," Rehder emphasized. "We can scan it, we can fix bugs … we can patch and update our devices very, very regularly."
Unified Hardware Approach Strengthens Security Posture
nWhat sets AWS apart from other network providers is its unified hardware approach. While most network providers use different types of switching ASICs for their aggregation, core, and border networks, AWS uses a single ASIC for everything.
"They would all use different silicon for different switches," Rehder said. "We use one for everything."
This approach, while technically challenging, provides significant security advantages. By maintaining a consistent hardware platform, AWS can implement standardized security measures across its entire network, reducing the attack surface and making it easier to identify and address vulnerabilities.
"If you have one thing and you overly invest in making it really good, you're putting all of your energy into that hardware and software making it super-reliable," Rehder explained. "It also helps us scale the network because when we're managing our supply chain or figuring out to scale, we're not trying to balance all these competing SKUs."
High-Precision Time Synchronization for Enhanced Security
nOne of AWS's most significant networking innovations is its high precision time network, which requires unique hardware and software that integrates with the company's Nitro server chip. This technology, which ensures microsecond-level timing synchronization across servers, has important security implications.
"The bigger problem we're trying to solve is how do we keep all the server clocks in sync," said Satish Vangala, director of network product development at AWS. "We had to build a dedicated network to ensure that we have the timing synchronization at microsecond accuracy for all the servers in our datacenter."
Precise time synchronization is critical for security applications like fraud detection, log analysis, and digital forensics. Under regulations like GDPR and CCPA, organizations must be able to demonstrate comprehensive audit capabilities, and precise timestamping is essential for this.
Scaling Infrastructure for Compliance and Performance
nAWS's networking infrastructure now includes about two million devices, 50-60 million optical links, and 20 million kilometers of terrestrial and subsea fiber. This massive scale presents both challenges and opportunities for data protection.
"We do have hollow core fiber deployed in a few places now," Rehder said. "It's more expensive than the traditional fiber. But if it enables us to improve latency or better serve customers, in the grand scheme of things, the cost of the fiber is small when you look at the entire cost of datacenters, servers and network devices and everything else."
The reduced latency provided by hollow core fiber (30% less than traditional fiber) allows AWS to implement more granular security monitoring and response capabilities. When data travels faster between points, security teams can detect and respond to threats more quickly, potentially limiting the scope of data breaches.
As generative AI services have accelerated bandwidth demands, AWS has developed solutions like the UltraCluster network, which reduces the number of networking devices in the path between servers. This not only improves performance but also reduces potential security vulnerabilities by minimizing the attack surface.
Reliability as a Security Feature
nAWS's focus on network reliability has significant implications for data protection. When networks fail, data can be lost, corrupted, or exposed. By building extremely reliable networking infrastructure, AWS helps protect customer data from these risks.
"That's a big area of focus for us – not only building all this capacity but making sure it can be built quickly and then, once it's built, it runs extremely reliably," Rehder said.
One innovation AWS has developed is the "firefly" connector, which verifies fiber signal paths to ensure they're clean before customer connections are made. This attention to detail helps prevent data transmission errors that could compromise data integrity or security.
Implications for Regulatory Compliance
nFor organizations subject to data protection regulations like GDPR, HIPAA, or CCPA, AWS's networking approach offers several compliance advantages:
Enhanced Data Protection: By controlling the entire networking stack, AWS can implement stronger encryption and security measures that help protect customer data both in transit and at rest.
Improved Audit Capabilities: The high precision time synchronization and comprehensive monitoring capabilities make it easier for organizations to demonstrate compliance with audit requirements.
Faster Incident Response: The reduced latency and improved reliability enable quicker detection and response to security incidents, potentially limiting the scope of data breaches.
Consistent Security Posture: The unified hardware approach allows AWS to implement standardized security measures across its entire network, reducing the risk of inconsistent security configurations.
The Future of Invisible Networking
nAs AWS continues to develop its networking technology, the company is focusing on increasing capacity while maintaining reliability and security. The next generation of AWS switches will provide 102.4 terabits per second via 64 ports running at 1.6 terabits per second.
"We're still using the same hardware and we're using the same software," Rehder explained, "but we're packaging it together in a different way" to meet the growing bandwidth demands of services like generative AI.
For customers concerned about data protection and regulatory compliance, AWS's approach to networking represents a significant advancement. By making networking "disappear" – making it so reliable and seamless that users don't need to think about it – AWS is not just improving performance but also creating a more secure foundation for cloud services.
As data protection regulations continue to evolve and become more stringent, the ability to control and secure the entire networking stack will become increasingly important. AWS's investment in proprietary networking technology positions the company well to meet these challenges while providing customers with the performance and reliability they expect.

Comments
Please log in or register to join the discussion