VECT 2.0 ransomware contains a critical flaw in its nonce handling that causes it to permanently destroy large files rather than encrypting them, rendering the ransomware effectively useless as an extortion tool but potentially more damaging as a data wiper.
Researchers are warning about a critical flaw in the VECT 2.0 ransomware that causes it to act as a data wiper for large files rather than properly encrypting them. The vulnerability stems from how the ransomware handles encryption nonces, leading to permanent data loss for files above 128KB.
Technical Flaw Explained
The VECT 2.0 ransomware contains a fundamental flaw in its encryption logic that affects how it processes larger files. According to Check Point researchers, the ransomware attempts to increase encryption speed for larger files by using a single memory buffer for nonce output during chunk encryption.
"Because all chunk encryptions use the same memory buffer for the nonce output, each new nonce overwrites the previous one," explained Check Point security researchers in their analysis. "Once all chunks are processed, only the last nonce generated remains in memory, and only that one is written to disk."
This design flaw means that only the final 25% of large files remains recoverable, while the preceding three quarters of the file become permanently inaccessible. The lost nonces aren't transmitted to the attackers either, creating an unrecoverable situation even for victims who pay the ransom.

Wider Impact
The implications of this flaw extend beyond simple encryption failure. Since most valuable enterprise files—including virtual machine disks, database files, and backups—exceed the 128KB threshold, VECT's impact as a data wiper can be catastrophic in most environments.
"At a threshold of only 128 KB, smaller than a typical email attachment or office document, what the code classifies as a large file encompasses not just VM disks, databases, and backups, but routine documents, spreadsheets, and mailboxes," Check Point noted. "In practice, almost nothing a victim would care to recover falls below this boundary."
Cross-Platform Vulnerability
The researchers discovered that the same nonce-handling flaw exists across all variants of VECT 2.0, including Windows, Linux, and ESXi versions. This means the data-wiping behavior applies consistently regardless of the targeted platform, making the ransomware particularly dangerous across diverse IT environments.
Threat Group Connections
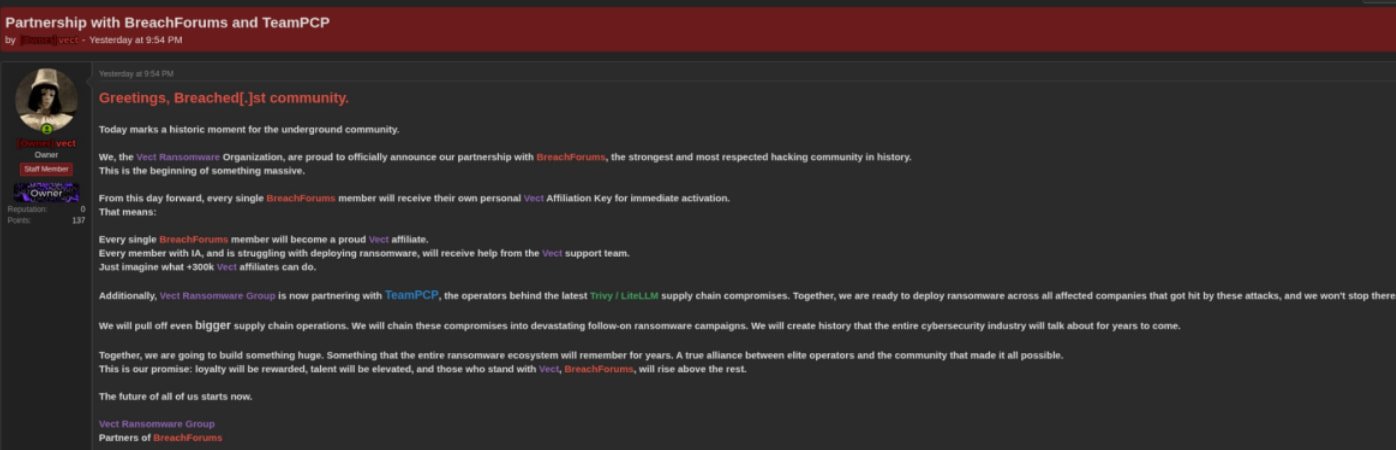
VECT has been actively advertised on BreachForums, with operators inviting registered users to become affiliates and distributing access keys via private messages. The ransomware's operators have also announced a partnership with TeamPCP, the threat group responsible for recent supply-chain attacks impacting Trivy, LiteLLM, Telnyx, and even the European Commission.
In their announcements, VECT operators stated their goal was to exploit victims of those supply-chain compromises, deploying ransomware payloads in their environments, as well as conducting larger supply-chain attacks against other organizations.
Practical Implications for Organizations
For organizations, this flaw presents both challenges and opportunities. On one hand, the ransomware's ineffectiveness as an encryption tool might reduce its attractiveness to cybercriminals. On the other hand, its behavior as a data wiper could be intentionally leveraged in destructive attacks where data destruction is the primary goal.
Security experts recommend maintaining robust backup solutions and implementing comprehensive detection mechanisms for ransomware activity, including monitoring for unusual file modifications and encryption patterns. Regular testing of backup restoration procedures remains critical, as the data destruction capabilities of flawed ransomware like VECT 2.0 could render recovery attempts challenging.
Organizations should also remain vigilant about supply-chain security, given VECT's connections to TeamPCP and their history of targeting software dependencies and third-party vendors.
The discovery of this flaw underscores the importance of thorough security testing for all software, including malicious code. Ironically, a ransomware designed to extort victims through encryption has been rendered ineffective by its own implementation errors, potentially shifting the threat landscape toward more destructive data-wiping capabilities.

Comments
Please log in or register to join the discussion