Application security firm Checkmarx confirms that the LAPSUS$ threat group leaked data stolen from its private GitHub repositories after gaining access through a Trivy supply-chain attack.
Application security company Checkmarx has confirmed that the LAPSUS$ threat group leaked data stolen from its private GitHub repository, marking another significant breach in the software supply chain security landscape.
The investigation, though ongoing, indicates that the access vector was the Trivy supply-chain attack attributed to the hacker group known as TeamPCP, which provided access to credentials from downstream users. "Using stolen credentials obtained from the Trivy incident, the threat actor was able to access Checkmarx's GitHub repositories and publish malicious code on March 23," the company explained in a statement.
The attackers maintained persistence in Checkmarx's systems for approximately a month before escalating their activities. "As a result of that access, the attackers were able to interact with Checkmarx's GitHub environment and subsequently publish malicious code to certain artifacts," Checkmarx stated.
On April 22, the attackers published malicious Docker images, VSCode and Open VSX extensions for Checkmarx's KICS security scanner. These malicious components were designed to steal credentials, keys, tokens, and configuration files from systems that downloaded and used them.
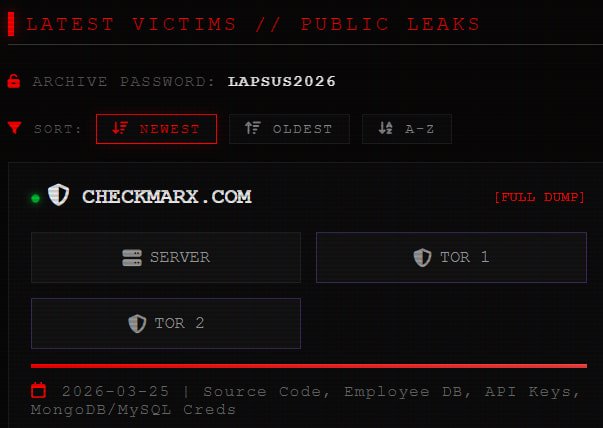
In a recent update, Checkmarx confirmed that the data published by the LAPSUS$ group on their extortion portal belonged to Checkmarx and originated from the March 23 compromise. "Our investigation, conducted with support from a leading third-party forensic firm, indicates that a cybercriminal group has published data related to Checkmarx to the dark web," reads the update. "Based on current evidence, we believe this data originated from Checkmarx's GitHub repository, and that access to that repository was facilitated through the initial supply chain attack of March 23, 2026."
While Checkmarx and other media outlets initially reported that the data was leaked on the dark web, further investigation revealed that LAPSUS$ has also made the 96GB data pack available through clearnet portals, potentially broadening the exposure.

Checkmarx has assured that the leaked data does not contain customer information, as this is not stored in the company's GitHub repository. However, a forensic investigation is still underway to determine the exact type of data that has been exposed. The company has stated that if customer information is found in the leaked data, affected individuals will be notified immediately.
"This incident highlights the cascading nature of supply chain attacks," noted security researcher Sarah Jenkins, who was not involved in the investigation but specializes in software supply chain security. "When one component is compromised, it can create a ripple effect that impacts multiple organizations. Companies need to implement stronger authentication and access controls for their development environments."
Checkmarx has blocked access to the affected GitHub repository until the investigation is complete and estimates that it will be able to share more details within the next 24 hours.
For organizations using Checkmarx products, the company recommends verifying the integrity of any downloaded components and checking for any unusual activity in their systems. Additionally, security professionals should monitor for any potential exploitation of the leaked information.
This incident follows several other high-profile breaches in the software supply chain, including the Cisco source code theft linked to the same Trivy vulnerability. These events underscore the increasing sophistication of threat actors targeting development environments and the critical need for enhanced security measures throughout the software development lifecycle.

Comments
Please log in or register to join the discussion