CISA has added two recently patched Roundcube Webmail vulnerabilities to its Known Exploited Vulnerabilities catalog, requiring federal agencies to patch within three weeks amidst confirmed attacks.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent directive for federal agencies to patch two actively exploited vulnerabilities in Roundcube Webmail, giving organizations until March 13th to secure their systems. This emergency action follows confirmed attacks targeting unpatched email servers.
Roundcube Webmail serves as the default mail interface for cPanel web hosting environments since 2008, powering email services for thousands of organizations. The vulnerabilities now under active exploitation include:
CVE-2025-49113: A critical remote code execution flaw allowing attackers to execute arbitrary code on vulnerable servers. Patched in June 2025, cybersecurity watchdog Shadowserver reported over 84,000 vulnerable instances shortly after disclosure.
CVE-2025-68461: A cross-site scripting (XSS) vulnerability enabling unauthenticated attackers to inject malicious scripts via SVG documents. Patched in December 2025, Roundcube's security team emphasized that "all productive installations" require immediate updating to versions 1.6.12 or 1.5.12.
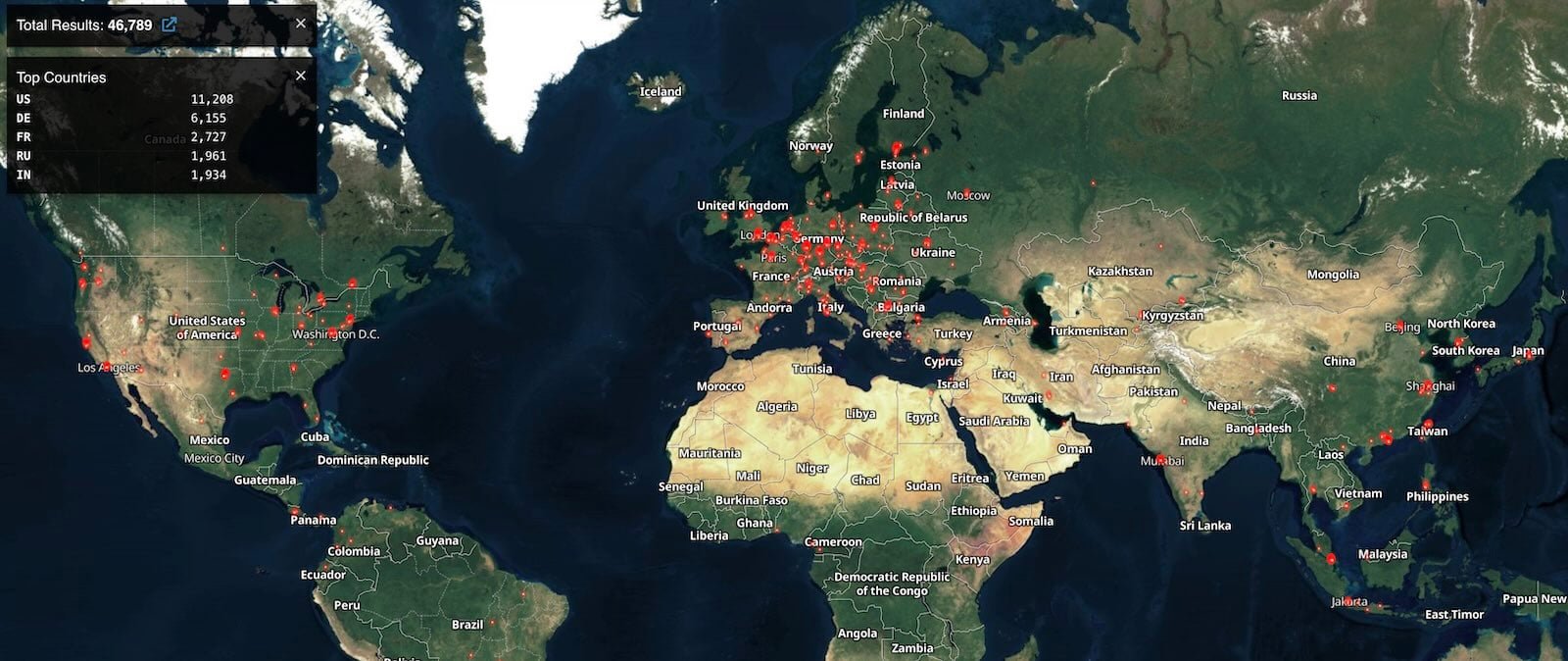
According to Shodan data, over 46,000 Roundcube instances remain publicly accessible online. While exact vulnerability rates are unknown, the exposure surface is significant enough to warrant CISA's emergency Binding Operational Directive (BOD 22-01).
"These vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise," CISA stated in its advisory. The agency now tracks 12 Roundcube vulnerabilities in its Known Exploited Vulnerabilities catalog, reflecting the platform's history as a prime target. Recent campaigns include:
- Russian hacking group Winter Vivern exploiting CVE-2023-5631 against European governments
- APT28 leveraging Roundcube flaws to breach Ukrainian email systems
John Bambenek, Principal Threat Hunter at Netenrich, notes: "Email systems remain high-value targets because they contain sensitive communications and credentials. When webmail platforms like Roundcube have RCE flaws, attackers gain footholds into entire networks."
Practical mitigation steps:
- Immediate patching: Upgrade to Roundcube 1.6.12 or 1.5.12 (or newer)
- Exposure assessment: Scan for publicly exposed Roundcube instances using tools like Shodan or Censys
- Input sanitization: Implement strict filtering for SVG and HTML content
- Web Application Firewalls: Deploy WAF rules to block exploitation attempts
- Monitoring: Audit authentication logs for suspicious activity
Federal agencies must comply by March 13, but all organizations running Roundcube should treat this as critical priority. Roundcube maintains a security advisory page for ongoing updates. As threat actors increasingly target collaboration tools, proactive patching remains the strongest defense against these evolving attacks.
Comments
Please log in or register to join the discussion