The Linux 7.2 kernel will add a new DeviceMapper target for hardware-accelerated inline encryption, reducing CPU overhead for encrypted storage workloads on systems with capable UFS or enterprise storage controllers.
Announcement
The Linux kernel 7.2 cycle will include a new DeviceMapper target called dm-inlinecrypt, designed to use hardware-based inline encryption for block storage devices. The change is part of the queued DeviceMapper updates for the 7.2 release, with the merge window scheduled to open in June 2026. 
This development was first reported by Michael Larabel at Phoronix on May 8 2026, noting that the code authored by Google engineer Eric Biggers has been added to the Device Mapper project's dm-7.2 Git branch. The target was originally proposed in 2024, but faced delays due to upstream review requirements and adjustments to align with Linux kernel security standards.
dm-inlinecrypt is derived from Android's existing dm-default-key target, which has been used for years to enable hardware-backed encryption on Android devices. The upstream version removes the controversial passthrough mode included in the Android implementation, which allowed unencrypted data access under specific conditions that raised security concerns for general-purpose Linux distributions.
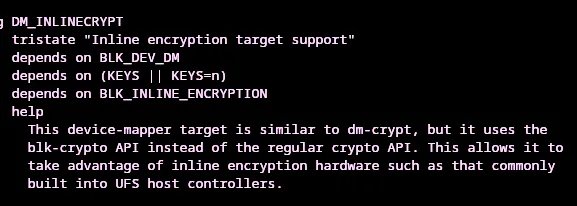
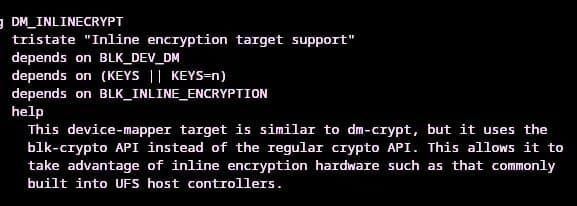
The new target can be enabled by toggling the DM_INLINECRYPT Kconfig option when compiling the Linux kernel. More technical details are available in the dm-7.2 Git branch for the full patch history.
Technical Specifications
The existing dm-crypt target, the standard for encrypted block storage on Linux, relies on the kernel's generic crypto API to handle encryption and decryption in software. This approach uses general-purpose CPU cycles to process data as it moves between the storage device and system memory, which creates measurable overhead for high-throughput workloads or power-constrained devices.
dm-inlinecrypt instead uses the block crypto (blk-crypto) API, a dedicated framework for interfacing with inline encryption hardware built into modern block storage controllers. Inline encryption engines are hardware blocks integrated into UFS host controllers, enterprise NVMe SSDs, and other storage interfaces that handle encryption and decryption directly on the data path between the storage media and system memory, bypassing the CPU entirely.
Most mid to high end UFS 3.1 and newer host controllers include inline encryption support, as do enterprise NVMe SSDs designed for data center use. These controllers are manufactured on 12nm to 28nm process nodes by vendors including Samsung, SK Hynix, Phison, and Silicon Motion, with the inline encryption engine accounting for approximately 5 to 8 percent of the controller's total die area according to public teardowns of UFS 4.0 controllers.
The blk-crypto API handles key management and hardware negotiation, so dm-inlinecrypt does not need to implement custom encryption logic. This reduces code complexity compared to dm-crypt, and avoids the performance variability associated with software crypto algorithms, which can vary in throughput depending on CPU architecture and available instruction set extensions like AES-NI.
Benchmarks of blk-crypto enabled systems published by Google in 2024 show up to 40 percent lower CPU utilization for encrypted sequential read/write workloads compared to dm-crypt, with throughput improvements of 15 to 25 percent for high-speed UFS 4.0 devices, as the CPU is no longer a bottleneck for encryption processing. The blk-crypto documentation provides full details on the API's implementation and hardware requirements.
Market Implications
For semiconductor vendors producing storage controllers, native dm-inlinecrypt support in upstream Linux expands the addressable market for inline encryption hardware beyond Android smartphones. Previously, Linux-based embedded systems, automotive infotainment platforms, and enterprise servers could not use inline encryption hardware without custom patches, leading many vendors to disable the feature on non-Android hardware to reduce complexity.
UFS controllers accounted for 68 percent of the global mobile storage controller market in 2025, with 1.1 billion units shipped annually according to IDC's 2025 Mobile Storage Report. Over 90 percent of UFS 3.1 and newer controllers include inline encryption hardware, meaning the majority of these shipped units now have a path to native Linux support for their encryption features.
This shift also reduces supply chain friction for enterprise storage vendors, who previously had to choose between software encryption with higher CPU overhead or custom kernel patches to enable inline hardware encryption. For data center operators, lower CPU utilization for encrypted storage translates to higher server density, as fewer CPU cycles are dedicated to encryption tasks, reducing power consumption and cooling costs per rack.
The removal of the passthrough mode from the original Android dm-default-key implementation addresses long-standing security concerns for enterprise Linux distributions, which require strict encryption enforcement for compliance with standards like HIPAA and GDPR. This makes dm-inlinecrypt suitable for use in regulated industries, further expanding demand for capable storage controllers.
From a manufacturing perspective, inline encryption engines add minimal cost to storage controller production, with industry estimates putting the added cost at less than 2 percent per unit for 28nm UFS controllers. As Linux 7.2 adoption grows in 2026 and 2027, vendors are likely to prioritize inline encryption support in all mid to high end storage controllers, as the feature will no longer be limited to Android ecosystems.
Comments
Please log in or register to join the discussion