The rapid rise of AI-discovered vulnerabilities is exposing deep flaws in how most organizations track software dependencies, driving renewed interest in deterministic package management systems that can map and remediate CVEs without redundant manual work.

Flox | Achieving CVE Remediation in an Era of Escalating Vulnerabilities
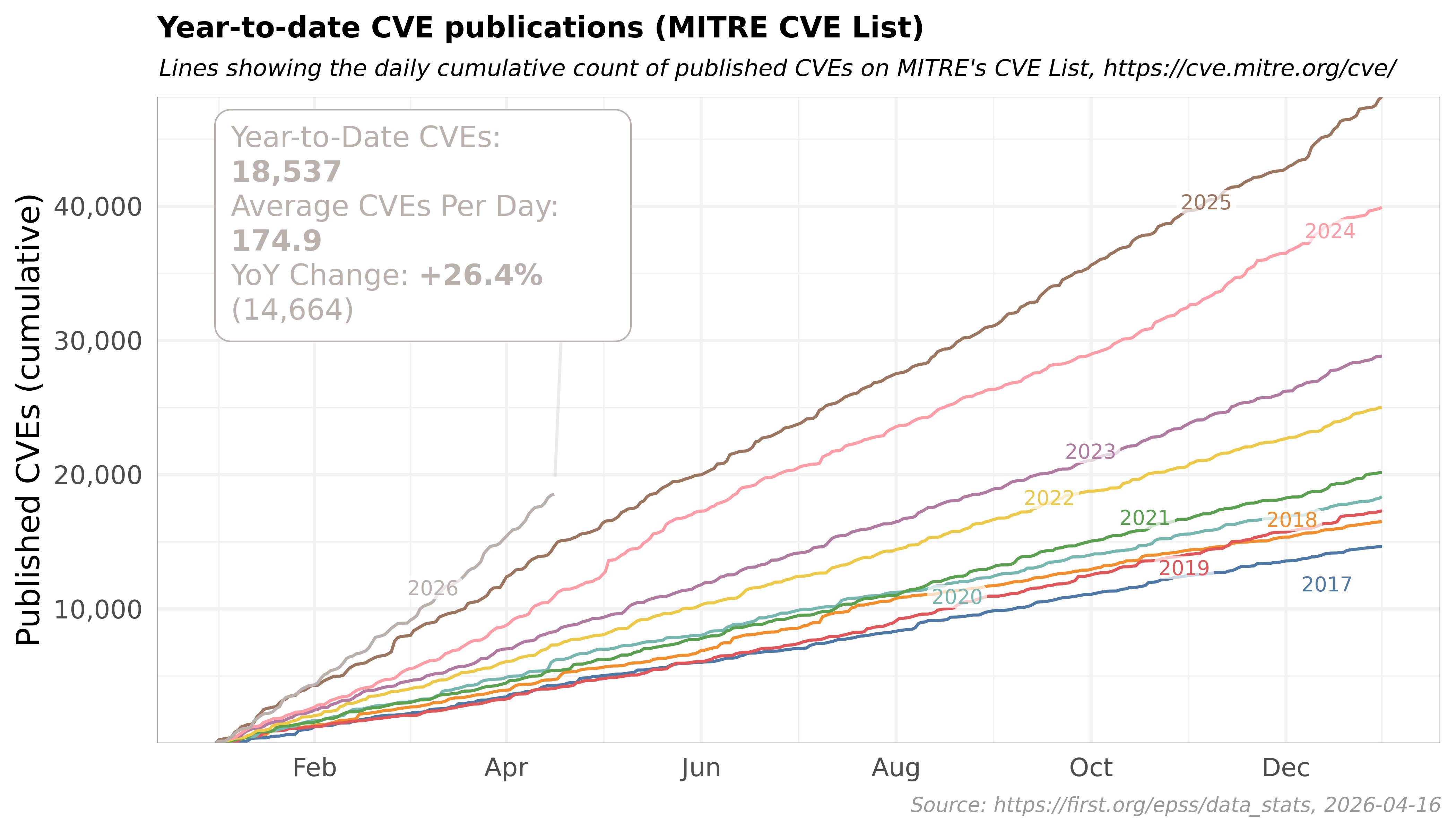
Over the past two years, the volume of disclosed Common Vulnerabilities and Exposures (CVEs) has entered a period of rapid acceleration, driven largely by AI models capable of automated vulnerability discovery. This trend is not hypothetical. Google's Big Sleep project identified a zero-day vulnerability in SQLite, a database engine used in countless applications, in 2024. Microsoft Copilot has since found more than 20 CVEs in bootloader software, while DARPA's AI Cyber Challenge (AIxCC) is offering millions in prizes to teams that build AI systems capable of autonomous vulnerability discovery. The recent release of models like Claude Mythos has only accelerated this pattern, with security researchers warning that AI will soon uncover decades-old vulnerabilities that evaded human researchers.
The core problem facing most organizations is that they lack a complete, queryable record of every package in their software stack. Traditional system package managers like apt, dnf, and zypper, along with toolchain-specific managers like npm, pip, and cargo, resolve package versions in non-deterministic ways. The same install command can produce different results depending on the host environment, cached packages, or upstream mirror used. Most package managers allow version ranges, meaning a single dependency specification can resolve to different packages across environments or over time.
This non-determinism makes CVE triage a massive resource drain. For an organization with n deployments, traditional workflows require scanning each artifact, image, or host independently, because there is no way to prove two environments contain identical dependencies. In algorithmic terms, this is O(n) work, most of which is redundant. When a new CVE is disclosed, teams must manually check every environment to see if the vulnerable package is present, including transitive dependencies that were not intentionally installed.

Conventional lockfiles like Cargo.lock or package-lock.json only solve part of this problem. They record resolved dependencies for a single package ecosystem, but they do not capture the full runtime environment, including base images, native libraries, environment variables, and system-level tools. As a result, there is no unified record of the complete dependency graph across an organization's entire stack.
Tools built on the Nix package manager offer a different approach. Nix uses declarative, input-addressed builds that produce immutable store paths identified by cryptographic hashes of their inputs. Every package's complete transitive dependency graph, called a closure, is recorded and queryable. This means two environments that resolve to the same Nix store path are guaranteed to have identical dependencies, eliminating the need to scan each one independently.
Flox builds on Nix to provide a team-friendly workflow for managing environments across development, testing, and production. When a Flox environment is resolved, it generates a manifest.lock file that records the exact package versions, derivations, and store paths for the entire dependency graph. This lockfile acts as a system of record, allowing teams to query which environments contain a vulnerable package in seconds, rather than hours or days.
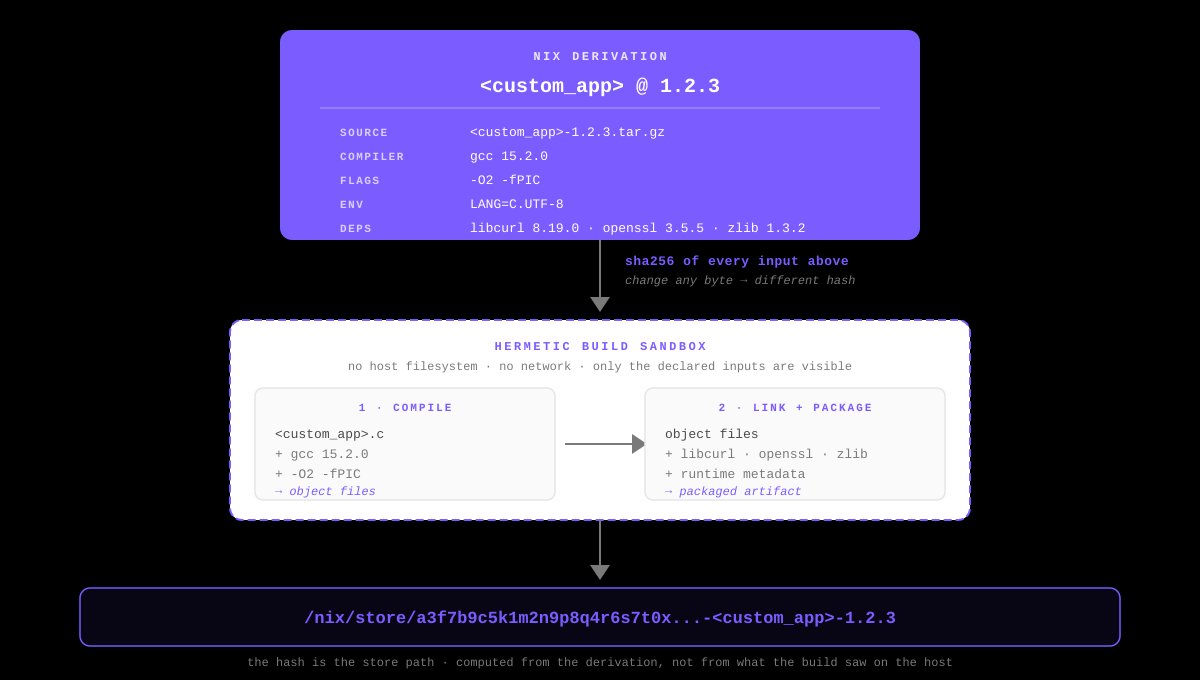
With Nix and Flox, CVE triage shifts from O(n) per environment to O(u) per unique dependency set. If 500 environments collapse to 50 unique closures, the expensive work of checking for vulnerabilities runs 50 times, not 500. Remediation follows the same pattern: teams update the vulnerable package in the environment definition, regenerate the lockfile, and promote the new version across all environments using the same closure. FloxHub, the platform's centralized sharing service, generates SBOMs for each environment generation, making it easy to index dependencies against vulnerability databases.
This approach is not without trade-offs. Nix has a steep learning curve compared to traditional package managers, requiring users to understand declarative builds and store semantics. Building packages in isolation, a core tenet of Nix's hermetic builds, takes longer and uses more disk space than conventional mutable installs. For years, these costs outweighed the benefits for most teams, but the explosion of CVEs is changing that calculus.
Critics also point out that Nix and Flox only manage dependencies that are explicitly included in the environment definition. Packages or artifacts fetched imperatively at runtime, such as scripts that download binaries on activation, are not captured in the closure and must be tracked separately. Migration costs are another barrier: refactoring existing pipelines to use Nix requires significant upfront work, even with coding agents that can automate parts of the process.
There is also debate about whether deterministic package management is the only solution to the CVE surge. Some security teams argue that improved SBOM mandates, better cross-ecosystem scanning tools, and automated patching workflows can address the problem without migrating to Nix. Others note that AI agents could theoretically automate O(n) scanning across environments, but this approach is error-prone and lacks the single source of truth that deterministic builds provide.
The rise of AI-discovered CVEs also introduces new risks. While AI models can find vulnerabilities faster than humans, they can also be used by attackers to engineer scalable exploits. A motivated actor could use a coding agent to generate attacks based on publicly disclosed CVEs, or target an organization's stack using details from conference talks or public documentation. This creates a feedback loop where AI accelerates both vulnerability discovery and exploitation, making fast, reliable remediation more critical than ever.
Community sentiment is mixed. Some developers praise Nix's reproducibility and Flox's user-friendly interface, while others resist adding another tool to their workflow. Adoption signals are growing, however: Nix has seen steady growth in usage over the past five years, and Flox has gained traction among platform teams looking to centralize environment management. DARPA's AIxCC and similar programs suggest that AI-driven vulnerability discovery will only become more common, pushing more organizations to adopt systems that can handle the resulting volume of CVEs.

Comments
Please log in or register to join the discussion