GlassWorm campaign evolves with Solana blockchain dead drops to deliver multi-stage malware framework that steals browser data, crypto credentials, and installs remote access trojans.
Cybersecurity researchers have uncovered a sophisticated evolution of the GlassWorm malware campaign that leverages the Solana blockchain for command-and-control communications while delivering a comprehensive data theft framework and remote access trojan (RAT) capable of compromising cryptocurrency wallets and browser data.
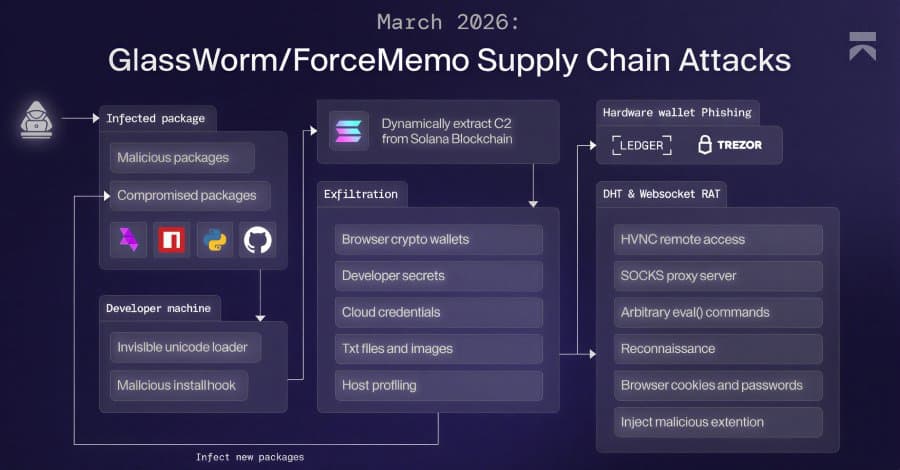
According to a report from Aikido security researcher Ilyas Makari, GlassWorm has developed a multi-stage attack chain that begins with malicious packages distributed across npm, PyPI, GitHub, and the Open VSX marketplace. The attackers have also compromised project maintainer accounts to push poisoned updates, demonstrating an advanced understanding of software supply chain vulnerabilities.
Solana Blockchain as Dead Drop Resolver
The malware employs an innovative approach to evade detection by using Solana transactions as a dead drop resolver to fetch command-and-control server details. This technique allows the attackers to hide their infrastructure behind legitimate blockchain transactions, making traditional network monitoring less effective. The initial C2 server at "45.32.150[.]251" serves as the first point of contact before delivering operating system-specific payloads.
This blockchain-based approach represents a significant evolution in malware communication techniques, as it blends malicious traffic with legitimate cryptocurrency network activity. The method also provides resilience against takedown efforts, since blocking the blockchain itself would be impractical.
Multi-Stage Data Theft Framework
Once installed, the malware deploys a sophisticated data-theft framework that harvests credentials, cryptocurrency wallet information, and system profiling data. All collected information is compressed into ZIP archives and exfiltrated to external servers, specifically "217.69.3[.]152/wall."
The framework includes several advanced capabilities:
- Credential harvesting from various applications
- Cryptocurrency wallet exfiltration targeting both software and hardware wallets
- System profiling to gather detailed information about compromised hosts
- Ability to retrieve and launch additional malicious payloads
Hardware Wallet Phishing Attacks
One of the most concerning aspects of the GlassWorm campaign is its targeted phishing attacks against hardware cryptocurrency wallets. The malware includes a .NET binary that leverages Windows Management Instrumentation (WMI) to detect when USB devices are connected to the system.
When a Ledger or Trezor hardware wallet is detected, the malware displays convincing phishing windows that mimic legitimate wallet interfaces. For Ledger devices, users see a fake configuration error with 24 numbered recovery phrase input fields. Trezor users encounter a "Firmware validation failed, initiating emergency reboot" message with the same recovery phrase layout.
Both phishing interfaces include a "RESTORE WALLET" button designed to trick victims into entering their recovery phrases. The malware actively kills any legitimate Ledger Live processes and re-displays the phishing window if users attempt to close it, demonstrating persistence in its attack methodology.
Advanced RAT Capabilities
The RAT component represents a significant escalation in GlassWorm's capabilities. It uses a Distributed Hash Table (DHT) to retrieve C2 details and falls back to the Solana-based dead drop mechanism if the DHT approach fails. Once connected, the RAT can execute a wide range of commands on compromised systems:
- Deploy Hidden Virtual Network Computing (HVNC) modules for remote desktop access
- Launch WebRTC modules as SOCKS proxies
- Steal data from multiple web browsers including Chrome, Edge, Brave, Opera, Vivaldi, and Firefox
- Bypass Chrome's app-bound encryption (ABE) protections
- Execute arbitrary JavaScript code via eval()
- Gather system information and browser data
Malicious Google Docs Offline Extension
Perhaps most alarmingly, the RAT force-installs a Google Chrome extension named "Google Docs Offline" on both Windows and macOS systems. This extension connects to the C2 server and receives commands from operators, enabling comprehensive browser surveillance.
The extension can collect:
- Cookies and localStorage data
- Full Document Object Model (DOM) tree of active tabs
- Bookmarks and browser history (up to 5,000 entries)
- Installed extensions list
- Screenshots and keystrokes
- Clipboard content
It also performs targeted session surveillance, with Bybit (.bybit.com) pre-configured as a target for monitoring secure-token and deviceid cookies. When these cookies are detected, the extension triggers an auth-detected webhook containing the cookie material and page metadata.
MCP Ecosystem Infiltration
The GlassWorm campaign has expanded into the Model Context Protocol (MCP) ecosystem, with attackers publishing npm packages impersonating the WaterCrawl MCP server. Koi security researcher Lotan Sery noted this represents GlassWorm's first confirmed move into the MCP ecosystem, warning that "given how fast AI-assisted development is growing – and how much trust MCP servers are given by design – this won't be the last."
Protection and Detection
Developers are advised to exercise extreme caution when installing Open VSX extensions, npm packages, and MCP servers. Key protective measures include:
- Verifying publisher names and package histories
- Avoiding blind trust in download counts
- Being skeptical of packages with limited documentation or community presence
- Using security tools to scan for known GlassWorm indicators
Polish cybersecurity company AFINE has released an open-source Python tool called glassworm-hunter that can scan developer systems for payloads associated with the campaign. The tool makes zero network requests during scanning, reads only local files, and updates its indicators of compromise database from GitHub.
Broader Implications
The GlassWorm campaign demonstrates several worrying trends in modern malware development:
- Increased sophistication in supply chain attacks
- Creative use of blockchain technology for command-and-control
- Targeted attacks on cryptocurrency users and hardware wallets
- Exploitation of trust in developer ecosystems
- Multi-platform compatibility and persistence mechanisms
As cryptocurrency adoption continues to grow and AI-assisted development becomes more prevalent, campaigns like GlassWorm are likely to become more common and sophisticated. Organizations and individual users must remain vigilant, particularly when dealing with software packages from unofficial or less-trusted sources.
The campaign's success highlights the critical importance of software supply chain security and the need for robust verification mechanisms before installing any third-party packages or extensions, especially those related to cryptocurrency or development tools.
Comments
Please log in or register to join the discussion