Microsoft and global partners have successfully disrupted Tycoon2FA, one of the most widespread adversary-in-the-middle (AiTM) phishing platforms that enabled cybercriminals to bypass multifactor authentication at scale. This article examines the technical architecture of the service, its business model, and the coordinated takedown operation that highlights the evolving landscape of cybercrime-as-a-service.
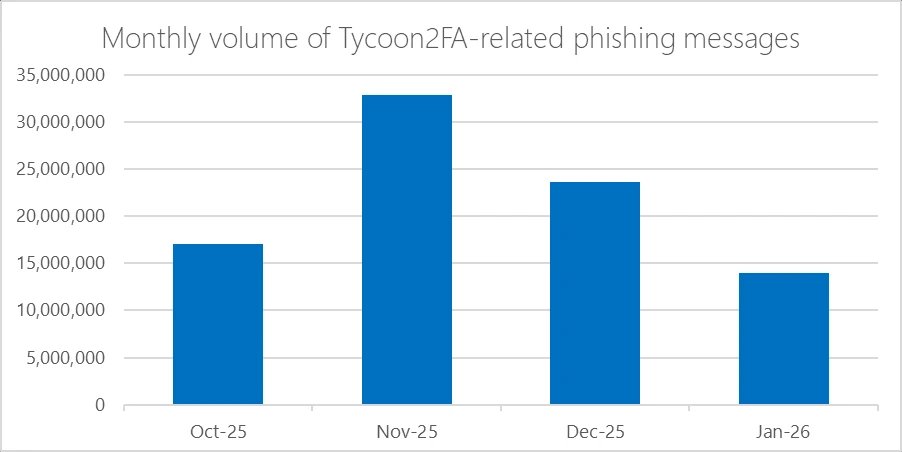
Following its emergence in August 2023, Tycoon2FA rapidly became one of the most dominant phishing-as-a-service (PhaaS) platforms, enabling campaigns responsible for tens of millions of phishing messages reaching over 500,000 organizations each month worldwide. The phishing kit—developed, supported, and advertised by the threat actor tracked by Microsoft Threat Intelligence as Storm-1747—provided adversary-in-the-middle (AiTM) capabilities that allowed even less skilled threat actors to bypass multifactor authentication (MFA), significantly lowering the barrier to conducting account compromise at scale.
Tycoon2FA's rise in popularity among cybercriminals likely stemmed from disruptions of other popular phishing services like Caffeine and RaccoonO365. Its emergence represents a significant evolution in the phishing-as-a-service ecosystem, where specialized platforms offer increasingly sophisticated capabilities to their customers. Campaigns leveraging Tycoon2FA have appeared across nearly all sectors including education, healthcare, finance, non-profit, and government, demonstrating its broad appeal to threat actors targeting various industries.
Technical Architecture: How Tycoon2FA Operated at Scale
Tycoon2FA's platform enabled threat actors to impersonate trusted brands by mimicking sign-in pages for services like Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail. The technical sophistication of the platform lay in its ability to establish persistence and access sensitive information even after passwords were reset, unless active sessions and tokens were explicitly revoked. This worked by intercepting session cookies generated during the authentication process, simultaneously capturing user credentials, then relaying the MFA codes through Tycoon2FA's proxy servers to the authenticating service.

The platform's core innovation was its ability to create seamless AiTM attacks that appeared legitimate to both users and security systems. When a victim entered their credentials, the system immediately relayed them to the real service, triggering the genuine MFA challenge. The phishing page then displayed the same MFA prompt, and once the user completed MFA, the attacker captured the session cookie and gained real-time access without needing further authentication.
To evade detection, Tycoon2FA employed sophisticated techniques including anti-bot screening, browser fingerprinting, heavy code obfuscation, self-hosted CAPTCHAs, custom JavaScript, and dynamic decoy pages. These features made the platform particularly resilient against traditional security measures and enabled it to maintain operations despite increasing defensive capabilities across the industry.
The Business Model: Pricing and Market Position
Tycoon2FA was advertised and sold to cybercriminals on applications like Telegram and Signal, with phish kits starting at $120 USD for access to the panel for 10 days and $350 for access to the panel for a month. These prices varied based on demand and market conditions, positioning Tycoon2FA as a mid-tier offering in the phishing-as-a-service market.
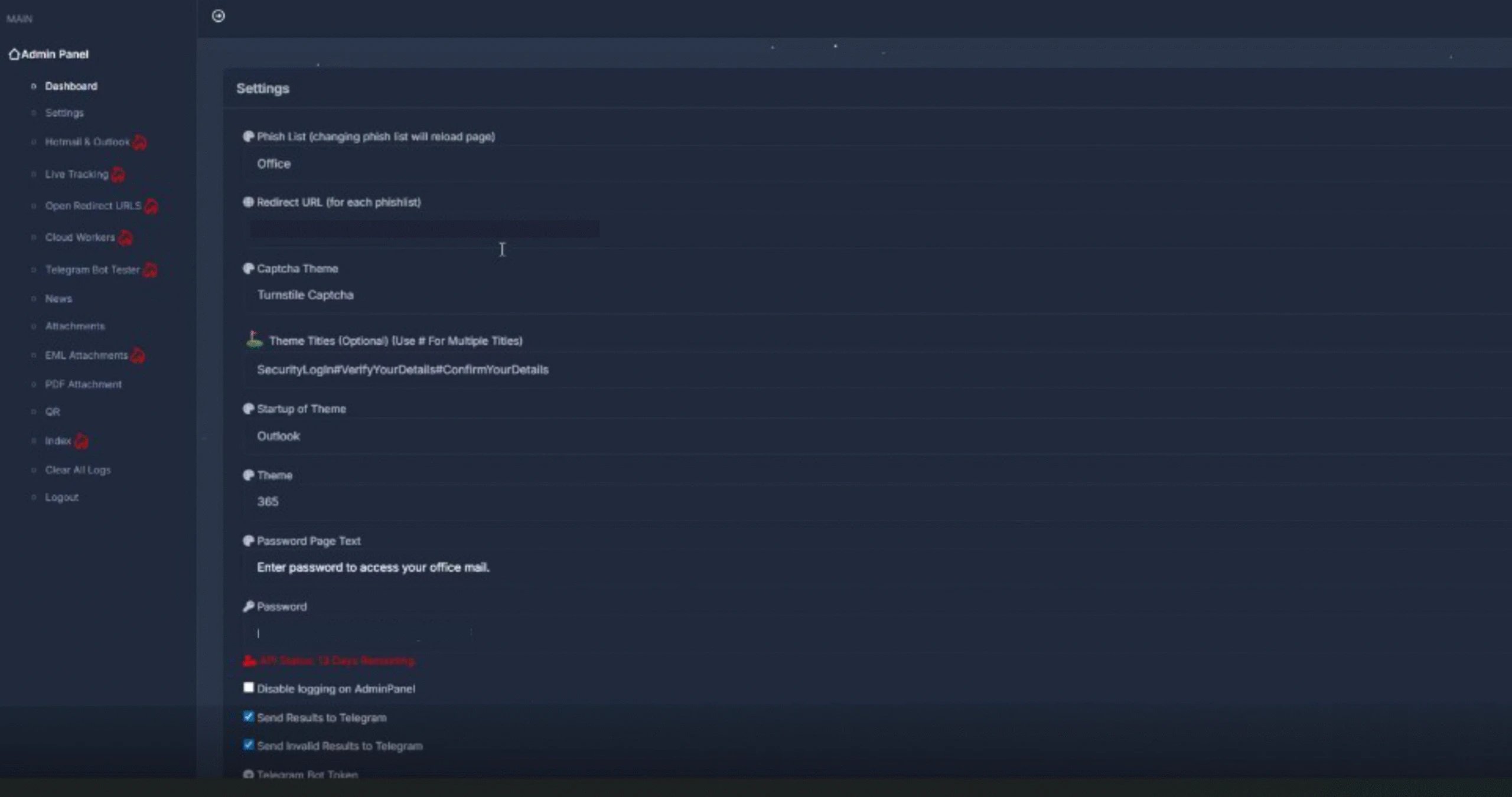
The service was operated through a web-based administration panel provided on a per-user basis that centrally integrated all functionality. This panel served as a single dashboard for configuring, tracking, and refining campaigns. While it did not include built-in mailer capabilities, the panel provided the core components needed to support phishing campaigns, including pre-built templates, attachment files for common lure formats, domain and hosting configuration, redirect logic, and victim tracking.

This design made the platform accessible to less technically skilled actors while still offering sufficient flexibility for more experienced operators. The balance between ease of use and technical sophistication likely contributed to Tycoon2FA's rapid adoption across various threat actor groups.
Operational Overview: The Phishing Campaign Lifecycle
After signing in, Tycoon2FA customers were presented with a dashboard used to configure, monitor, and manage phishing campaigns. Campaign operators could configure a broad set of campaign parameters that controlled how phishing content was delivered and presented to targets. Key settings included lure template selection and branding customization, redirection routing, MFA interception behavior, CAPTCHA appearance and logic, attachment generation, and exfiltration configuration.
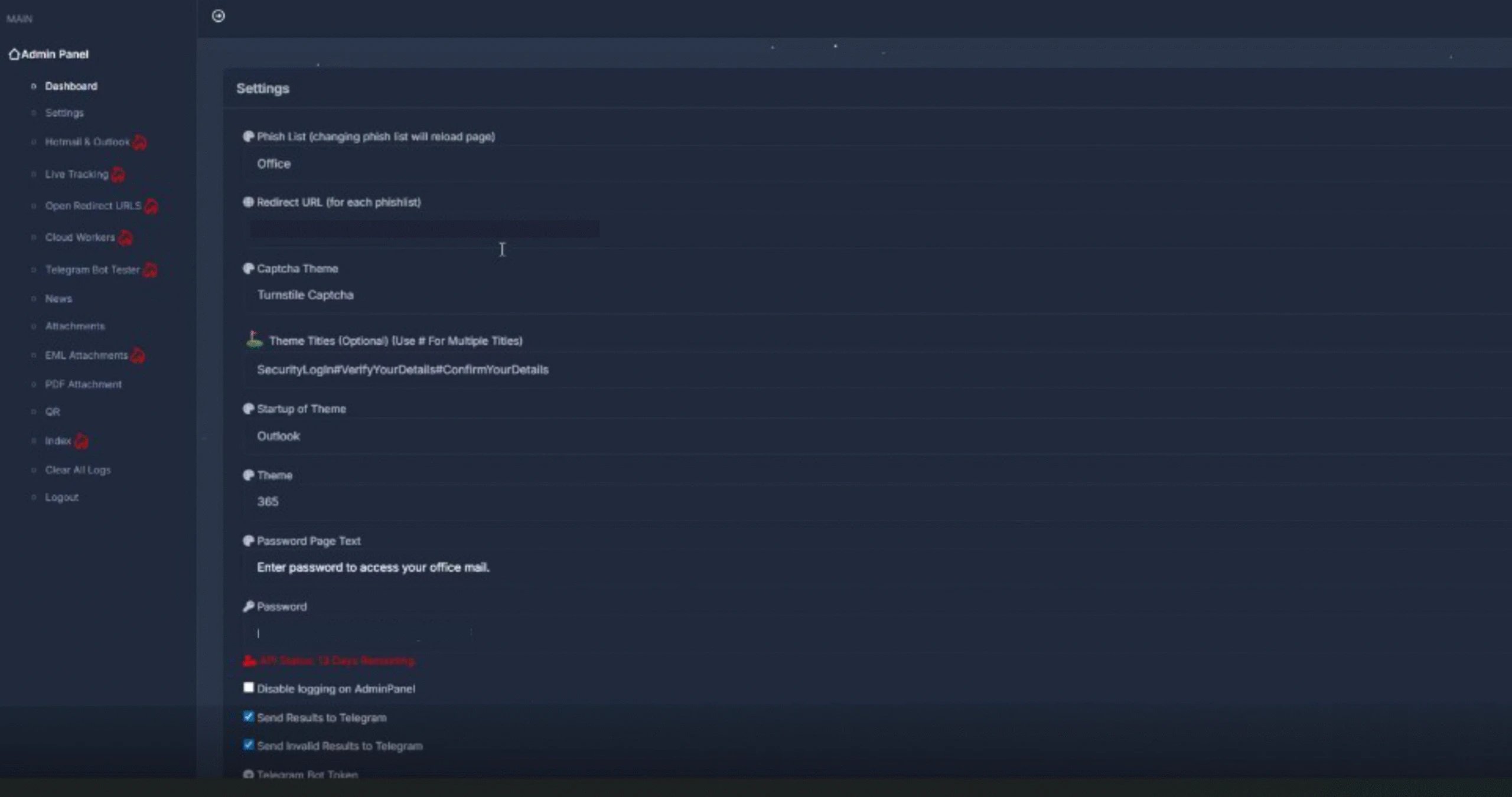
Campaign operators could choose from highly configurable landing pages and sign-in themes that impersonated widely trusted services such as Microsoft 365, Outlook, SharePoint, OneDrive, and Google, increasing the perceived legitimacy of attacks. The platform also allowed operators to configure how malicious content was delivered through attachments, with options including generating EML files, PDFs, and QR codes, offering multiple ways to package and distribute phishing lures.
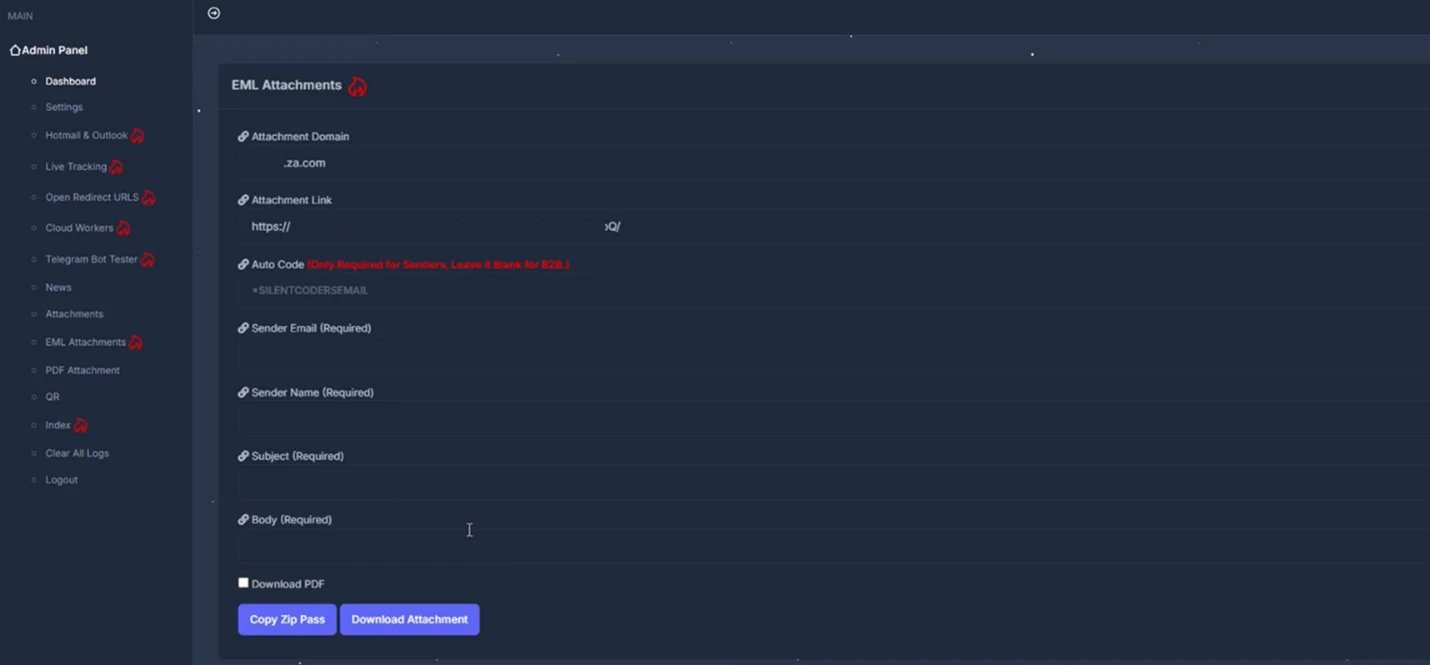
Beyond campaign configuration, the panel provided detailed visibility into victim interaction and authentication outcomes. Operators could track valid and invalid sign-in attempts, MFA usage, and session cookie capture, with victim data organized by attributes such as targeted service, browser, location, and authentication status. Captured credentials and session cookies could be viewed or downloaded directly within the panel and/or forwarded to Telegram for near-real-time monitoring.
Infrastructure Evolution: Adapting to Defensive Measures
Tycoon2FA's infrastructure evolved significantly from static, high-entropy domains to a fast-moving ecosystem with diverse top-level domains (TLDs) and short-lived (often 24-72 hours) fully qualified domain names (FQDNs), with the majority hosted on Cloudflare. A key change was the move toward a broader mix of TLDs. Early tracking showed heavier use of regional TLDs like .es and .ru, but recent campaigns increasingly rotated across inexpensive generic TLDs that require little to no identity verification, such as .space, .email, .solutions, .live, .today, and .calendar.
Subdomain patterns also shifted toward more readable formats. Instead of high entropy or algorithmically generated strings, newly observed subdomains used recognizable words tied to common workflows or services. Some subdomains resembled everyday processes or tech terms like cloud, desktop, application, and survey, while others echoed developer or admin vocabulary like python, terminal, xml, and faq. Software as a service (SaaS) brand names also appeared in subdomains, such as docker, zendesk, azure, microsoft, sharepoint, onedrive, and nordvpn.
This shift was likely used to reduce user suspicion and evade detection models that rely on entropy or string irregularity. The rapid turnover of domains and subdomains complicated detection efforts, such as building reliable blocklists or relying on reputation-based defenses.
Defense Evasion Tactics: Outmaneuvering Security Controls
From a defense standpoint, Tycoon2FA stood out for its continuously updated evasion and attack techniques. A defining feature was the use of constantly changing custom CAPTCHA pages that regenerated frequently and varied across campaigns. Before credentials were entered, targets encountered custom CAPTCHA challenges designed to block automated scanners and ensure real users reached the phishing content. These challenges often used randomized HTML5 canvas elements, making them hard to bypass with automation.
The phishing kit also disrupted analysis through obfuscation and dynamic code generation, including nonfunctional dead code, to defeat consistent fingerprinting. When the campaign infrastructure encountered an unexpected or invalid server response (for example, a geolocation outside the allowed targeting zone), the kit replaced phishing content with a decoy page or a benign redirect to avoid exposing the live credential phishing site.
Tycoon2FA further complicated investigation by actively checking for analysis of environments or browser automation and adjusting page behavior if detected. These evasive measures included:
- Intercepting user input and keystroke monitoring
- Blocking copy/paste and right-click functions
- Detecting or blocking automated inspection tools
- Disabling common developer tool shortcuts
- Validating and filtering incoming traffic
- Browser fingerprinting and datacenter IP filtering
- Geolocation restrictions and suspicious user agent profiling
- Increased obfuscation through encoded content, fragmented strings, and invisible Unicode characters
- Layered URL/URI encoding and dead or nonfunctional scripts
If analysis was suspected at any point, the kit redirected to a legitimate decoy site or threw a 404 error. Complementing these anti-analysis measures, Tycoon2FA used increasingly complex redirect logic, chaining multiple intermediate hosts such as Azure Blob Storage, Firebase, Wix, TikTok, or Google resources to lend legitimacy to the redirect path.
The Global Takedown Operation: Disrupting Tycoon2FA
In collaboration with Europol and industry partners, Microsoft's Digital Crimes Unit (DCU) facilitated a disruption of Tycoon2FA's infrastructure and operations. The coordinated action represents a significant success in the ongoing battle against cybercrime-as-a-service platforms, demonstrating the effectiveness of public-private partnerships in addressing transnational cyber threats.
The takedown operation involved multiple phases, including intelligence gathering, legal coordination, and technical disruption. By targeting both the infrastructure and the business model of Tycoon2FA, the coalition was able to significantly reduce the platform's ability to operate at scale. This operation follows similar successful actions against other major cybercrime platforms, highlighting a growing trend of coordinated law enforcement and industry responses to sophisticated cyber threats.
Business Impact: Implications for Organizations and Security Strategies
The disruption of Tycoon2FA represents both a temporary victory and a reminder of the persistent nature of cybercrime threats. Organizations should view this as an opportunity to reassess their security strategies, particularly around identity and authentication. The rise of sophisticated phishing platforms like Tycoon2FA demonstrates that traditional security measures are increasingly insufficient against well-resourced and technically capable threat actors.
Key business impacts include:
- Reassessment of authentication strategies: Organizations should consider moving beyond traditional MFA to phishing-resistant methods such as FIDO2 security keys, Windows Hello for Business, and Microsoft Authenticator passkeys.
- Evaluation of security investments: The sophistication of platforms like Tycoon2FA highlights the need for layered security approaches that combine technical controls with user awareness.
- Review of incident response procedures: The speed and scale of Tycoon2FA campaigns necessitate rapid detection and response capabilities to minimize potential damage.
- Consideration of supply chain security: The use of third-party services and platforms by threat actors underscores the importance of securing the entire technology ecosystem.
Mitigation Strategies: Defending Against AiTM Phishing Threats
Defending against Tycoon2FA and similar AiTM phishing threats requires a layered approach that blends technical controls with user awareness. Microsoft recommends several key mitigation strategies:
Adopt phishing-resistant authentication methods: Implement passwordless authentication methods such as FIDO2 security keys, Windows Hello for Business, and Microsoft Authenticator passkeys. Enforce phishing-resistant MFA for privileged roles in Microsoft Entra ID to significantly reduce the risk of account compromise.
Configure advanced email security settings:
- Recommended settings for Exchange Online Protection and Microsoft Defender for Office 365
- Configure Microsoft Defender for Office 365 to recheck links on click
- Turn on Zero-hour auto purge (ZAP) in Defender for Office 365
- Enable Safe Links and Safe Attachments in Microsoft Defender for Office 365
Implement endpoint protection:
- Enable network protection in Microsoft Defender for Endpoint
- Encourage users to use Microsoft Edge and other web browsers that support Microsoft Defender SmartScreen
- Turn on cloud-delivered protection in Microsoft Defender Antivirus or equivalent
Conduct security awareness training:
- Use the Attack Simulator in Microsoft Defender for Office 365 to run realistic phishing simulations
- Train end-users against clicking URLs in unsolicited messages and disclosing credentials
Deploy advanced detection capabilities:
- Configure automatic attack disruption in Microsoft Defender XDR
- Implement Microsoft Entra with increased security
- Pilot and deploy phishing-resistant authentication methods for users
- Implement Entra ID Conditional Access authentication strength to require phishing-resistant authentication
Future Outlook: The Evolving Landscape of Phishing-as-a-Service
The disruption of Tycoon2FA is unlikely to eliminate the threat of sophisticated phishing platforms. Instead, it will likely lead to the emergence of new services or the evolution of existing ones to fill the gap. The phishing-as-a-service ecosystem continues to evolve, with platforms becoming increasingly sophisticated and accessible to less technically skilled threat actors.
Organizations should prepare for this evolving threat landscape by:
- Investing in advanced threat detection and response capabilities
- Adopting zero-trust security principles
- Implementing phishing-resistant authentication methods
- Maintaining robust security awareness programs
- Participating in information sharing communities to stay ahead of emerging threats
The takedown of Tycoon2FA demonstrates that coordinated action between industry and law enforcement can have a significant impact on cybercriminal operations. However, it also highlights the need for continuous vigilance and adaptation in the face of evolving threats.
Conclusion: Strategic Implications for Cloud Security
The rise and fall of Tycoon2FA offers several important lessons for organizations navigating the complex cloud security landscape. The platform's technical sophistication and business model reflect broader trends in the cybercrime ecosystem, where specialized services enable increasingly effective attacks at lower barriers to entry.
For organizations, the key takeaway is that traditional security measures are no longer sufficient against well-resourced and technically capable threat actors. A layered approach combining phishing-resistant authentication, advanced threat detection, and user awareness is essential to defend against modern phishing threats.
The disruption of Tycoon2FA represents a significant victory in the fight against cybercrime, but it is not the end of the threat. Organizations should view this as an opportunity to reassess their security strategies and invest in more robust defenses against evolving threats. By adopting a proactive and adaptive security posture, organizations can better protect themselves against the sophisticated attacks that characterize the modern threat landscape.

Comments
Please log in or register to join the discussion