Microsoft has enhanced its Agent Framework with PII Shield middleware components that automatically anonymize and de-anonymize sensitive data throughout AI agent interactions, addressing critical privacy concerns in regulated industries.
Privacy Proxy in Agents with Microsoft Agent Framework Middleware
In today's increasingly regulated business environment, AI agents present unique challenges for data privacy protection. As AI systems become more sophisticated, they introduce multiple points where sensitive information can unintentionally propagate through complex networks of models, tools, planners, and memory components. This complexity makes protecting personally identifiable information (PII) significantly more challenging than in traditional applications.
The Challenge: Protecting PII in Complex AI Systems
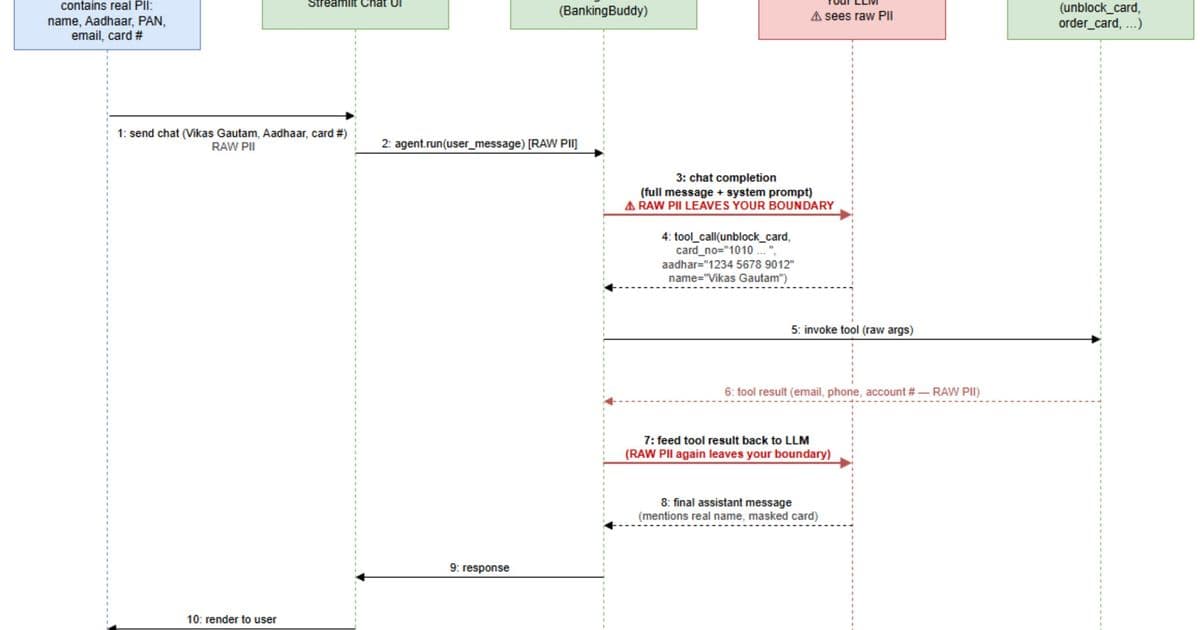
An AI agent is not a single model call but a complex system combining multiple components. Consider a banking chatbot designed to help customers with tasks such as unblocking cards or requesting replacements. As part of its workflow, the agent collects sensitive information including the customer's name, identification numbers, card details, and date of birth. This data is used to validate the customer, invoke backend APIs, and ultimately communicate outcomes.
The critical issue emerges when we examine the interactions between the agent and language models. Some information about the customer is sent across so that the LLMs can perform tool calling and frame accurate responses. For regulated industries, this could be a significant compliance risk. If not handled properly, actual customer information could inadvertently surface in LLM inference logs or downstream processing layers.
Rather than placing this responsibility on individual AI developers, the burden should be absorbed by the enterprise architecture. Developers should remain focused on delivering business functionality, while a centralized, enforced privacy boundary ensures that all LLM and tool interactions are consistently governed. This boundary must be non-optional—every request and response flows through it, with no possibility of bypass.
Microsoft's Solution: PII Shield Middleware
Microsoft addresses this challenge through PII Shield, integrated as middleware in the Microsoft Agent Framework. This approach removes the need for per-agent privacy engineering and guarantees uniform protection across applications—an essential requirement in highly regulated sectors such as BFSI, healthcare, and government.
The Microsoft Agent Framework provides two middleware extensibility points that are particularly relevant for privacy protection:
- ChatMiddleware: Wraps every LLM call, anonymizing outgoing messages and de-anonymizing responses
- FunctionMiddleware: Manages every @tool invocation, de-anonymizing tool arguments and re-anonymizing tool results
Together, these components form a generalized implementation of the "Anonymize → LLM → De-anonymize" pattern, systematically applied to every LLM interaction and tool call within an agent's execution loop.
Implementation Architecture
The implementation relies on several key components working in concert:
- PiiMappingStore: Serves as per-conversation memory, maintaining the association between placeholders (e.g., {{PERSON_1}}, {{IN_AADHAAR_1}}) and their corresponding real values
- PiiShieldChatMiddleware: Operates at the LLM boundary, sanitizing every outbound prompt before it reaches the model, and restoring original values in the model's response
- PiiShieldFunctionMiddleware: Wraps all tool calls, resolving placeholders into real values before execution and re-anonymizing results before they are passed back into the agent loop
By registering both middleware components in the agent's middleware pipeline, the privacy boundary becomes comprehensive and non-bypassable. Every prompt, tool invocation, and response is automatically governed.
Comments
Please log in or register to join the discussion