Microsoft is completing the retirement of DES encryption for Kerberos authentication while providing enhanced tools to detect and manage legacy RC4 usage, significantly improving enterprise security posture.
Microsoft has announced the final phase of removing DES encryption as an option for Kerberos authentication, a critical security update that affects enterprise environments worldwide. This move, coupled with enhanced detection capabilities for RC4 usage, represents a significant step forward in securing Windows authentication protocols against known vulnerabilities.
What Changed: The Complete Removal of DES
Data Encryption Standard (DES), a legacy encryption method dating back to the 1970s, has long been recognized as cryptographically weak. Microsoft's Directory Services team, led by Chris Cartwright, has now finalized the complete removal of DES as an encryption type for Kerberos. This change addresses long-standing security concerns while pushing organizations toward more robust authentication methods.
The transition away from DES is particularly important because:
- DES can be broken with relatively modest computing resources
- It's vulnerable to brute-force attacks
- Modern compliance standards often prohibit its use
Microsoft has provided comprehensive tools to assist organizations in this transition through the microsoft/Kerberos-Crypto repository, which includes identification scripts and documentation to help administrators detect and remediate DES usage in their environments.
Enhanced Detection Capabilities for RC4
Simultaneously with the DES retirement, Microsoft has enhanced its capabilities to detect and manage RC4 usage, another legacy encryption method that has known vulnerabilities. The company released "Beyond RC4 for Windows authentication" guidance and implemented patching efforts related to CVE-2026-20833, which addresses RC4 vulnerabilities in service account ticket issuance.
The enhanced detection capabilities include:
- New XML filters for identifying RC4 usage in authentication logs
- Updated Event IDs 4768 and 4769 with additional information about ticket encryption
- Custom event forwarding mechanisms specifically designed to flag legacy encryption usage
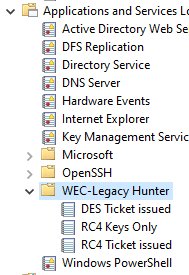
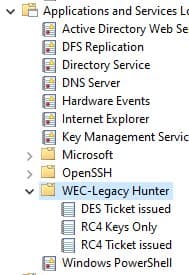
Technical Implementation: XML Filters and Event Forwarding
For administrators implementing these changes, Microsoft has provided detailed XML filters that can be used to detect specific authentication events. These filters enable organizations to identify:
- DES tickets issued across different encryption types (0x1, 0x2, 0x3)
- Legacy keys available for authentication (RC4, DES combinations)
- RC4 tickets issued (using encryption type 0x17)
The XML filters can be implemented directly in Windows Event Viewer or through custom event forwarding solutions. For organizations requiring more sophisticated detection, Microsoft has provided a complete manifest for creating custom event forwarder targets using Visual Studio.
The custom event forwarder creates dedicated channels for:
- RC4 Keys Only detection
- RC4 Usage tracking
- DES Usage tracking
Business Impact and Migration Considerations
The retirement of DES and enhanced RC4 detection capabilities have several important business implications:
Security Posture Improvement
Organizations implementing these changes will immediately improve their security posture by eliminating known weak encryption methods. This reduces the attack surface and helps meet compliance requirements for various industry standards.
Migration Complexity
For organizations still using legacy applications that depend on DES or RC4, the migration may require:
- Application updates to support stronger encryption
- Careful testing in non-production environments
- Phased rollout to minimize business disruption
Operational Monitoring
The enhanced detection capabilities provide valuable visibility into authentication patterns, enabling security teams to:
- Identify unauthorized access attempts
- Monitor compliance with encryption policies
- Detect potential security anomalies
Multi-Environment Considerations
For organizations operating in hybrid or multi-cloud environments, these changes require consistent implementation across all domains. Microsoft's tools and documentation provide a foundation for standardizing security policies across different environments.
Implementation Recommendations
Based on Microsoft's guidance, organizations should:
- Inventory Current Usage: Use the provided XML filters to identify current DES and RC4 usage patterns
- Prioritize Critical Systems: Focus first on systems handling sensitive data or external access
- Coordinate with Application Owners: Work with development teams to update applications that may depend on legacy encryption
- Implement Enhanced Monitoring: Deploy the custom event forwarder solutions to maintain visibility into authentication patterns
- Update Documentation: Revise security policies and procedures to reflect the new encryption requirements
The complete retirement of DES represents a significant milestone in Microsoft's ongoing efforts to modernize authentication security. By providing comprehensive tools and documentation, the company has made it possible for organizations to transition away from legacy encryption methods while maintaining operational continuity.
For organizations implementing these changes, the microsoft/Kerberos-Crypto repository and the "Beyond RC4 for Windows authentication" blog provide essential resources for successful migration. Additionally, the updated Event IDs 4768 and 4769 offer improved visibility into authentication patterns, enabling more effective security monitoring.
As authentication threats continue to evolve, Microsoft's proactive approach to retiring legacy encryption methods demonstrates a commitment to maintaining enterprise security in increasingly complex IT environments. The enhanced detection capabilities not only address current vulnerabilities but also provide a foundation for future security improvements.
Comments
Please log in or register to join the discussion