Microsoft warns of tax season phishing campaigns targeting 29,000 users across 10,000 organizations, using IRS impersonation and remote monitoring tools to deliver malware and steal credentials.
Microsoft has issued a warning about a surge in tax-themed phishing campaigns that have already impacted over 29,000 users across 10,000 organizations in the United States. These attacks are exploiting the urgency and time-sensitive nature of tax season to deliver malware and steal sensitive financial data.
The campaigns take various forms, including fake refund notices, payroll forms, filing reminders, and requests from tax professionals. Many target individuals for personal data theft, while others specifically focus on accountants and professionals who handle sensitive documents and financial data.
Key Campaign Tactics
One major campaign impersonated the Internal Revenue Service (IRS), claiming that irregular tax returns had been filed under victims' Electronic Filing Identification Numbers (EFINs). Recipients were instructed to review these returns by downloading a "legitimate" IRS Transcript Viewer. These emails, sent through Amazon Simple Email Service, contained a "Download IRS Transcript View 5.1" button that redirected users to a domain masquerading as SmartVault.
The phishing site used Cloudflare to evade detection, serving only human users the main payload: a maliciously packaged ScreenConnect remote monitoring and management tool. This grants attackers persistent access to compromised systems for data theft and credential harvesting.
Remote Monitoring Tools Abuse
Several campaigns deliver legitimate RMM tools like ConnectWise ScreenConnect, Datto, and SimpleHelp. These tools, commonly used by IT departments, are now being abused at an alarming rate. According to Huntress, RMM tool abuse has surged 277% year-over-year.
"As these tools are used by legitimate IT departments, they are typically overlooked and considered 'trusted' in most corporate environments," said Elastic Security Labs researchers Daniel Stepanic and Salim Bitam. "Organizations must stay vigilant, auditing their environments for unauthorized RMM usage."
Other Notable Campaigns
- Energy365 PhaaS Kit: Uses CPA lures to deliver phishing pages, sending hundreds of thousands of malicious emails daily
- QR Code and W2 Lures: Targets manufacturing, retail, and healthcare organizations with Microsoft 365 sign-in page impersonations
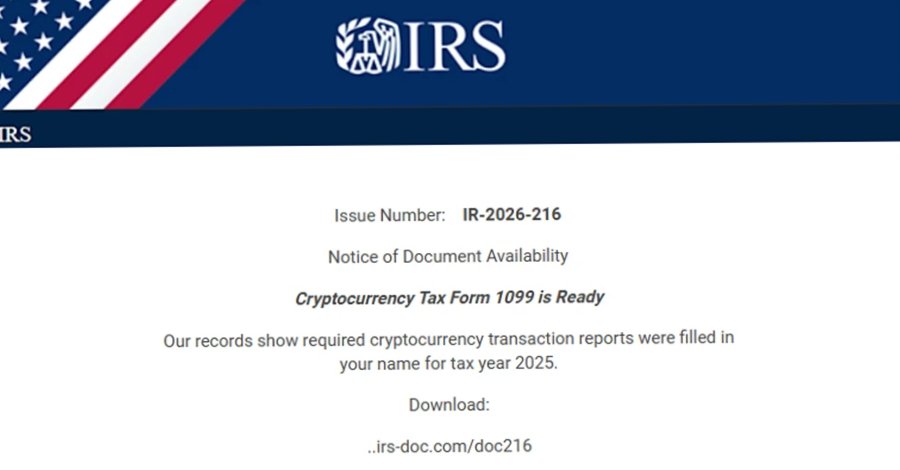
- Cryptocurrency Tax Form 1099: Targets higher education sector with malicious domains like "irs-doc[.]com"
- Tax-Themed Domains: Distribute ScreenConnect through bogus links to "updated tax forms"
Industry Targeting
About 95% of targets were located in the U.S., with financial services (19%), technology and software (18%), and retail and consumer goods (15%) being the most affected industries. The campaigns use sophisticated techniques including multi-vendor chained redirection, typosquatted websites, and malicious ZIP files disguised as popular software.
Protection Recommendations
Organizations are advised to:
- Enforce two-factor authentication on all users
- Implement conditional access policies
- Monitor and scan incoming emails and visited websites
- Prevent access to known malicious domains
The attacks demonstrate how threat actors are increasingly leveraging legitimate tools and services to bypass security measures, making traditional detection methods less effective. This trend highlights the need for comprehensive security strategies that go beyond signature-based detection.
For more information on protecting against phishing and malware, visit Microsoft's security resources.
Comments
Please log in or register to join the discussion