Security researchers have uncovered a new Mirai-derived botnet that targets Android-exposed IoT devices, offering DDoS-for-hire services with 21 attack variants.
Security researchers at Hunt.io have exposed a sophisticated new botnet that builds on the notorious Mirai malware family to hijack internet-connected devices for DDoS attacks. The self-identified 'xlabs_v1' botnet specifically targets devices with exposed Android Debug Bridge (ADB) services, creating a network capable of launching 21 different flood attack variants against game servers and other targets.
The discovery began when Hunt.io researchers identified an unauthenticated directory on a Netherlands-hosted server at IP address 176.65.139[.]44. This exposed entry point gave them direct access to the botnet's infrastructure without needing to bypass any security measures. "The botnet is offered as a DDoS-for-hire service designed specifically for targeting game servers and Minecraft hosts," explained the Hunt.io team in their analysis.
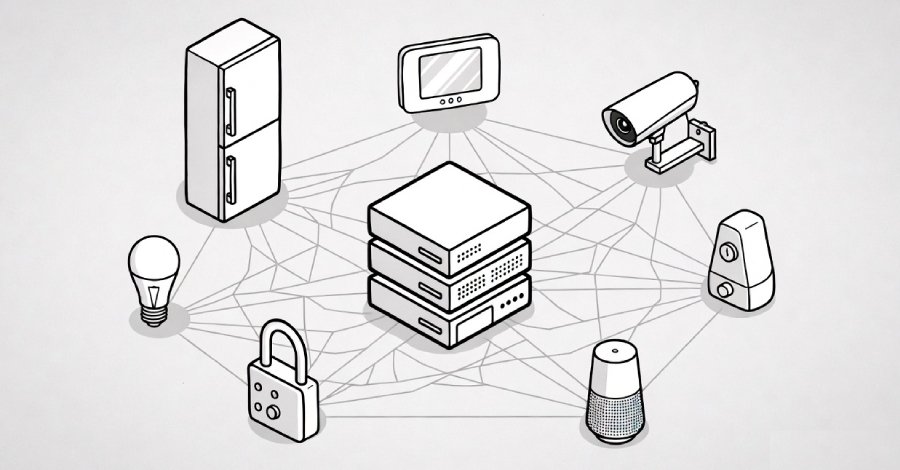
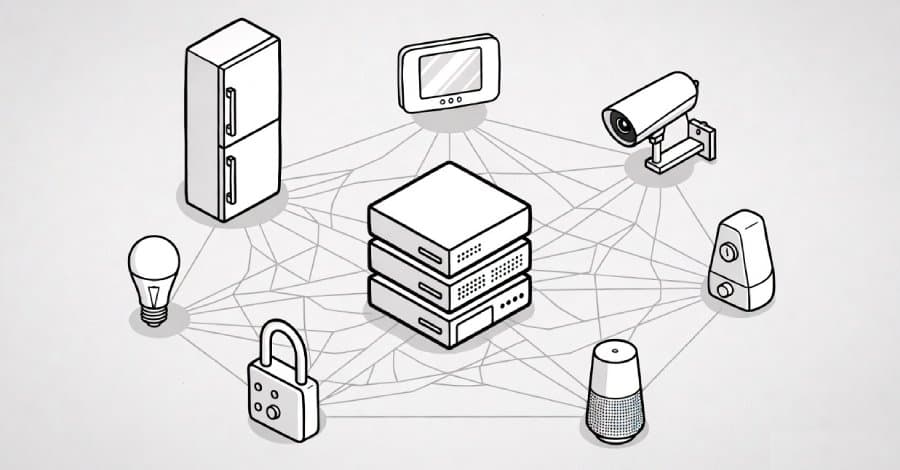
What makes xlabs_v1 particularly concerning is its focus on Android devices running ADB on TCP port 5555. Many consumer devices come with this debugging tool enabled by default, including Android TV boxes, set-top boxes, and smart TVs. The malware demonstrates cross-platform compatibility, supporting ARM, MIPS, x86-64, and ARC architectures, which suggests it can target residential routers and various IoT hardware.
"The bot is statically-linked ARMv7, runs on stripped Android firmwares, and is delivered through ADB-shell pastes into /data/local/tmp," Hunt.io detailed. "The operator's nine-variant payload list is tuned for Android TV boxes, set-top boxes, smart TVs, and IoT-grade ARM hardware that ships with ADB enabled."
The botnet's business model appears to be bandwidth-tiered pricing, based on a sophisticated bandwidth-profiling routine. When compromised, infected devices open 8,192 parallel TCP connections to the nearest Speedtest server, saturate them for 10 seconds, and report the measured data transfer rate back to the operator's panel at xlabslover[.]lol. This information helps the operator assign each compromised device to appropriate pricing tiers for their paying customers.
Interestingly, the botnet lacks persistence mechanisms. "The bot does not write itself to disk persistence locations, does not modify init scripts, does not create systemd units, and does not register cron jobs," Hunt.io noted. "This design suggests the operator views bandwidth probing as an infrequent fleet-tier-update operation rather than a per-attack pre-flight check, and the resulting exit-and-re-infect cycle is the design intent."

The xlabs_v1 botnet also includes a "killer" subsystem designed to terminate competing malware on infected devices. This ensures the botnet can usurp the victim device's full upstream bandwidth for its DDoS attacks. While the threat actor behind the malware uses the alias "Tadashi" (evidenced by a ChaCha20-encrypted string in each build), the actual identity remains unknown.
Further investigation of the co-located infrastructure revealed a VLTRig Monero-mining toolkit on host 176.65.139[.]42, though researchers haven't confirmed if this is connected to the same threat actor.
"In commercial-criminal terms, xlabs_v1 is mid-tier," Hunt.io assessed. "It is more sophisticated than the typical script-kiddie Mirai fork [...], but less sophisticated than the top tier of commercial DDoS-for-hire operations. This operator is competing on price and attack variety, not technical sophistication. Consumer IoT devices, residential routers, and small game-server operators are the target."
The emergence of xlabs_v1 comes as Darktrace reported similar targeting activities against misconfigured Jenkins instances in their honeypot network. "The presence of game-specific DoS techniques further highlights that the gaming industry continues to be extensively targeted by cyber attackers," Darktrace noted. "This botnet has likely already been used against game servers, serving as a reminder for server operators to ensure appropriate mitigations are in place."
For device owners and administrators, the implications are clear. Any device running ADB should have this service disabled unless absolutely necessary for development purposes. Network segmentation can help contain potential infections, while regular security audits can identify exposed services before threat actors do. Game server operators should implement robust DDoS mitigation strategies capable of handling the 21 different attack variants xlabs_v1 can deploy.
The discovery serves as another reminder of the evolving threat landscape in IoT security, where consumer devices continue to be weaponized for large-scale attacks. As the cybersecurity community continues to monitor this botnet's activities, device manufacturers and users alike must remain vigilant against these increasingly sophisticated threats.
Comments
Please log in or register to join the discussion