University of Toronto researchers demonstrate how GPU Rowhammer attacks can escalate to full system compromise without requiring IOMMU disablement, prompting NVIDIA to consider updating security guidance.
A new attack dubbed GPUBreach demonstrates that GPU Rowhammer attacks can escalate from data corruption to full system compromise, even with IOMMU protection enabled. Developed by researchers at the University of Toronto, the attack exploits Rowhammer-induced bit flips in GDDR6 memory to corrupt GPU page tables and ultimately gain root-level access to systems running NVIDIA GPUs.

How GPUBreach works
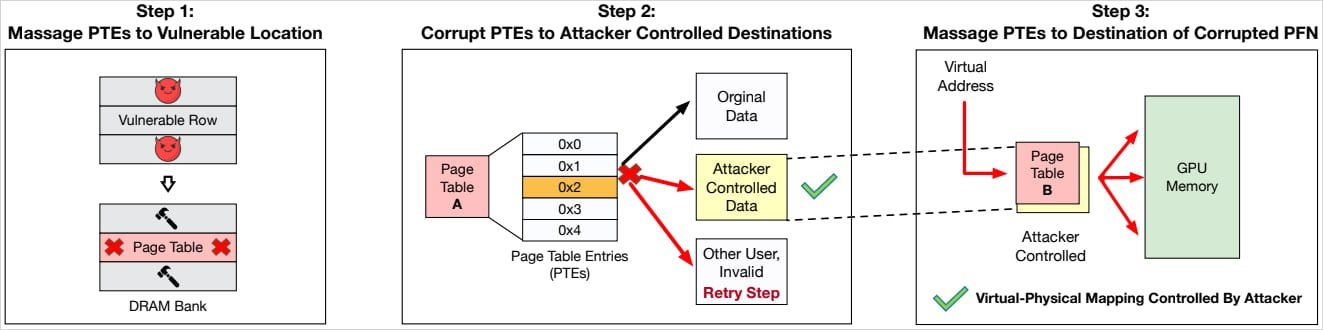
The attack chain begins with an unprivileged CUDA kernel that induces Rowhammer bit-flips in GPU GDDR6 memory. These bit-flips corrupt GPU page table entries (PTEs), granting the attacker arbitrary read/write access to GPU memory. The researchers then discovered memory-safety vulnerabilities in the NVIDIA driver that can be exploited to chain this GPU-side access into CPU-side privilege escalation.
"GPUBreach shows that GPU Rowhammer attacks can move beyond data corruption to real privilege escalation," the researchers explain. "By corrupting GPU page tables, an unprivileged CUDA kernel can gain arbitrary GPU memory read/write, and then chain that capability into CPU-side escalation by exploiting newly discovered memory-safety bugs in the NVIDIA driver."
Why IOMMU protection isn't enough
Input-Output Memory Management Unit (IOMMU) is designed to protect against direct memory access attacks by controlling which memory regions devices can access. However, GPUBreach demonstrates that IOMMU alone cannot prevent this attack vector.
"The result is system-wide compromise up to a root shell, without disabling IOMMU, unlike contemporary works, making GPUBreach a more potent threat," the researchers note. This finding is particularly concerning because most modern systems leave IOMMU enabled as a critical security boundary.
Technical demonstration
The researchers successfully demonstrated GPUBreach on an NVIDIA RTX A6000 GPU with GDDR6 memory. This GPU model is widely deployed in AI development and training workloads, making the attack particularly relevant to enterprise and research environments.
Comparison to previous GPU attacks
GPUBreach builds upon the team's earlier work on GPUHammer, which was the first practical demonstration of GPU Rowhammer attacks. While GPUHammer showed that bit-flips in GPU memory were possible, GPUBreach takes the threat significantly further by demonstrating privilege escalation capabilities.
Disclosure and vendor response
The University of Toronto team reported their findings to NVIDIA, Google, AWS, and Microsoft on November 11, 2025. Google acknowledged the report and awarded the researchers a $600 bug bounty. NVIDIA stated it may update its existing security notice from July 2025 to include the newly discovered attack possibilities.
Current mitigations and limitations
The researchers emphasize that IOMMU alone is insufficient protection if GPU-controlled memory can corrupt trusted driver state. While Error Correcting Code (ECC) memory can correct single-bit flips and detect double-bit flips, it remains unreliable against the multi-bit flips that GPUBreach can induce.
"Ultimately, the researchers underlined that GPUBreach is completely unmitigated for consumer GPUs without ECC," highlighting the limited options available to average users.
Availability of research details
The full technical paper, along with a GitHub repository containing reproduction packages and scripts, will be published on April 13, 2026, when the researchers present their findings at the IEEE Symposium on Security & Privacy in Oakland.
This research underscores the evolving threat landscape for GPU security and the need for more robust hardware and software protections against Rowhammer-style attacks in modern computing environments.

Comments
Please log in or register to join the discussion