Redox OS is implementing capability-based security by moving namespace management to userspace and treating CWD as a capability, simplifying the kernel and enabling advanced sandboxing features.
Redox OS is undergoing a fundamental security transformation through its "Capability-based security for Redox" project, funded by NGI Zero Commons and NLnet. This initiative, led by Ibuki Omatsu, represents a significant architectural shift that moves complex namespace management out of the kernel and treats the current working directory (CWD) as a capability rather than a simple string path.
The Evolution of File Access in Redox OS
To understand this transformation, we need to examine how file access worked in Redox OS before capabilities. The system relied on a kernel-managed namespace where schemes (resource providers) were registered and accessed through scheme-rooted paths like /scheme/file/home/user/file.txt. The kernel held all scheme names as strings and parsed paths to identify target schemes, creating a complex and potentially vulnerable system.
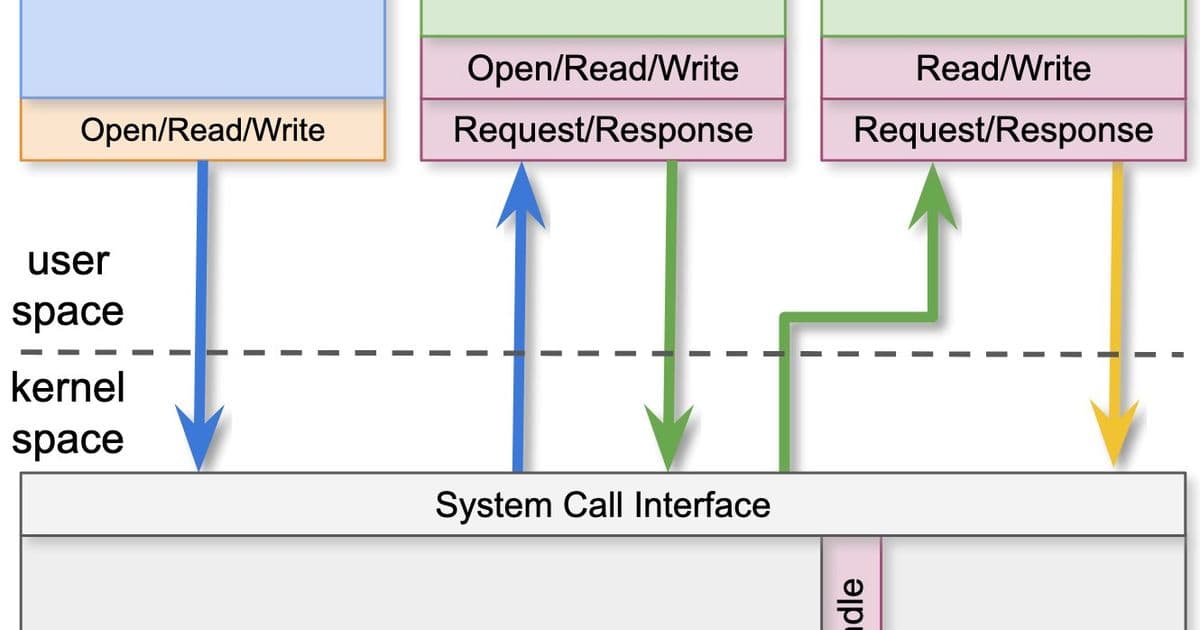
In this previous design, the namespace existed in the kernel and was bound to processes by integer IDs. When an application called open("/home/user/some_file"), the relibc runtime would convert the path to a scheme-rooted path, the kernel would extract the scheme name, verify it existed in the process's namespace, and then route the request to the appropriate scheme service.
Introducing the Namespace Manager in Userspace
The new architecture introduces a Namespace Manager (nsmgr) as an userspace scheme-type service daemon that sits between applications and other schemes. This represents a crucial shift from kernel-managed to userspace-managed namespaces. The namespace is now represented as a file descriptor managed by relibc's redox-rt runtime rather than just an ID bound to the process.
This design leverages the openat system call as its foundation. When an application calls open("/home/user/some_file"), relibc converts the path to a scheme-rooted path and calls openat with the process's namespace file descriptor as the dir_fd. The nsmgr daemon receives this request, extracts the target scheme name, verifies it's registered in the namespace, and routes the request to the appropriate scheme.
Benefits of the New Architecture
The transition to userspace namespace management brings several significant advantages:
Simplified Kernel: The kernel no longer needs to hold scheme names as strings or parse paths. It simply dispatches system call requests based on the directory file descriptor, dramatically reducing complexity and the attack surface.
Enhanced Security: By moving complex scheme and namespace management out of the kernel, the system becomes more secure and stable. The kernel's reduced responsibility means fewer potential bugs and vulnerabilities.
Anonymous Scheme Creation: Schemes are now created anonymously in the kernel, eliminating the need for the kernel to know any scheme names. This further simplifies the kernel's role to basic request dispatching.
CWD as a Capability
Perhaps even more revolutionary is the treatment of the current working directory as a capability. Rather than storing CWD as a simple string path, relibc now holds it as a file descriptor. When applications pass relative paths to open or use AT_FDCWD with the libc openat function, relibc calls its internal openat using the CWD file descriptor.
This approach enables several powerful features:
Path Processing Without Conversion: Relative paths can be processed without converting them to absolute paths, eliminating the overhead and complexity of path reconstruction.
O_RESOLVE_BENEATH Support: The system can now support the O_RESOLVE_BENEATH flag with simple implementation. When this flag is set on a file descriptor, the scheme limits the use of ../ to prevent escaping the sandbox.
Sandbox Enforcement: The CWD file descriptor can be used as a sandbox by restricting absolute path access via the namespace, providing a natural mechanism for directory-based confinement.
The Role of relibc and redox-rt
Central to this architecture is relibc, the C standard library that targets Redox OS while also supporting multiple operating systems. For Redox, relibc provides redox-rt, which serves as a translation layer from Redox services to POSIX-compliant services. This compatibility layer performs functions typically assigned to the kernel in other Unix-like systems, including path translation and file descriptor management.
In the new design, threads and processes are managed as file descriptors by redox-rt, aligning with the capability-based approach. The Cwd structure now contains both a path string (for getcwd() compatibility) and a file descriptor guard, though the string caching may change as more sandboxing features are implemented.
Implications for Future Security
This project represents a significant step toward capability-based security in Redox OS. By reimplementing namespace and CWD management using capabilities, the system gains the ability to support more modern security features and sandboxing mechanisms. The architecture naturally lends itself to directory-based confinement, path resolution restrictions, and other security primitives that are difficult or impossible to implement with traditional string-based path management.
As Redox OS continues to evolve toward capability-based security, users can expect more robust sandboxing features, better isolation between processes, and a more secure foundation for applications. The simplified kernel design also means better performance and reliability, as the kernel's attack surface has been significantly reduced.
This transformation demonstrates how rethinking fundamental system concepts like namespaces and working directories through the lens of capability-based security can lead to more secure, simpler, and more powerful operating system architectures. Redox OS is positioning itself at the forefront of modern operating system security design, showing how microkernel architectures can be enhanced with capability-based principles to create systems that are both powerful and inherently secure.
Comments
Please log in or register to join the discussion