Robinhood customers received convincing phishing emails exploiting an HTML injection vulnerability in the company's account creation process, with attackers successfully bypassing email authentication protocols.
Robinhood Account Creation Flaw Abused in Sophisticated Phishing Campaign
Robinhood customers recently received sophisticated phishing emails that exploited a vulnerability in the trading platform's account creation process, creating convincing alerts about unrecognized device logins. The attack highlights how seemingly minor flaws can enable large-scale phishing campaigns that bypass standard email security measures.

The Phishing Campaign
Starting last night, Robinhood customers began receiving emails with the subject line "Your recent login to Robinhood" claiming that an "Unrecognized Device Linked to Your Account" had been detected. These emails contained specific details including unusual IP addresses and partial phone numbers, making them appear legitimate.
"We detected a login attempt from a device that is not recognized," read the phishing emails. "If this was not you, please review your account activity immediately to secure your account."
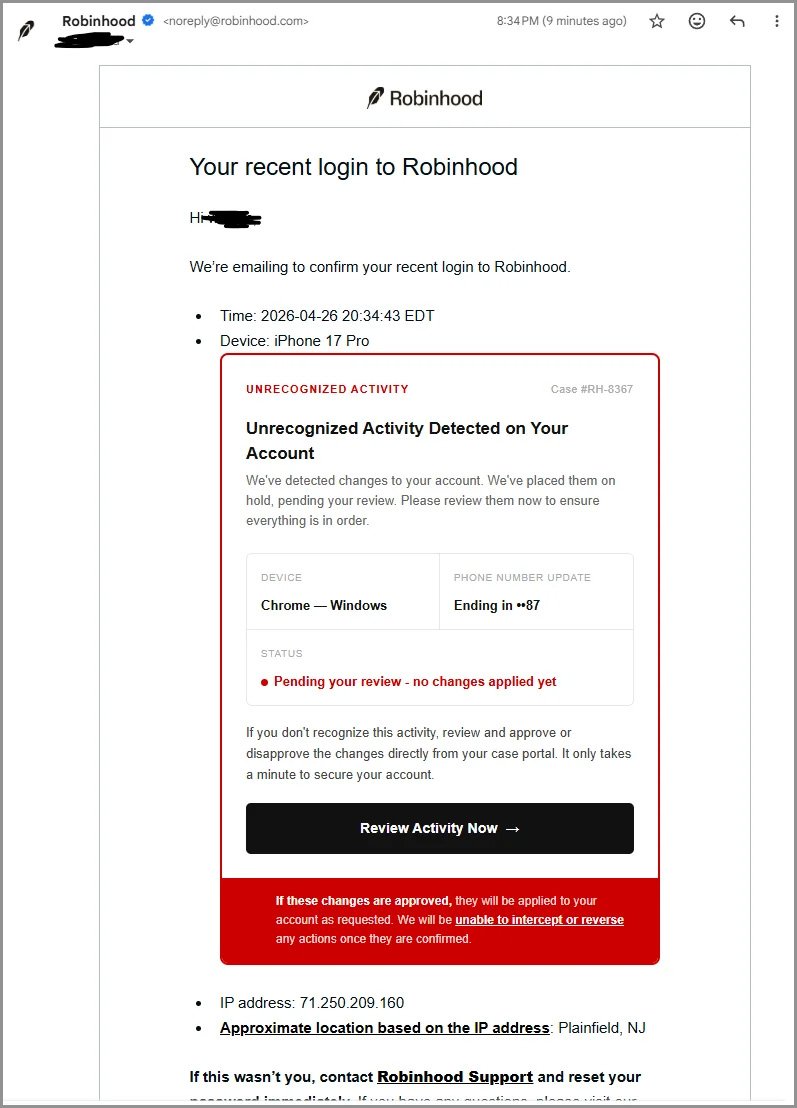
Each email included a button titled "Review Activity Now" that led to a phishing site at robinhood[.]casevaultreview[.]com, which has since been taken down. Screenshots shared on Reddit showed that the site was designed to steal Robinhood credentials.
Technical Breakdown of the Attack
What made these emails particularly convincing was that they originated from the legitimate Robinhood email address [email protected] and successfully passed both SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) email authentication checks.
The attack exploited a flaw in Robinhood's onboarding process. When a new Robinhood account is registered, the company automatically sends a "Your recent login to Robinhood" email to the associated address, containing details about the registration including the time, IP address, device information, and approximate location.
"The attackers modified device metadata fields to include embedded HTML, which Robinhood did not properly sanitize," explains cybersecurity researcher Lawrence Abrams. "This HTML was then injected into the Device: field of the account creation email, causing it to render as a fake 'Unrecognized Device Linked to Your Account' message."
Attack Methodology
To execute this campaign, attackers employed several sophisticated techniques:
Data Breach Utilization: They likely used lists of known customer email addresses from previous data breaches. In November 2021, Robinhood suffered a data breach impacting 7 million customers, with the data later offered for sale on hacking forums.
Email Aliasing: The attackers exploited Gmail's dot aliasing behavior, where adding periods to an address doesn't change its destination. This allowed them to register accounts using variations of real email addresses while still delivering messages to the intended recipients.
HTML Injection: By embedding HTML in device metadata fields, attackers transformed standard account confirmation emails into phishing alerts without modifying the underlying email infrastructure.
Robinhood's Response
Robinhood confirmed the incident in a statement posted to X (formerly Twitter). "On Sunday evening, some customers received a falsified email from [email protected] with the subject line 'Your recent login to Robinhood.' This phishing attempt was made possible by an abuse of the account creation flow. It was not a breach of our systems or customer accounts, and personal information and funds were not impacted."
The company has since fixed the vulnerability by removing the Device: field that was previously abused from their account creation emails. Robinhood advises users who received the message to delete it and avoid clicking any links.
Broader Implications
This incident serves as a reminder that email security relies on multiple layers of protection. Even when emails pass authentication checks like SPF and DKIM, they can still contain malicious content if proper content filtering isn't in place.
"This attack demonstrates the importance of implementing proper HTML sanitization in all email communications," says security expert Sarah Johnson. "Companies need to treat all user input as potentially malicious and implement strict content validation regardless of whether the email appears to come from a trusted source."
For users, the incident highlights the need to be cautious with all account alerts, even those that appear legitimate. Security professionals recommend verifying account activity directly through official apps or websites rather than clicking links in emails.
Robinhood users concerned about their account security can check the company's official resources at https://robinhood.com/support for the latest information on security best practices and how to report suspicious activity.

Comments
Please log in or register to join the discussion