Microsoft warns of Storm-2561's sophisticated phishing campaign that hijacks search results to distribute trojanized VPN clients, stealing credentials through fake sign-in dialogs and abusing GitHub for hosting malicious installers.
Microsoft has issued a warning about Storm-2561, a threat actor that's exploiting search engine optimization (SEO) poisoning to distribute trojanized VPN clients and steal user credentials. The campaign, which Microsoft's Threat Intelligence and Microsoft Defender Experts teams observed in mid-January 2026, represents a sophisticated evolution in credential theft tactics.
How the Attack Works
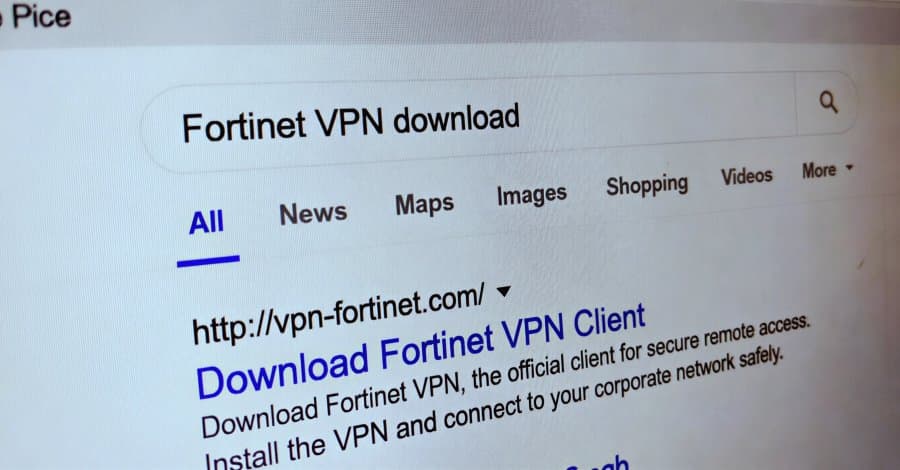
The campaign begins when users search for legitimate enterprise VPN software on Bing. Instead of reaching the official vendor sites, victims are redirected to attacker-controlled websites hosting malicious ZIP files. These sites are designed to appear convincing, often using domain names that closely mimic legitimate VPN providers.
Once downloaded, the ZIP file contains an MSI installer that masquerades as legitimate VPN software. However, during installation, it sideloads malicious DLL files that deploy the Bumblebee loader. The ultimate payload is a variant of the Hyrax information stealer, specifically engineered to harvest VPN credentials from the victim's machine.
The Social Engineering Layer
What makes this campaign particularly effective is its multi-layered approach to deception. After installation, victims are presented with a fake but convincing VPN sign-in dialog. When users enter their credentials, they're shown an error message and instructed to download the legitimate VPN client instead.
In some cases, victims are even redirected to the official VPN website after entering their credentials, making the entire experience feel legitimate and reducing suspicion. This psychological manipulation is a hallmark of Storm-2561's tactics, which deliberately exploit trust in search engine rankings and software branding.
Technical Infrastructure and Persistence
The attackers abuse trusted platforms like GitHub to host their malicious installer files, lending an air of legitimacy to the downloads. Once installed, the malware establishes persistence by modifying the Windows RunOnce registry key, ensuring it executes automatically after every system reboot.
Microsoft notes that the malicious components are digitally signed by "Taiyuan Lihua Near Information Technology Co., Ltd.," adding another layer of apparent legitimacy to the attack.
Attribution and Campaign History
Storm-2561 has been active since May 2025, with a documented history of propagating malware through SEO poisoning while impersonating popular software vendors. The threat actor's campaigns were first documented by Cyjax, highlighting the use of SEO poisoning to redirect users searching for software from companies like SonicWall, Hanwha Vision, and Pulse Secure.
A subsequent iteration was disclosed by Zscaler in October 2025, where the group exploited users searching for legitimate software on Bing to propagate a trojanized Ivanti Pulse Secure VPN client via bogus websites.
Mitigation and Protection
Microsoft has taken steps to neutralize the operation by taking down the attacker-controlled GitHub repositories and revoking the legitimate certificate used to sign the malicious components. However, organizations and users should implement additional protective measures:
- Multi-factor authentication (MFA): Enable MFA on all accounts to add an extra layer of security even if credentials are compromised
- Software verification: Always verify software authenticity before installation, particularly when downloading from search results
- Caution with search results: Be skeptical of search engine results, especially for enterprise software, and navigate directly to official vendor websites
- Security awareness training: Educate users about SEO poisoning tactics and the risks of downloading software from unverified sources
This campaign exemplifies the evolving sophistication of financially motivated cybercrime operations, where attackers combine technical exploitation with psychological manipulation to achieve their objectives. The abuse of trusted platforms and legitimate digital certificates demonstrates how threat actors continue to adapt their tactics to evade detection and exploit user trust.
Comments
Please log in or register to join the discussion