A comprehensive analysis of critical security vulnerabilities discovered in Zero Motorcycles' firmware, update mechanisms, and mobile application, revealing how the rush to market with connected vehicles has created significant safety risks that remain unaddressed by the manufacturer.
The electric vehicle revolution represents one of the most significant technological shifts in personal transportation since the advent of the internal combustion engine. Yet as we embrace this cleaner, more efficient future, we confront an uncomfortable reality: the very connectivity that makes these vehicles 'smart' also creates unprecedented security vulnerabilities. The research conducted by Bureau Veritas Cybersecurity North America on Zero Motorcycles reveals a troubling pattern where innovation has demonstrably outpaced security considerations, leaving riders exposed to potentially life-threatening risks.

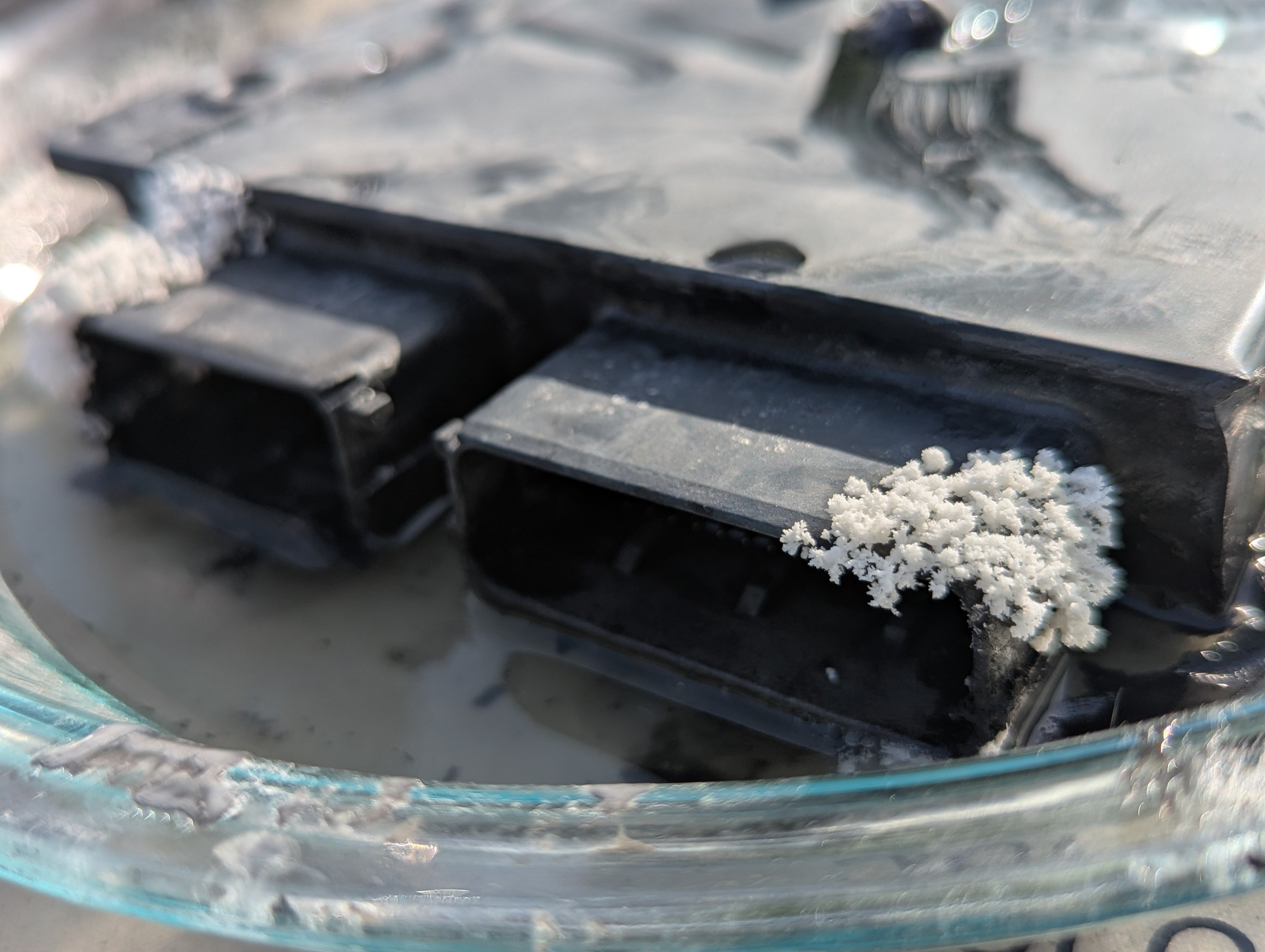
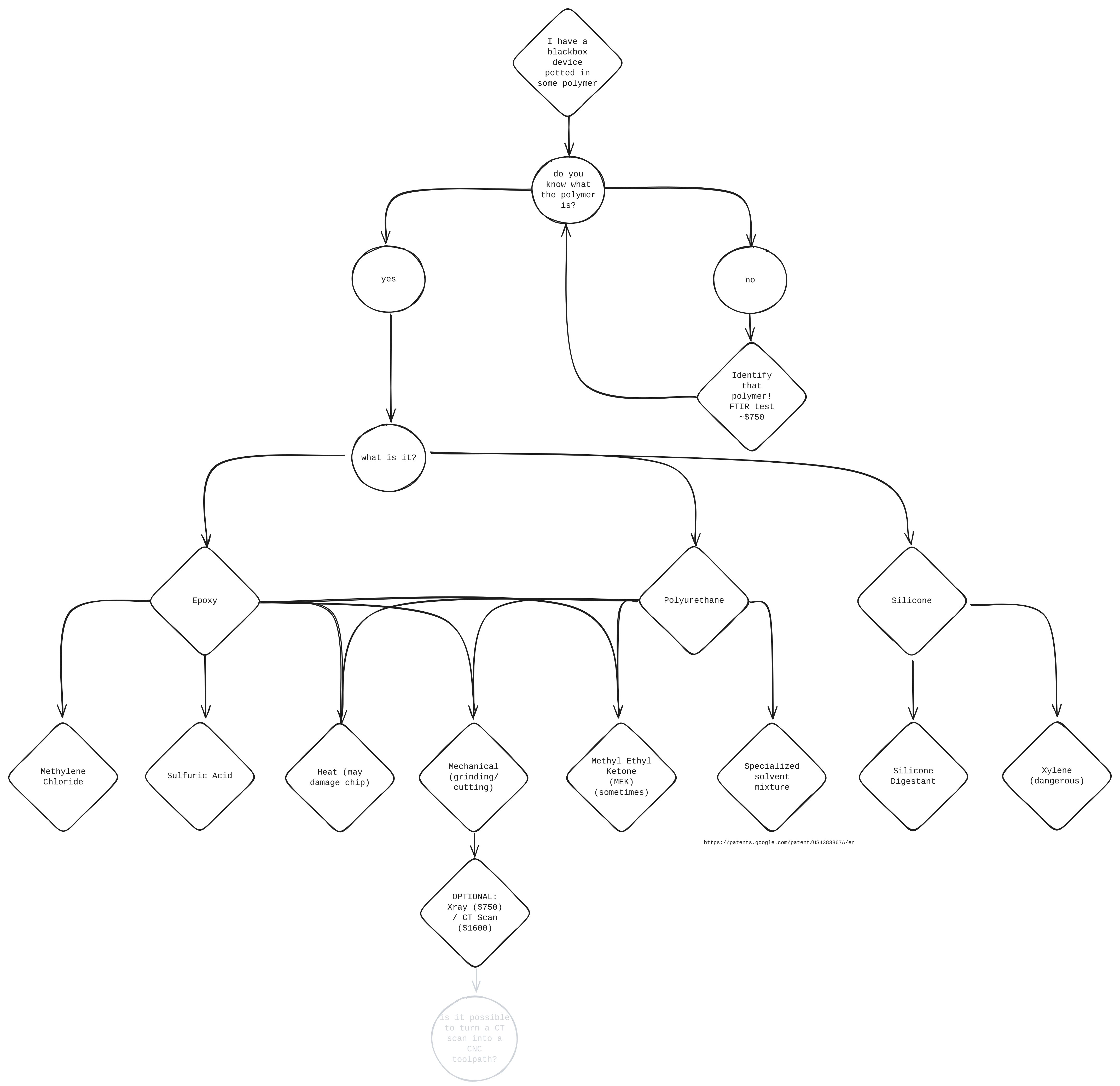
The physical security analysis of Zero motorcycles began with an ambitious attempt to depot the Main Bike Board (MBB), essentially the motorcycle's electronic control unit. What researchers discovered was a matryoshka-like construction with the PCB encased first in resin, then in an ABS plastic shell. The initial attempt using methylene chloride failed, leading to a fascinating detour into chemical engineering as the team identified that the board was actually potted with polyurethane rather than epoxy, as originally assumed. This discovery highlights a fundamental challenge in hardware security research: the physical barriers manufacturers implement are often more sophisticated than they appear, requiring specialized knowledge and potentially dangerous chemicals to bypass.

The depotting process, ultimately abandoned due to safety concerns with the required chemical cocktail, represents the first layer of what would prove to be a multi-faceted security architecture. Yet this initial physical barrier proved to be the most robust component of Zero's security posture, as researchers would soon discover far more significant vulnerabilities in the digital realm.
The Zero Motorcycles Android application, responsible for over-the-air (OTA) updates and bike connectivity, revealed itself to be a treasure trove of security flaws. Within the BuildConfig, researchers discovered hardcoded URLs and bearer tokens for the firmware update server, essentially providing the keys to the kingdom without requiring authentication. The decompiled Java code showed that firmware downloads required only a GET request with proper headers and a parameter that could be easily guessed, given the sequential nature of firmware version numbers.
This vulnerability allowed researchers to download firmware binaries simply by incrementing version numbers, bypassing any meaningful authentication or authorization mechanisms. The downloaded firmware packages contained not only the binaries but also linker map files, which provided function names that dramatically simplified the reverse engineering process. This represents a critical security failure: the inclusion of debugging symbols in production firmware essentially provides attackers with a roadmap of the system's internal architecture.
The firmware analysis revealed authentication mechanisms with hardcoded salts like "TODO:changeThisS"—a clear indication that developers had intended to implement proper security but either forgot or ran out of time before release. More concerning was the discovery of a passcode server reference, leading to the identification of Will Brunner, a Zero employee whose credentials could potentially be used to escalate privileges on the motorcycle's systems.
The firmware verification process proved to be particularly alarming. Upon receiving a firmware update, the motorcycle performs only a single check: comparing the SHA-512 hash of the received firmware against an expected hash. This hash is computed using a static salt that is identical across all motorcycles, meaning that once discovered, it can be used to sign arbitrary firmware updates. The researchers demonstrated this with a simple seven-line Python script, highlighting how easily firmware could be maliciously modified.
The attack surface expands further when considering the CAN bus communication between motorcycle components. The research identified that neither the CANopen SDO protocol used during normal operation nor the custom protocol used in Bootloader Mode included any authentication mechanisms. This means that anyone with physical access to the OBD-2 port could potentially upload malicious firmware to critical components like the Battery Management System (BMS) and Battery Monitoring Unit (BMU).
The researchers constructed a proof-of-concept attack using a Raspberry Pi Zero W 2 with a CAN bus adapter, creating a handheld device capable of interfacing with the motorcycle's systems for approximately $100—roughly one-thirteenth the cost of an official OBD-2 harness. This accessibility dramatically lowers the barrier to entry for potential attackers.
{{IMAGE:6}}
Perhaps most concerning was the potential for persistent malware implantation. The XMC4500 and XMC4800 microcontrollers used in Zero motorcycles contain significantly more memory than is utilized by the firmware, leaving ample space for malicious code. Researchers identified specific code caves—unused regions of memory—large enough to accommodate sophisticated implants. By hooking into legitimate functions like ZeroMbbManageCCMTask, which handles cellular communication and has access to GPS data, attackers could create a persistent presence that would be extremely difficult to detect or remove.
The envisioned C2 (command and control) implant could receive commands over 4G LTE, allowing remote attackers to:
- Apply maximum regenerative braking or engage reverse unexpectedly, potentially throwing the rider
- Apply maximum torque at low speeds, potentially causing wheelies
- Open contactors, cutting power to the motors and stranding the rider
- Disable safety monitoring while modifying operational parameters
These capabilities echo the sophisticated control demonstrated by malware like Stuxnet, which famously targeted industrial control systems. The potential consequences for motorcycle safety are particularly severe given the physical risks involved.
The disclosure process reveals another layer of the problem. Despite multiple attempts to contact Zero Motorcycles through official channels over a 13-month period, the researchers received no response. This lack of engagement is particularly troubling given that the vulnerabilities identified could potentially compromise rider safety. The eventual response, coming only after CERT/CC intervention, acknowledged the issues but provided no concrete timeline for resolution.
{{IMAGE:7}}
The legal and ethical dimensions of this research warrant careful consideration. The researchers cite several legal protections that support their disclosure, including Van Buren v. United States (2021), which narrowed the Computer Fraud and Abuse Act's scope to exclude good-faith security research. They also reference DMCA exemptions for security research on motor vehicles, which permit circumvention of technological protection measures for testing purposes.
However, the broader implications extend beyond legal compliance. The research highlights a fundamental tension in the Internet of Things (IoT) ecosystem: the pressure to bring innovative products to market quickly often results in security being treated as an afterthought rather than a core design principle. This is particularly concerning in safety-critical systems like vehicles, where security failures can have life-or-death consequences.
Counter-perspectives might argue that motorcycles, as relatively specialized vehicles compared to automobiles, represent a lower-priority target for attackers. Additionally, some might suggest that the physical access required for many of these attacks limits their real-world applicability. However, as the research demonstrates, the barrier to obtaining physical access—particularly through OBD-2 ports that are increasingly accessible in modern designs—continues to decrease.
Moreover, the argument that specialized vehicles are less attractive targets ignores the potential for attacks that extend beyond individual motorcycles. The envisioned C2 infrastructure could potentially create botnets of compromised vehicles, creating systemic risks that extend beyond individual safety concerns.
The Zero Motorcycles case study serves as a cautionary tale for the entire EV industry. As vehicles become increasingly connected and software-defined, security must be integrated into the design process from the outset rather than bolted on as an afterthought. This includes implementing proper cryptographic mechanisms for firmware verification, establishing authenticated communication channels between components, and designing secure update mechanisms that cannot be easily bypassed.
The research also highlights the need for more robust vulnerability disclosure processes in the automotive industry. The 13-month period during which Zero Motorcycles failed to respond to researchers represents a significant failure to address known safety issues. Manufacturers must establish clear channels for receiving and responding to security research, with defined SLAs and transparent communication about remediation timelines.
Ultimately, the security of connected motorcycles is not merely a technical issue but a matter of public safety. As we accelerate toward an electric, connected transportation future, we must ensure that innovation does not come at the cost of security. The Zero Motorcycles vulnerabilities serve as a reminder that in our rush to embrace the future of transportation, we cannot afford to neglect the fundamental security principles that protect users from harm.

Comments
Please log in or register to join the discussion