Modern access security requires continuous device verification beyond identity checks to prevent credential reuse and session hijacking attacks.

For years, security teams treated identity verification as the cornerstone of access control. But as cybersecurity expert David Lindner observes: "The assumption that valid authentication equals trustworthy access crumbles when endpoints become compromised mid-session." This vulnerability gap is increasingly exploited through session hijacking and credential reuse attacks, where legitimate identities access resources from untrusted devices.
Modern work patterns exacerbate the challenge. Employees routinely switch between corporate laptops, personal devices, and third-party endpoints across multiple networks. Traditional security models struggle with this fluidity because they primarily validate identity at login while overlooking continuous device integrity checks. Verizon's 2026 Data Breach Investigations Report confirms stolen credentials remain involved in 44.7% of breaches despite robust authentication measures.
The limitations of identity-centric security become apparent when:
- Device risk evolves post-authentication: Endpoints can develop security gaps through configuration drift, disabled controls, or delayed updates long after initial access
- Legacy protocols lack context: Non-browser workflows and remote access tools often bypass modern conditional access policies
- Zero Trust implementations stall: Many organizations implement strong identity controls but lack equivalent device trust mechanisms
"Identity tells us who's accessing resources, but not whether their endpoint remains trustworthy," explains cybersecurity architect Maya Rodriguez. "Attackers exploit this by hijacking valid sessions from compromised devices rather than breaking authentication."
Practical security enhancements focus on closing these gaps:
Continuous Verification Framework
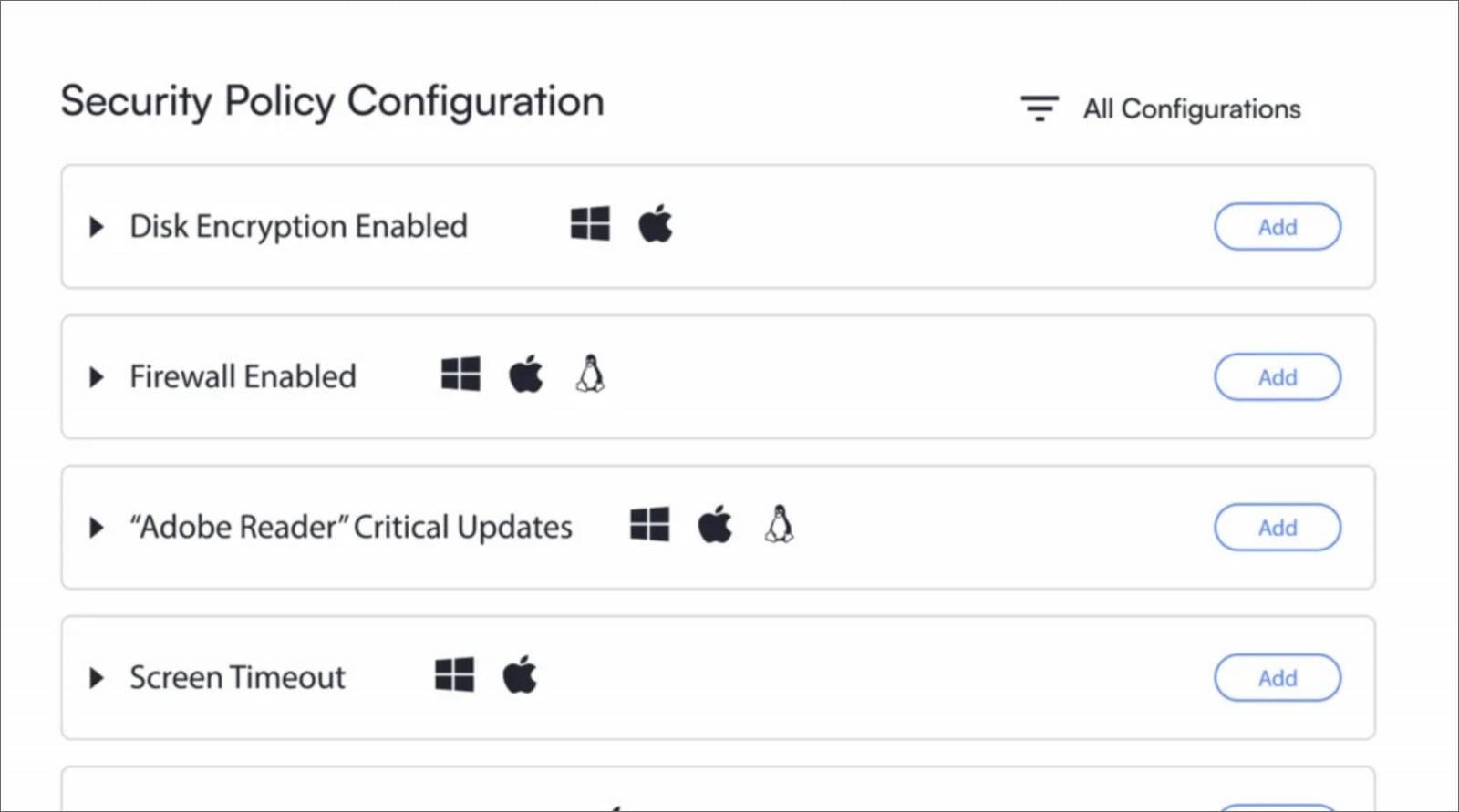
Implement real-time device health checks throughout sessions, not just at login. Solutions like InfiniPoint extend Zero Trust principles by validating both user identity and endpoint security posture continuously across Windows, macOS, Linux, and mobile platforms.
Device-Based Access Controls
- Enroll approved hardware through enterprise mobility management systems
- Limit devices per user and differentiate between corporate/personal endpoints
- Block access attempts from non-compliant devices even with valid credentials
Proportional Enforcement
Instead of complete access revocation for minor policy violations, implement conditional restrictions like:
- Reduced data permissions during grace periods
- Temporary access to remediation tools
- Selective application blocking
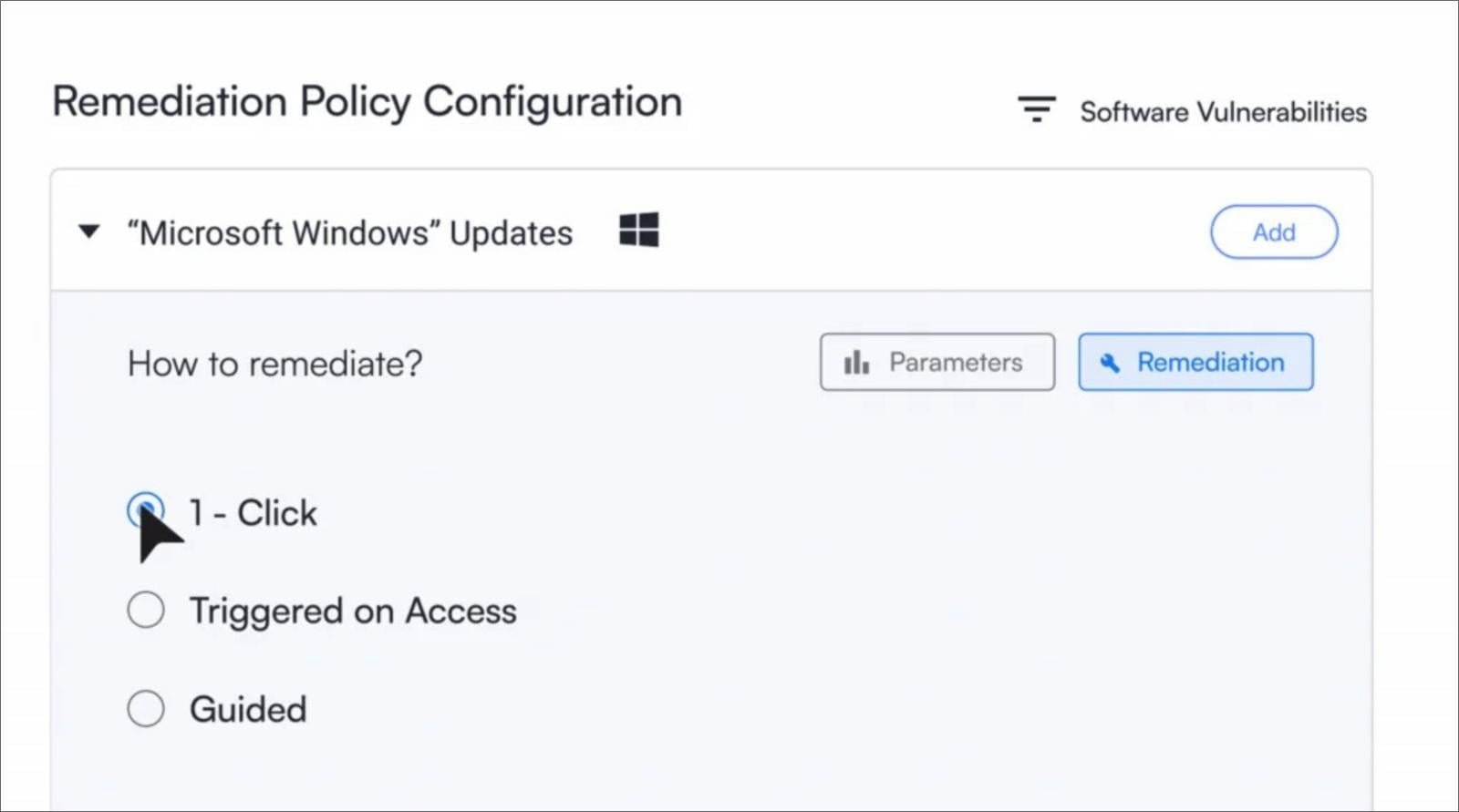
Self-Service Remediation
Provide users with one-click tools to resolve common compliance issues like enabling disk encryption or installing updates. This maintains security standards while reducing IT ticket volume by up to 70% according to enterprise case studies.
As Lindner concludes: "The future of access security isn't stronger identity gates—it's continuous verification ecosystems that dynamically adjust trust based on real-time device integrity." Security teams should prioritize solutions that unify identity and endpoint signals through integrated platforms rather than siloed tools.

Comments
Please log in or register to join the discussion