An in‑depth look at the systemic weaknesses of password‑based authentication, the mechanics of WebAuthn passkeys, their security benefits, practical deployment considerations, and the challenges that remain.
Why Passwords Fail and How Passkeys Offer a Viable Path Forward
Published February 6 2025
The Core Problem with Passwords
Most high‑profile data breaches can be traced back to compromised credentials. Whether the leak originates from a phishing site that mimics a bank’s login page, a key‑logging trojan that records every keystroke, or a server‑side breach that exposes a password hash database, the underlying issue is the same: passwords are a shared secret that must travel—often in a weakened form—between user and service. This creates multiple attack surfaces:
- Phishing – Users are tricked into entering their credentials on a look‑alike domain. Even the most security‑aware individual can fall victim when the attacker controls the entire page.
- Malware – Keyloggers and more sophisticated injectors can capture passwords before they are encrypted, or hook cryptographic libraries to read plaintext before it leaves the process.
- Man‑in‑the‑Middle (MitM) – Rogue TLS certificates issued by compromised certificate authorities enable attackers to decrypt traffic and harvest passwords.
- Database Exposure – Misconfigured storage buckets, SQL injection, or outright theft of password‑hash dumps give attackers a treasure trove of reusable credentials.
Because a password is static until the user changes it, a single compromise can be reused indefinitely, fueling a black market for stolen credentials.
Cryptographic Signatures as an Alternative
A digital signature solves the “shared secret” problem by replacing it with a pair of keys:
- The private key never leaves the user’s device.
- The public key is stored by the service.
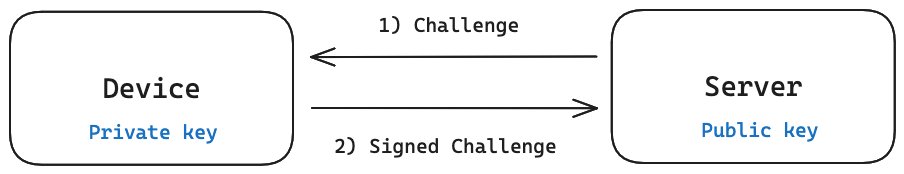
When a service wants to verify a user’s identity, it sends a random challenge. The device signs that challenge with the private key, and the service validates the signature using the stored public key. Because the private key never traverses the network and is bound to the service’s domain, an attacker cannot replay the signature on a different site.
The Web Authentication (WebAuthn) standard implements exactly this flow and brands the resulting credentials as passkeys.

How Passkeys Work in Practice
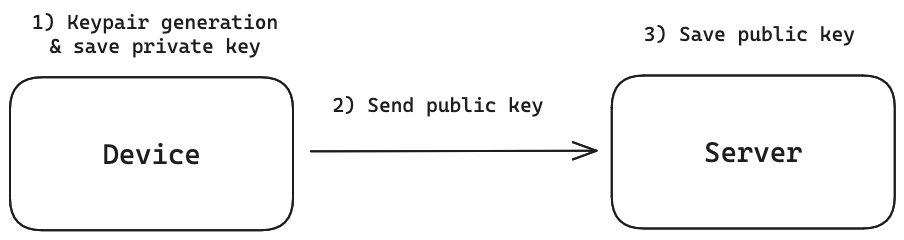
- Registration – The user creates a new credential on their device. The device generates a private/public key pair, stores the private key in a secure enclave or a platform‑managed keychain, and sends the public key to the server.
- Login – The server issues a fresh, unpredictable challenge. The device signs the challenge with the private key, optionally after the user authenticates locally (PIN, biometrics, or hardware button). The server verifies the signature with the stored public key.
- Phishing Resistance – Because the signature is tied to the originating domain, a malicious site cannot obtain a valid signature for a victim’s bank.
- Device Portability – Software‑based passkeys can be synced across a user’s devices via encrypted cloud storage, while hardware security keys (e.g., YubiKey) remain bound to a single device.
A live demonstration of this flow is available at webauthn.io, and the official WebAuthn tutorial on passkey registration can be found on web.dev.
Practical Benefits for Users and Providers
| Aspect | Passwords | Passkeys |
|---|---|---|
| User experience | Remember dozens of complex strings, frequent resets | One‑tap or biometric unlock, no memorization |
| Phishing resistance | None – credentials are entered on any site | Domain‑bound signatures prevent reuse on impostor sites |
| Credential leakage | Database breach yields reusable passwords | Breach reveals only public keys; private keys remain on devices |
| Recovery | Email reset links, often insecure | Recovery depends on the passkey manager; backup devices or synced cloud keys are recommended |
Providers also benefit because a stolen credential database is far less valuable to attackers, reducing the incentive for large‑scale exfiltration.
Remaining Challenges and Counter‑Perspectives
1. Recovery and Device Loss
If a user loses the device that holds their private keys, they must rely on a secondary recovery method. Most passkey ecosystems support encrypted cloud sync, but this introduces a new trust boundary: the cloud provider must protect the backup keys with strong encryption and multi‑factor safeguards. Organizations should still offer fallback mechanisms such as one‑time codes or magic‑link emails.
2. Compatibility with Legacy Systems
Older browsers and operating systems lack native WebAuthn support. For these cases, a hybrid approach—offering both passkeys and a traditional password fallback—may be necessary during a transition period. However, maintaining both pathways can re‑introduce the very attack vectors passkeys aim to eliminate.
3. Quantum Threats
Current passkey implementations rely on elliptic‑curve signatures (e.g., Ed25519, ES256). Quantum computers capable of running Shor’s algorithm could eventually break these schemes. The NIST post‑quantum signature standard ML‑DSA (FIPS 204) is already published, and the FIDO Alliance is evaluating its integration into future WebAuthn versions. Until quantum‑resistant algorithms are widely deployed, passkeys remain more secure than passwords but are not immutable.
4. Attacks on the Private‑Key Store
Malware that compromises a device’s secure enclave or extracts the master password of a cloud‑synced keychain could still expose private keys. Pairing a software passkey manager with a hardware security key for the second factor mitigates this risk, offering a layered defense similar to traditional 2FA.
Transition Strategies for Organizations
- Commit to a password‑free future – Remove stored password hashes once users have registered a passkey. Offer a one‑time magic link to guide users toward registration.
- Educate users – Provide clear instructions on how to set up passkeys on common platforms (iOS, Android, Windows, macOS) and explain recovery options.
- Support fallback flows – Until adoption is universal, maintain a secondary authentication channel that does not re‑introduce reusable secrets.
- Monitor standards evolution – Keep an eye on FIDO’s roadmap for post‑quantum algorithms and plan for key rotation when quantum‑resistant signatures become mainstream.
Closing Thoughts
Passwords have become a liability that fuels a continuous cycle of breaches, resets, and user frustration. Passkeys, built on well‑understood public‑key cryptography and bound to the service’s domain, eliminate many of the systemic flaws of password‑based authentication. They are not a panacea—recovery, legacy compatibility, and future quantum threats require thoughtful mitigation—but they represent a pragmatic, deployable step toward a more secure digital identity ecosystem.
For developers interested in experimenting, the following resources are a good starting point:
- The official WebAuthn specification
- Adam Langley’s A Tour of WebAuthn blog post
- Mozilla’s guide to the Web Authentication API
Adopting passkeys today reduces the attack surface that passwords have exposed for decades. The question is no longer whether they can replace passwords, but how quickly organizations will make the transition.

Comments
Please log in or register to join the discussion