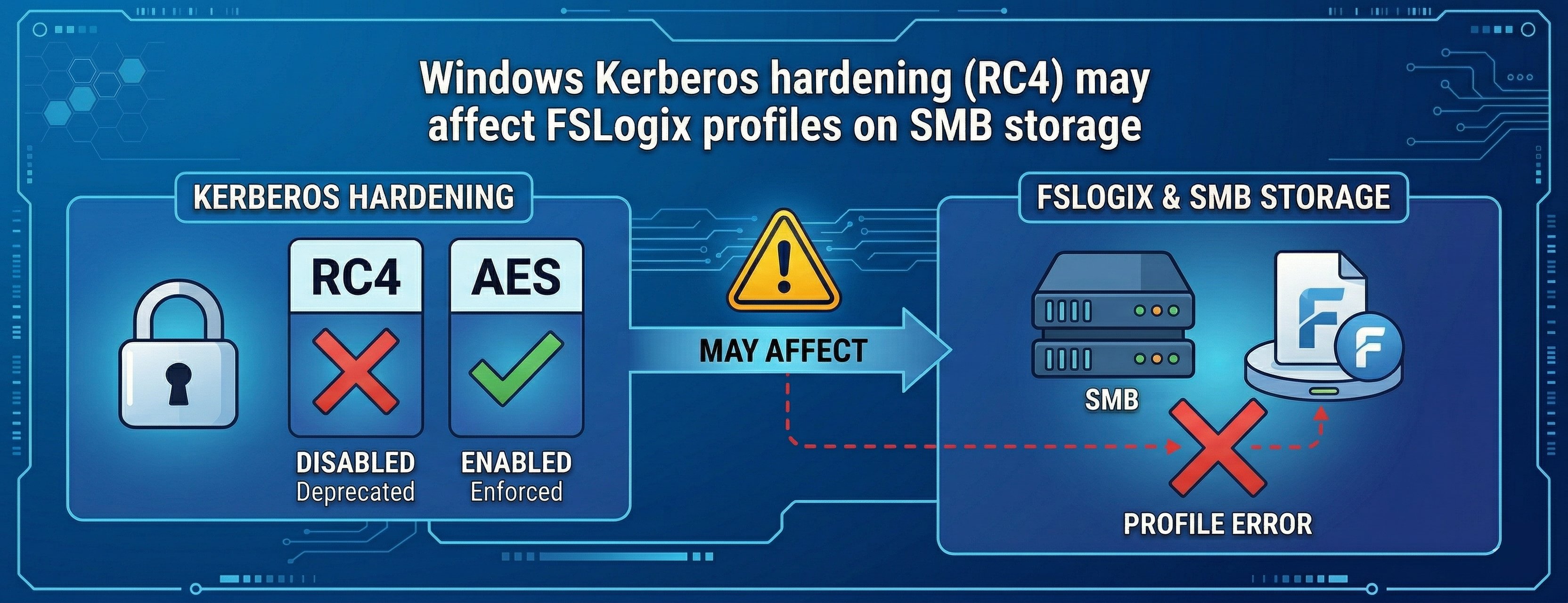
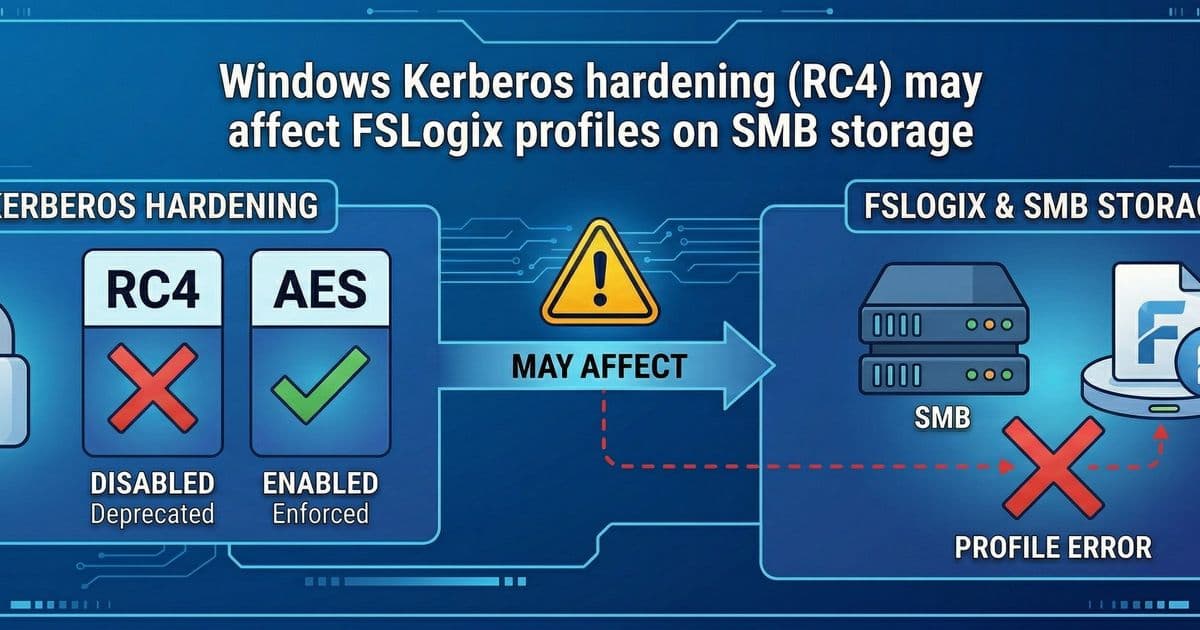
Microsoft's April 2026 Kerberos encryption change from RC4 to AES-SHA1 could disrupt FSLogix profile access on SMB storage unless you update AD configurations now.
Microsoft has announced a critical security hardening change coming in April 2026 that will alter default Kerberos encryption behavior in Windows. This change, while enhancing security, may break FSLogix profile access for organizations using SMB storage with Active Directory integration. The shift from legacy RC4 encryption to AES-SHA1 as the default for accounts without explicit encryption settings represents a significant platform change that requires immediate attention from IT administrators.
What's Changing in April 2026
Beginning with the April 2026 Windows cumulative update, Kerberos will default to AES-SHA1 encryption for Active Directory objects whose encryption type is not explicitly set (null). Previously, these accounts often defaulted to RC4, a weaker encryption algorithm that Microsoft is now deprecating for security reasons. This is a Windows platform security change, not a modification to Azure Virtual Desktop service behavior.
The rollout follows a phased approach:
- April 2026: Enforcement Phase with manual rollback - Default Kerberos behavior changes to AES-SHA1-only encryption for accounts without explicit encryption type settings. Enforcement mode is enabled by default on Windows domain controllers, though audit mode remains available as a manual rollback option until July 2026.
- July 2026: Enforcement Phase - Audit mode is removed, leaving enforcement mode as the only option.
Who's at Risk?
You may be impacted if you use Kerberos-based access to SMB storage for FSLogix profiles and have Kerberos encryption settings that are RC4-only or unset (null) for relevant AD objects or service accounts. This affects both Azure Virtual Desktop (AVD) and non-AVD environments where FSLogix profile storage depends on SMB file shares integrated with Active Directory.
If a dependent system (file server, NAS, or service account configuration) does not support AES-SHA1 for Kerberos, authentication may fail. Azure Files SMB storage with AD DS integration is specifically mentioned as requiring remediation by the end of June 2026.
What You Need to Do Now
Microsoft recommends several immediate actions:
- Identify RC4 usage and null encryption settings for AD objects tied to SMB access, including FSLogix profile storage
- Update configurations to support and prefer AES-based Kerberos encryption (AES-SHA1)
- Validate end-to-end sign-in and FSLogix profile access for both AVD and non-AVD environments
Resources for Remediation
Microsoft provides several resources to help with this transition:
- Troubleshoot Azure Files identity-based authentication and authorization issues (SMB) - Azure | Microsoft Learn
- How to manage Kerberos KDC usage of RC4 for service account ticket issuance changes related to CVE-2026-20833
- Detect and remediate RC4 usage in Kerberos
- CVE-2026-20833 - related vulnerability information
- Windows Server Blog: Beyond RC4 for Windows authentication
The Business Impact
This change represents a classic security versus compatibility tradeoff. While Microsoft is strengthening Kerberos encryption defaults to address security vulnerabilities, organizations with legacy configurations may face unexpected authentication failures. The impact could be particularly severe for businesses relying on FSLogix for user profile management in virtual desktop environments.
Organizations should prioritize this remediation, as the July 2026 deadline for audit mode removal means there's limited time to test and implement changes. The requirement for AES-SHA1 support across all dependent systems (file servers, NAS devices, service accounts) may necessitate firmware updates, configuration changes, or even hardware replacements in some cases.
For IT teams managing hybrid or multi-cloud environments, this change underscores the importance of maintaining current encryption standards and regularly auditing authentication configurations. The shift away from RC4 reflects broader industry trends toward stronger encryption and zero-trust security models.
Comments
Please log in or register to join the discussion