Cybersecurity
CISA Adds ABB B&R Automation Studio to No‑Cost Cyber Services Program
5/21/2026

Security
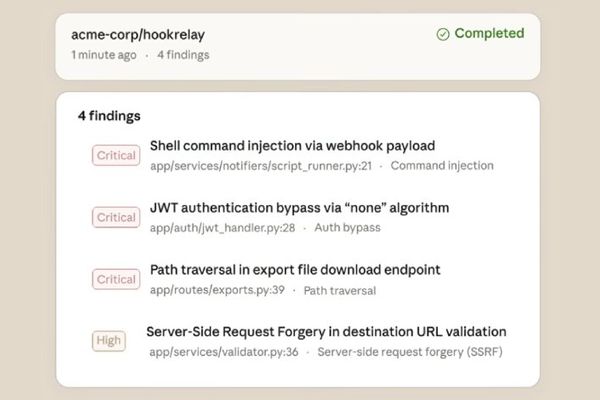
How exposed is your code? Find out in minutes—for free
4/14/2026

Vulnerabilities
GitHub Security Lab's AI-Powered Vulnerability Scanner Finds 80+ High-Impact Flaws
3/6/2026
Security
Anthropic Launches Claude Code Security for AI-Powered Vulnerability Scanning
2/21/2026