A comprehensive guide to implementing automated credential rotation in Azure, comparing cloud provider approaches and analyzing business impacts for enterprise security and compliance.
In today's complex cloud environments, managing cryptographic assets—keys, secrets, and certificates—has become a critical operational challenge. When credentials expire unexpectedly, applications fail, security trust breaks, and teams scramble for emergency solutions. Microsoft's Azure Key Vault Auto-Rotation functionality addresses this fundamental challenge by providing policy-driven, auditable automation for credential lifecycle management.
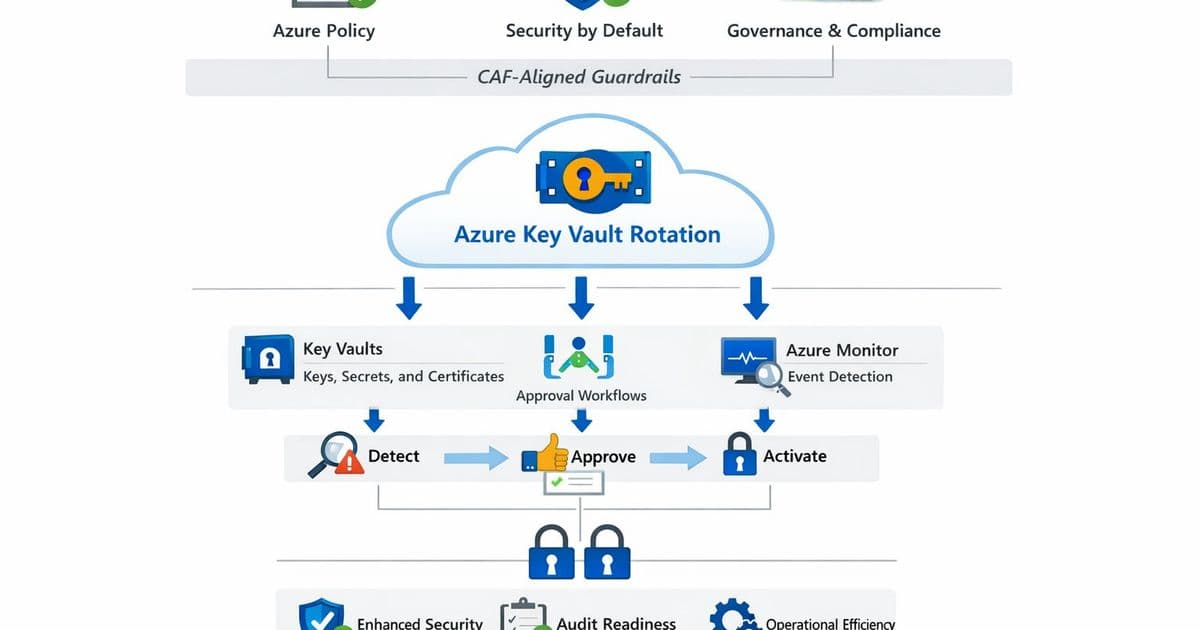
The evolution of Azure Key Vault's auto-rotation capabilities represents a significant advancement in cloud security operations. Unlike basic manual rotation processes that rely on human memory and ad-hoc procedures, Azure's implementation offers a structured approach aligned with the Cloud Adoption Framework (CAF). This shift transforms credential management from a reactive operational burden to a proactive security capability.
The Challenge of Manual Credential Rotation
At enterprise scale, manual credential rotation becomes unsustainable. Organizations face multiple pain points:
- Unexpected outages when certificates expire at midnight
- Untracked secrets increasing breach risk
- Inconsistent rotation practices across different teams
- Difficulty proving compliance during audits
- Operational overhead consuming valuable engineering resources
These challenges aren't merely technical—they represent significant business risks. A single expired certificate can bring down critical applications, resulting in revenue loss, customer dissatisfaction, and reputational damage. According to industry reports, credential-related incidents account for a substantial portion of security breaches, making automated rotation not just a convenience but a necessity.
Azure's Approach to Auto-Rotation
Azure Key Vault's auto-rotation functionality provides a comprehensive solution that addresses these challenges through several key components:
First, Azure Policy serves as the governance backbone, ensuring rotation controls, diagnostics, and networking configurations are consistently applied across the organization. This policy-as-code approach eliminates configuration drift and provides auditable evidence of compliance.
Second, Azure Monitor provides visibility into credential lifecycles, alerting teams well before expiration dates. This proactive visibility transforms what was once a reactive scramble into a planned, managed process.
Third, Logic Apps orchestrate approval workflows when human intervention is required, particularly for sensitive systems like identity federation certificates. This hybrid approach balances automation with necessary governance controls.
The architecture follows a clear separation of concerns:
- Platform teams manage Key Vault instances and rotation policies
- Identity teams oversee certificate authorities and federation approvals
- Application teams consume credentials through managed identities and Key Vault references
This separation enables scalability while maintaining appropriate governance boundaries.
Comparing Cloud Provider Approaches
When evaluating credential rotation capabilities across major cloud providers, several key differences emerge:
Azure Key Vault offers the most integrated approach, combining policy enforcement, monitoring, and orchestration within a unified ecosystem. The tight integration with Azure Policy provides governance at scale, while the Logic Apps integration enables complex approval workflows.
AWS Secrets Manager provides rotation capabilities but requires more manual configuration of Lambda functions for custom rotation scenarios. While AWS offers integration with CloudWatch for monitoring, the policy enforcement lacks the same level of native integration as Azure's approach.
Google Cloud Secret Manager offers rotation functionality but with fewer built-in orchestration capabilities. Google's approach relies more on external tooling for complex approval workflows, potentially increasing operational complexity.
Azure's advantage lies in its comprehensive, integrated approach that reduces the operational overhead typically associated with implementing and maintaining credential rotation at scale.
Implementation Scenarios and Business Impact
Organizations can apply Azure Key Vault auto-rotation across multiple scenarios, each with distinct business impacts:
Internal Application Workloads
For internal applications, automated rotation without approval gates provides maximum operational efficiency. Applications consume credentials through managed identities, eliminating the need to store secrets in configuration files. The business impact includes:
- Reduced operational overhead by automating routine credential management
- Elimination of emergency outages due to expired credentials
- Improved security posture through regular credential refresh
- Simplified compliance with regulatory requirements
SaaS/SSO Federation Certificates
For identity federation certificates connecting to SaaS platforms like Salesforce or ServiceNow, a hybrid approach with required approvals balances security and operational needs. The business impact includes:
- Prevention of catastrophic federation outages
- Maintained trust with external SaaS providers
- Audit trail for certificate changes supporting compliance
- Streamlined renewal process reducing security team workload
Platform Infrastructure
For critical platform components like Domain Controllers or internal Certificate Authorities, tightly controlled rotation with manual deployment ensures stability. The business impact includes:
- Maintained system stability during sensitive credential changes
- Alignment with change management processes
- Reduced risk of misconfiguration during rotation
- Preservation of system integrity and availability
Strategic Considerations for Implementation
Successful implementation of Azure Key Vault auto-rotation requires strategic planning across several dimensions:
Governance Framework
Establishing a governance framework that defines rotation policies, approval requirements, and compliance expectations is essential. This framework should:
- Define rotation intervals based on sensitivity and risk
- Establish approval workflows for different credential types
- Document retention policies for expired credentials
- Define escalation procedures for automation failures
Integration Strategy
A well-planned integration strategy ensures seamless adoption across the organization:
- Inventory existing credential usage and dependencies
- Prioritize workloads for migration to auto-rotation
- Develop migration plans for applications using hardcoded credentials
- Establish communication plans for stakeholders affected by changes
Operational Readiness
Preparing operations teams for the new paradigm is critical:
- Develop runbooks for automation failure scenarios
- Train teams on monitoring and alerting procedures
- Conduct tabletop exercises for emergency response
- Establish metrics for measuring rotation success and reliability
Measuring Success
Key performance indicators for Azure Key Vault auto-rotation implementation include:
- Reduction in credential-related incidents
- Decrease in manual credential management tasks
- Improvement in compliance audit scores
- Increase in automated rotation success rate
- Reduction in mean time to recover from credential issues
Conclusion
Azure Key Vault auto-rotation represents a significant advancement in cloud security operations, transforming credential management from a reactive burden to a proactive security capability. By implementing policy-driven automation with appropriate governance controls, organizations can achieve security, reliability, and compliance by default.
The strategic implementation of auto-rotation requires careful planning across governance, integration, and operational dimensions. However, the business benefits—including reduced risk, improved compliance, and operational efficiency—make it an essential capability for organizations operating at scale in cloud environments.
As cloud adoption continues to accelerate, automated credential management will transition from a competitive advantage to a baseline expectation. Organizations that proactively implement robust auto-rotation strategies will be better positioned to secure their digital assets while maintaining operational agility.
References:
Comments
Please log in or register to join the discussion