A sophisticated threat actor is using Microsoft Teams as a delivery mechanism for a custom malware suite called 'Snow,' enabling deep network compromise and data theft. Security researchers from Google's Mandiant have detailed the attack chain and provided detection tools to help organizations defend against this emerging threat.
In a concerning development highlighting the evolving tactics of cybercriminals, a threat group tracked as UNC6692 has been observed using Microsoft Teams as a delivery mechanism for a new, custom malware suite named 'Snow.' The campaign demonstrates a sophisticated approach to social engineering combined with advanced malware techniques, enabling attackers to achieve deep network compromise and steal sensitive data.
According to researchers at Google's Mandiant, the attackers begin their campaign with 'email bombing' tactics designed to create urgency among potential victims. Following the initial email bombardment, threat actors contact targets directly through Microsoft Teams, impersonating IT helpdesk agents to establish credibility and trust. This approach has been increasingly popular in the cybercrime space, as highlighted in a recent Microsoft report, which noted the growing trend of Teams abuse in helpdesk impersonation attacks.
During the Teams interaction, victims are prompted to click a link supposedly offering a patch to block email spam. In reality, this link leads to a dropper that executes AutoHotkey scripts, ultimately loading 'SnowBelt,' a malicious Chrome extension. The extension operates within a headless Microsoft Edge instance, making it invisible to the victim while establishing persistence through scheduled tasks and startup folder shortcuts.
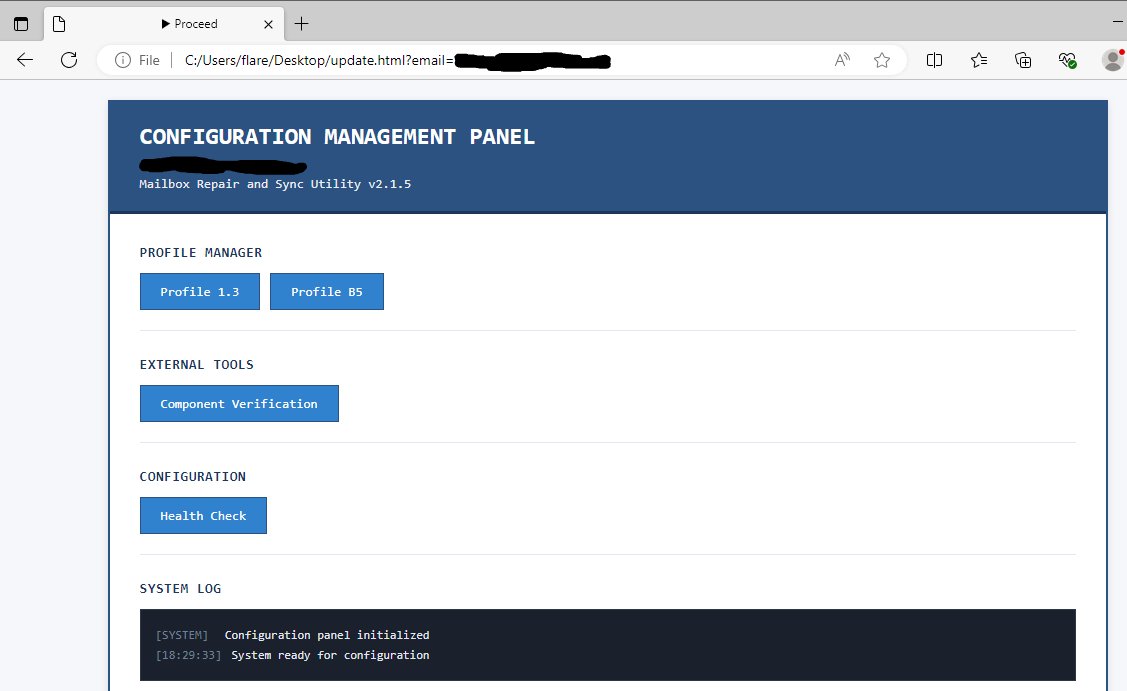 Malicious page used in the attacks
Source: Google
Malicious page used in the attacks
Source: Google
The 'Snow' malware suite consists of three interconnected components that work together to maintain access and facilitate data theft. SnowBelt serves as both a persistence mechanism and a relay for commands sent by the attacker to a Python-based backdoor named SnowBasin. Communication between the operator and the infected system is masked through a WebSocket tunnel established by a tunneler tool called SnowGlaze, which also facilitates SOCKS proxy operations to route arbitrary TCP traffic through the compromised host.
SnowBasin, the backdoor component, runs a local HTTP server capable of executing attacker-supplied CMD or PowerShell commands directly on the infected system. The backdoor relays command execution results back to the operator through the same communication pipeline established by SnowGlaze. This component provides the attacker with comprehensive remote access capabilities, including remote shell access, data exfiltration, file downloads, screenshot capturing, and basic file management operations. Notably, the operator can also issue a self-termination command to shut down the backdoor if needed.
The attack lifecycle, as detailed by Mandiant researchers, reveals a methodical approach to network penetration and data theft. Following initial compromise, the attackers perform internal reconnaissance, scanning for services such as SMB and RDP to identify additional targets. They then move laterally across the network using techniques like LSASS memory dumping to extract credential material and pass-the-hash authentication to access additional hosts.
 Featured image
Featured image
The culmination of the attack involves targeting domain controllers, where the threat actor deploys FTK Imager to extract the Active Directory database, along with critical registry hives including SYSTEM, SAM, and SECURITY. These sensitive files containing credential data across the entire domain are then exfiltrated from the network using LimeWire, giving the attackers comprehensive access to organizational credentials.
Mandiant's report provides extensive indicators of compromise (IoCs) and YARA rules to help security professionals detect the 'Snow' toolset within their environments. For organizations seeking to defend against this threat, several key mitigation strategies emerge:
User awareness training: Educate employees about sophisticated social engineering attacks, particularly those involving impersonation of IT staff through collaboration platforms like Microsoft Teams.
Endpoint protection: Implement advanced endpoint detection and response (EDR) solutions capable of identifying suspicious process chains, particularly those involving AutoHotkey scripts and unusual browser extension behavior.
Network segmentation: Limit lateral movement potential by implementing proper network segmentation, especially separating critical systems like domain controllers from general user networks.
Multi-factor authentication: Enforce MFA across all services, particularly for privileged accounts, to mitigate the impact of credential theft techniques like pass-the-hash.
Regular security assessments: Conduct regular security assessments to identify potential vulnerabilities in remote access tools and collaboration platforms that might be exploited in similar campaigns.
The emergence of the 'Snow' malware campaign underscores the increasing sophistication of threat actors and their ability to adapt to security controls. By combining social engineering with multi-component malware architectures, attackers are achieving deeper network penetration and more comprehensive data theft than ever before.
Organizations should treat this campaign as a warning sign and evaluate their defenses against similar attack vectors. The detailed IoCs and YARA rules provided by Mandiant offer a starting point for detection, but proactive security measures and user education remain the most effective defenses against these evolving threats.
For security professionals seeking to understand similar advanced threats, resources like Mandiant's research blog and Microsoft's Security Intelligence reports provide valuable insights into emerging attack patterns and mitigation strategies.

Comments
Please log in or register to join the discussion