Automotive platform CarGurus suffers massive data breach as ShinyHunters group leaks 12.4 million user records including personal and financial information.
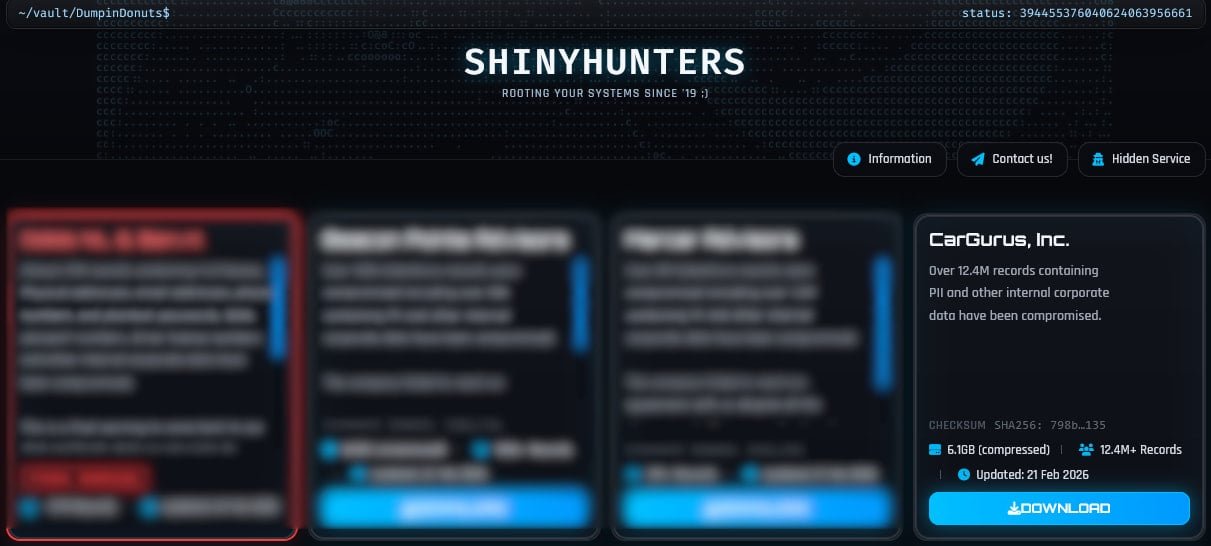
The automotive research and shopping platform CarGurus has suffered a significant data breach, with the ShinyHunters extortion group claiming responsibility for stealing and publishing personal information from over 12.4 million user accounts.

Massive Data Exposure
The breach, first reported on February 21, 2026, involves a 6.1GB archive containing detailed personal information from millions of CarGurus users. The compromised data includes email addresses, IP addresses, full names, phone numbers, physical addresses, user account IDs, finance pre-qualification application data, finance application outcomes, dealer account details, and subscription information.
While CarGurus has not officially confirmed the breach or responded to media inquiries, the HaveIBeenPwned (HIBP) platform has added the dataset to its database after attempting to verify its authenticity. According to HIBP, approximately 70% of the leaked data was already present in their database from previous incidents, meaning roughly 3.7 million records are newly exposed.
Immediate Security Concerns
The freely available nature of this data poses significant risks to affected users. Cybercriminals can leverage the comprehensive personal information for sophisticated phishing attacks, identity theft, and other fraudulent activities. The inclusion of finance-related data is particularly concerning, as it could enable attackers to craft highly convincing scams targeting users' financial information.
CarGurus users are strongly advised to remain vigilant for suspicious communications and to be cautious of any unexpected messages claiming to be from the company or related financial institutions.
ShinyHunters' Expanding Operations
This breach represents the latest in a series of high-profile attacks by the ShinyHunters group, which has been remarkably active in recent months. The threat actor has claimed responsibility for attacks on numerous major companies, including:
- Dutch telecommunications provider Odido
- Ad tech firm Optimizely
- Fintech company Figure (affecting nearly 1 million accounts)
- Outerwear brand Canada Goose (600K customer records leaked)
- Restaurant chain Panera Bread (5.1 million accounts impacted)
- Online dating company Match Group (exposing data from Hinge, Tinder, OkCupid, and Match)
- Music streaming platform SoundCloud (29.8 million accounts affected)
Attack Methodology
ShinyHunters has developed a sophisticated approach to breaching organizations, primarily relying on social engineering tactics. Their most common technique involves voice phishing (vishing), where they direct victims to credential-harvesting pages that grant access to critical SaaS platforms such as Salesforce, Okta, and Microsoft 365.
In previous campaigns, the group has successfully tricked employees into installing malicious OAuth applications, which provided API-level read access to customer data tables within Salesforce instances. This method allows them to bypass traditional security measures and extract large volumes of sensitive data without triggering immediate alarms.
Industry Context
The CarGurus breach highlights the ongoing challenges faced by digital platforms in protecting user data. With an estimated 40 million monthly visitors across the U.S., Canada, and the U.K., CarGurus represents a significant target for cybercriminals due to the wealth of personal and financial information it processes.
This incident follows a pattern of recent high-profile breaches affecting major companies across various sectors. The frequency and scale of these attacks underscore the importance of robust security measures, employee training to recognize social engineering attempts, and comprehensive data protection strategies.
Protection Recommendations
For affected CarGurus users and those concerned about similar breaches:
- Monitor financial accounts closely for suspicious activity
- Be extremely cautious of unsolicited communications requesting personal information
- Enable two-factor authentication on all accounts where available
- Consider using identity theft protection services
- Regularly update passwords and use unique credentials for different services
- Report any suspicious activity to both the affected company and relevant authorities
The CarGurus breach serves as a stark reminder that even established, publicly traded companies remain vulnerable to sophisticated cyber attacks, and users must remain proactive in protecting their personal information.

Comments
Please log in or register to join the discussion