Ukraine's CERT-UA warns of phishing campaign impersonating the agency to distribute AGEWHEEZE remote access trojan, with attackers claiming 200K+ devices compromised despite official reports of limited success.
The Computer Emergency Response Team of Ukraine (CERT-UA) has issued a stark warning about a sophisticated phishing campaign that impersonated the agency itself to distribute a dangerous remote access trojan called AGEWHEEZE. The attack, which occurred on March 26 and 27, 2026, targeted a wide range of Ukrainian organizations including state institutions, medical centers, security companies, educational institutions, financial organizations, and software development firms.
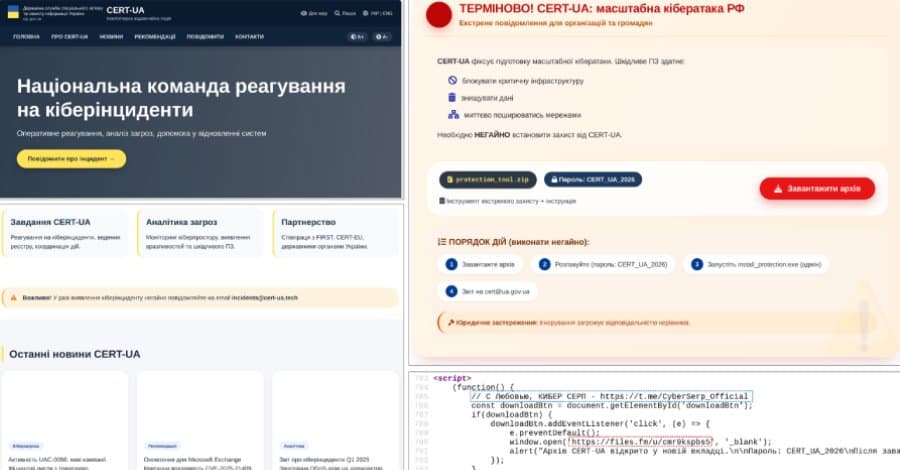
The Impersonation Strategy
The threat actors behind this campaign, identified as UAC-0255 and operating under the banner "Cyber Serp," employed a particularly brazen tactic: they posed as CERT-UA itself. The attackers sent emails from addresses like "incidents@cert-ua[.]tech" and distributed password-protected ZIP archives hosted on Files.fm, claiming recipients needed to install "specialized software" for protection.
The ZIP file, named "CERT_UA_protection_tool.zip," was designed to appear as legitimate security software from the agency. However, once opened, it downloaded and installed the AGEWHEEZE malware, a sophisticated remote access trojan written in Go.
AGEWHEEZE Malware Capabilities
CERT-UA's analysis reveals that AGEWHEEZE is a highly capable piece of malware that communicates with command-and-control servers over WebSockets at IP address 54.36.237[.]92. The trojan supports an extensive range of malicious commands:
- Remote command execution
- File operations (upload, download, delete)
- Clipboard modification
- Mouse and keyboard emulation
- Screenshot capture
- Process and service management
- System information gathering
The malware establishes persistence through multiple mechanisms, including scheduled tasks, Windows Registry modifications, and adding itself to the Startup directory, making it particularly difficult to remove once installed.
Scale and Claims vs. Reality
Perhaps most alarming are the conflicting reports about the campaign's scale. While CERT-UA stated the attack was "largely unsuccessful" with "no more than a few infected personal devices belonging to employees of educational institutions," the attackers themselves made extraordinary claims on their Telegram channel.
Cyber Serp claimed they sent phishing emails to 1 million ukr[.]net mailboxes and compromised over 200,000 devices. The group, which describes itself as "cyber-underground operatives from Ukraine," created their Telegram channel in November 2025 and has amassed over 700 subscribers.
In a statement that attempts to justify their actions, Cyber Serp claimed: "We are not bandits – the average Ukrainian citizen will never suffer as a result of our actions." This rhetoric attempts to position the group as some kind of vigilante operation rather than criminal hackers.
AI-Generated Infrastructure
CERT-UA's investigation uncovered evidence that artificial intelligence tools were used to generate the fake website cert-ua[.]tech. The HTML source code contained a comment reading "С Любовью, КИБЕР СЕРП" ("With Love, CYBER SERP"), suggesting the attackers leveraged AI to create convincing fake infrastructure quickly and efficiently.
This use of AI for malicious purposes represents a growing trend in cybercrime, where threat actors use automation and AI tools to scale their operations and create more convincing phishing materials.
Previous Cyber Serp Activities
This campaign isn't Cyber Serp's first high-profile operation. Last month, the group claimed responsibility for breaching Ukrainian cybersecurity company Cipher, stating they obtained a complete dump of the company's servers, including client databases and source code for CIPS products.
Cipher acknowledged the breach in a statement, confirming that attackers compromised an employee's credentials at one of their technology partners. However, the company maintained that its infrastructure was operating normally and that the infected user had access to only a single project without sensitive data.
Security Implications and Recommendations
This incident highlights several critical security concerns:
1. Trust in Official Communications: The impersonation of a trusted cybersecurity agency demonstrates how threat actors exploit institutional trust. Organizations must verify any security-related communications through official channels.
2. AI-Powered Attacks: The use of AI tools to generate fake websites and phishing content suggests attackers are increasingly leveraging automation to scale their operations and improve success rates.
3. Supply Chain Risks: The attack targeting software development companies and technology firms could potentially lead to supply chain compromises if successful.
4. Verification Protocols: Organizations should implement strict verification procedures for any software or security tools, especially those claiming to come from official sources.
5. Employee Training: Despite the sophisticated nature of the attack, employee awareness and training remain crucial defenses against phishing attempts.
The Broader Context
This campaign occurs against the backdrop of ongoing cyber conflict in Ukraine, where state-sponsored and independent threat actors frequently target critical infrastructure and government organizations. The use of AI tools and the brazen impersonation of a national CERT demonstrates the evolving sophistication of these attacks.
The discrepancy between CERT-UA's assessment of limited success and Cyber Serp's claims of massive compromise underscores the challenges in accurately measuring the impact of phishing campaigns, particularly when attackers may exaggerate their achievements for propaganda purposes.
For organizations in Ukraine and beyond, this incident serves as a reminder that even the most trusted institutions can be impersonated, and that verification of all security communications is essential. The AGEWHEEZE malware's capabilities also highlight the ongoing threat of remote access trojans in targeted attacks against organizations of all types.
As cyber threats continue to evolve with the integration of AI and other advanced technologies, maintaining robust security practices and healthy skepticism toward unsolicited security communications becomes increasingly critical.
Comments
Please log in or register to join the discussion