U.S. federal agencies have until April 11 to patch a critical Ivanti EPMM vulnerability actively exploited since January, with nearly 950 vulnerable systems still exposed online globally.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an emergency directive requiring federal agencies to patch a critical vulnerability in Ivanti Endpoint Manager Mobile (EPMM) by Saturday midnight, April 11, 2026. The vulnerability, tracked as CVE-2026-1340, has been actively exploited in attacks since January 2026 and enables unauthenticated remote code execution on Internet-exposed systems.

Critical Vulnerability Exploited in the Wild
The code injection flaw allows threat actors without privileges to gain remote code execution on unpatched EPMM appliances. Ivanti disclosed the vulnerability alongside a second security bug (CVE-2026-1281) on January 29, 2026, when it released security updates to address both issues.
"Successful exploitation could lead to unauthenticated remote code execution. We are aware of a very limited number of customers whose solution has been exploited at the time of disclosure," Ivanti stated when announcing the patches.
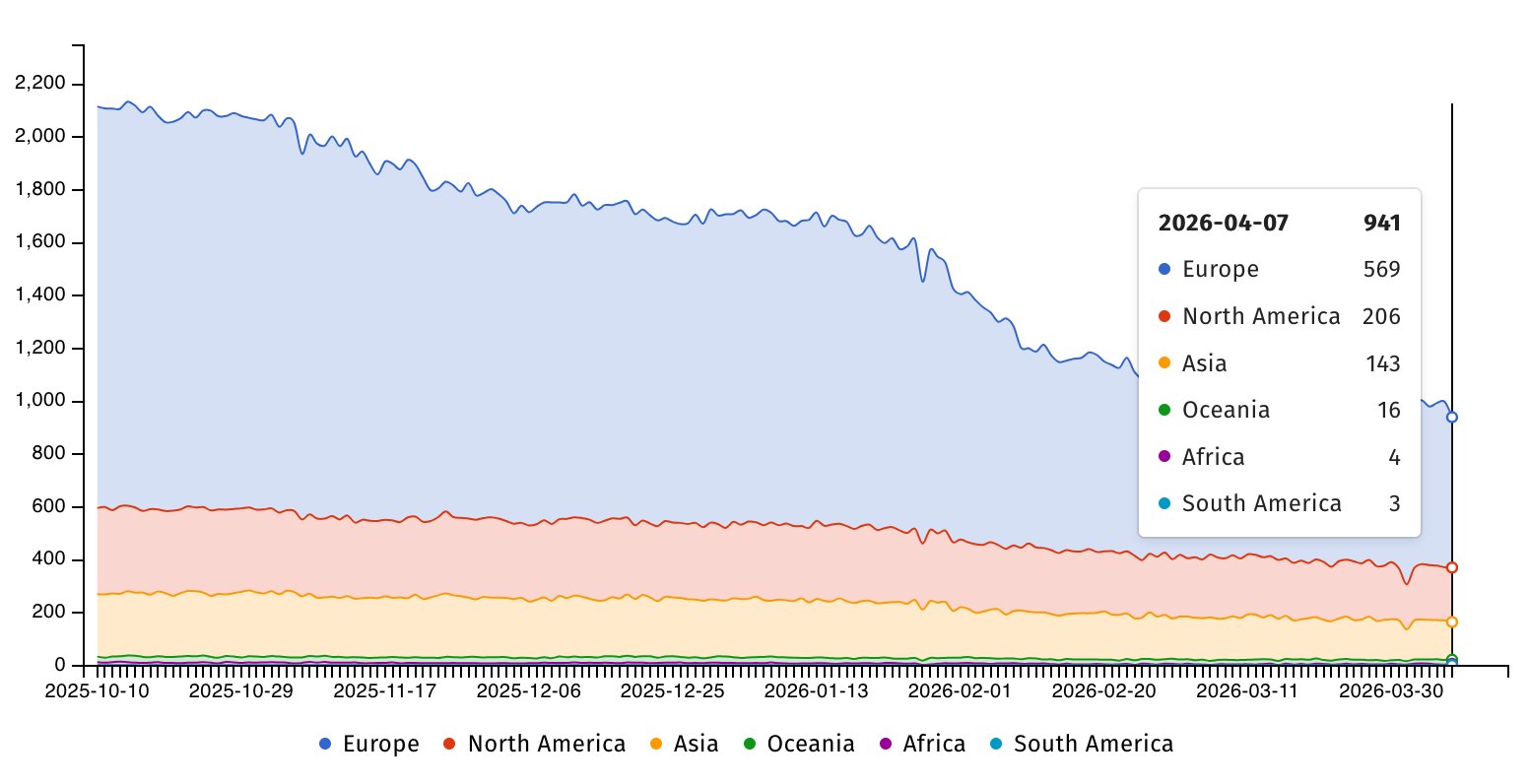
Internet security watchdog Shadowserver is currently tracking nearly 950 IP addresses with Ivanti EPMM fingerprints still exposed online. The majority of these vulnerable systems are located in Europe (569) and North America (206), though the exact number of patched systems remains unknown.
Federal Mandate and Timeline
On April 6, 2026, CISA added CVE-2026-1340 to its Known Exploited Vulnerabilities (KEV) Catalog and issued the emergency directive under Binding Operational Directive (BOD) 22-01. Federal Civilian Executive Branch (FCEB) agencies must complete patching by Saturday midnight, April 11, 2026.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," CISA warned in its directive. The agency advised agencies to apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Broader Security Implications
While BOD 22-01 applies only to U.S. federal agencies, CISA strongly recommends that all organizations, including those in the private sector, prioritize applying patches for CVE-2026-1340 as soon as possible. The agency emphasized that this vulnerability represents a significant risk to organizations across all sectors.
The Ivanti EPMM vulnerability is part of a concerning pattern of exploitation targeting Ivanti products. Multiple Ivanti vulnerabilities have been exploited in recent years through zero-day attacks to breach a wide range of targets, including government agencies worldwide. In total, CISA has identified 33 Ivanti vulnerabilities as exploited in attacks, with 12 of these being used by various ransomware operations.
Ivanti provides IT asset management products to over 40,000 customers through a network of more than 7,000 partners globally, making the widespread impact of these vulnerabilities particularly concerning.
Historical Context and Related Incidents
This incident follows a pattern of critical vulnerabilities in enterprise management software being exploited in the wild. Previous incidents include:
- Chinese hackers exploiting Ivanti EPMM flaws to breach government agencies
- Actively exploited Citrix flaws requiring federal patching mandates
- Critical F5 BIG-IP vulnerabilities being targeted in ongoing attacks
- DarkSword iOS flaws exploited in attacks against federal systems
Mitigation and Response
Organizations using Ivanti EPMM should immediately:
- Verify if their systems are exposed to the internet
- Apply the January 29, 2026 security patches immediately
- Monitor for suspicious activity on their EPMM appliances
- Consider implementing network segmentation for exposed systems
- Review access logs for indicators of compromise
The four-day window provided by CISA underscores the severity of the threat and the agency's concern about potential widespread exploitation. Organizations that fail to comply with the directive may face compliance issues and increased vulnerability to cyber attacks.
Expert Analysis
Security experts note that vulnerabilities in enterprise management systems like EPMM are particularly dangerous because they often have elevated privileges and access to sensitive organizational data. The fact that this vulnerability has been exploited since January without widespread awareness highlights the challenges organizations face in maintaining visibility into their attack surface.
"When vulnerabilities in management platforms are exploited, the potential for lateral movement and privilege escalation increases dramatically," said one security analyst familiar with the situation. "The four-day deadline reflects the urgency of containing this threat before it can be used in more widespread attacks."
The incident also raises questions about the security practices of enterprise software vendors and the need for more robust security testing and disclosure processes to prevent vulnerabilities from being exploited in the wild before patches are available.
Organizations should treat this as a wake-up call to review their vulnerability management processes and ensure they have the capability to rapidly deploy critical security updates across their infrastructure.

Comments
Please log in or register to join the discussion