Sophos researchers uncover three ClickFix campaigns delivering MacSync infostealer through fake AI tool installers, exploiting developer trust in legitimate installation patterns.
Sophos researchers have uncovered three distinct ClickFix campaigns that are actively distributing a macOS information stealer called MacSync through deceptive AI tool installer lures.
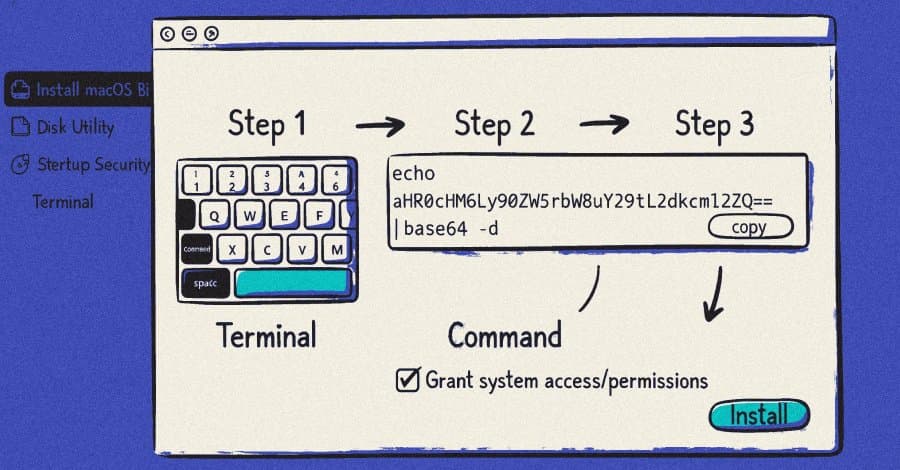
The campaigns exploit a social engineering technique that tricks users into copying and executing malicious commands in their Terminal application, bypassing traditional exploit-based attack methods.
Three Active ClickFix Campaigns
The first campaign, active in November 2025, used OpenAI Atlas browser as bait delivered through sponsored Google search results. Victims were directed to fake Google Sites URLs containing download buttons that prompted users to open Terminal and paste commands.
A second campaign in December 2025 leveraged sponsored links tied to searches like "how to clean up your Mac" on Google. These links redirected victims to legitimate OpenAI ChatGPT conversations, creating an illusion of safety before leading to malicious GitHub-themed landing pages.
The most recent campaign, active since February 2026, targets users in Belgium, India, and parts of North and South America. This iteration features a new MacSync variant with dynamic AppleScript payloads and in-memory execution capabilities designed to evade static analysis and behavioral detections.
Technical Analysis of MacSync
The MacSync infostealer is equipped to harvest extensive data from compromised systems, including credentials, files, keychain databases, and cryptocurrency wallet seed phrases. After execution, the malware contacts a hard-coded server to retrieve the AppleScript payload while simultaneously attempting to remove evidence of data theft.
Sophos researchers note that the latest variant "likely represents the malware developer adjusting to OS and software security measures to maintain effectiveness."
InstallFix: A New Evolution
Security researchers have identified a related technique called InstallFix or GoogleFix, which weaponizes the trust associated with ChatGPT conversations. Unlike traditional ClickFix attacks that require fake CAPTCHAs or error messages, InstallFix simply presents users with what appears to be legitimate software installation instructions.
According to Pillar Security researcher Eilon Cohen, there have been at least 20 distinct malware campaigns targeting AI and vibe coding tools between February and March 2026. These campaigns specifically target macOS users because they "skew heavily toward macOS, and macOS users tend to have higher-value credentials (SSH keys, cloud tokens, cryptocurrency wallets)."
Developer-Targeted Attack Pattern
The effectiveness of these campaigns stems from exploiting legitimate installation patterns familiar to developers. Tools like Homebrew, Rust, nvm, and many others use the exact "curl | sh" pattern that malicious commands hide within.
Nati Tal, head of Guardio Labs, reports that similar infection chains deploy Alien infostealer on Windows and Atomic Stealer on macOS. The PowerShell commands executed after pasting supposed installation commands for tools like Claude Code fetch legitimate Chrome extension packages within malicious HTML Application (HTA) files.
Broader Threat Landscape
Multiple threat actors have adopted ClickFix tactics. The KongTuke traffic distribution system (TDS) uses compromised WordPress websites and fake CAPTCHA lures to deliver ModeloRAT, a Python-based trojan. This group specifically checks for corporate domain membership and installed security tools before continuing, indicating a focus on enterprise environments.
Other observed ClickFix-style attacks include:
- Using compromised websites mimicking Google's "Aw Snap!" error to distribute droppers
- Malvertising links leading to Remcos RAT deployment
- Fake CAPTCHA verification on phony websites promoting scams
- Bogus CleanMyMac sites deploying SHub Stealer
- Malicious Cloudflare verification challenges injecting stealer malware
WordPress Compromise Campaign
Rapid7 recently revealed a widespread campaign compromising highly trusted WordPress websites since December 2025. More than 250 infected websites across 12 countries inject ClickFix implants impersonating Cloudflare human verification challenges.
The compromised sites, primarily regional news outlets and local businesses, ultimately deliver various stealer malware families including StealC, an improved Vidar Stealer, Impure Stealer, and VodkaStealer.
Protection Recommendations
Site administrators are advised to:
- Keep WordPress sites updated with latest security patches
- Use strong passwords for administrative access
- Implement two-factor authentication (2FA)
- Scan for suspicious administrator accounts
For individual users, experts recommend maintaining a zero-trust mindset, using reputable security software, and staying informed about the latest phishing and ClickFix tactics used by malicious actors.
The sophistication of these campaigns demonstrates how threat actors continue to evolve their techniques, weaponizing legitimate platforms and trusted software installation patterns to compromise systems and steal sensitive data.
Comments
Please log in or register to join the discussion