Cloudflare introduces a reference architecture for scaling Model Context Protocol deployments, focusing on centralized governance and remote infrastructure to address security risks and cost concerns in enterprise AI agent systems.
Cloudflare's MCP Architecture Addresses Enterprise Security and Governance Challenges
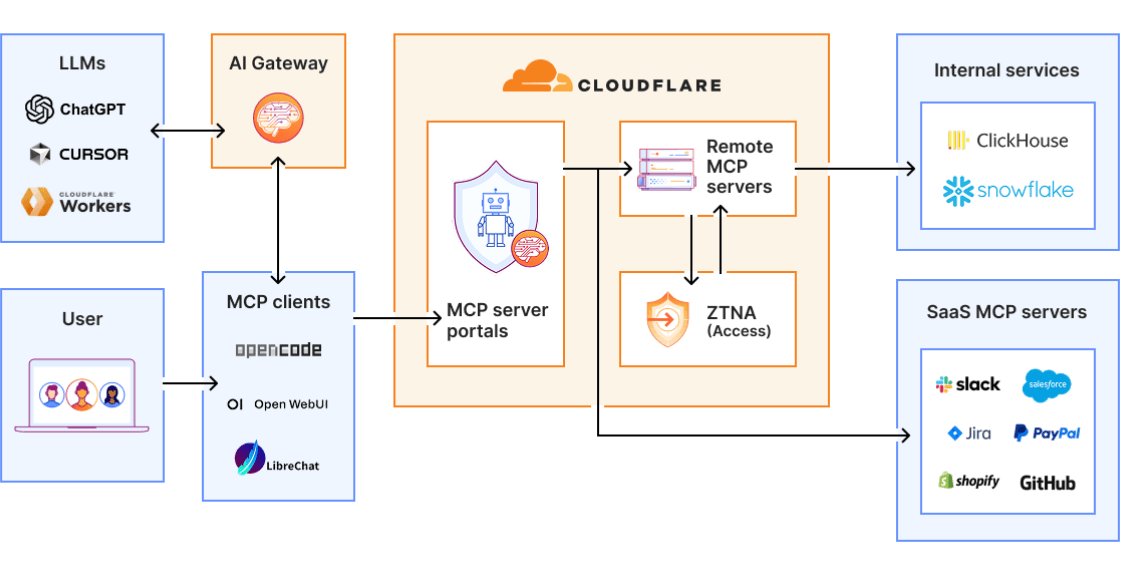
Cloudflare has unveiled a comprehensive reference architecture for scaling Model Context Protocol (MCP) deployments across enterprise environments, emphasizing centralized governance, remote server infrastructure, and cost controls as essential components of production-ready agent systems. This announcement arrives amid increasing scrutiny of MCP-based implementations, as research continues to highlight significant security vulnerabilities that organizations must address before widespread adoption.
The Model Context Protocol, an open standard designed to connect AI agents with external tools and data sources, creates a separation between agent-facing clients and backend servers interfacing with corporate resources. While this abstraction enables autonomous data retrieval and action execution, it introduces new trust boundaries between AI models, tools, and sensitive systems that require careful management.
Growing Security Concerns with MCP Implementations
Recent research has identified several critical risks in MCP-based systems, including prompt injection attacks, supply chain vulnerabilities, and exposed or misconfigured servers. Studies have demonstrated that successful implementations can lead to arbitrary code execution and data exfiltration across MCP integrations. The protocol's architecture inherently expands attack surfaces compared to traditional LLM usage, as a single prompt can trigger chains of actions across multiple systems.
Academic analysis suggests these risks extend beyond implementation flaws, with protocol-level design choices potentially amplifying attack success rates in agent-tool systems. This creates a significant challenge for organizations attempting to balance AI capability with security requirements.
"Locally deployed MCP servers represent a substantial security liability," explains Cloudflare's approach document. "These deployments often rely on unvetted software and lack centralized oversight, creating vulnerabilities that can be exploited by malicious actors."
Cloudflare's Architectural Approach
Cloudflare's reference architecture addresses these challenges through a multi-layered security and governance model:
Remote Server Infrastructure
Instead of encouraging local MCP server deployments, Cloudflare has adopted a model where MCP servers are deployed remotely on its developer platform and managed by a centralized team. This approach eliminates the security risks associated with unpatched or misconfigured local installations while maintaining the flexibility needed for diverse enterprise environments.

Centralized Authentication and Access Control
Authentication is handled through Cloudflare Access, which integrates with existing enterprise systems including single sign-on (SSO), multi-factor authentication (MFA), and contextual signals such as device posture and location. This creates multiple layers of verification that can adapt to risk-based access policies.
The MCP server portals provide a unified interface for discovering and accessing authorized servers while enabling administrators to enforce policies such as data loss prevention (DLP) rules and fine-grained tool exposure. This centralized control model ensures consistent security enforcement across all MCP interactions.
Cost Control and Optimization
On the cost management front, the architecture incorporates an 'AI Gateway' positioned between MCP clients and underlying language models. This gateway allows organizations to route requests across different model providers while enforcing usage limits and monitoring token consumption at a per-user level. This granular control becomes increasingly important as organizations scale AI agent deployments.
Cloudflare has also introduced "Code Mode," designed to address the growing complexity of MCP tool definitions. Rather than exposing every API operation to the model, Code Mode collapses tool interfaces into a small set of dynamic entry points, allowing models to discover and invoke tools on demand. According to Cloudflare, this approach can reduce token usage by up to 99.9%, effectively mitigating context window limitations while improving performance.
Architectural Implications for Enterprise AI Strategy
While these technical controls address immediate security and cost concerns, industry analysts note that the underlying challenge may be less about individual features and more about how MCP fits into broader agent system architectures.
Forrester Research clarifies that protocols such as MCP are often mistakenly viewed as governance layers, when in practice they function more like transport or interoperability mechanisms—comparable to RPC or messaging systems rather than policy engines. This distinction becomes significant as enterprises begin designing centralized control layers.
"Recent research suggests that governance, observability, and policy enforcement are emerging as a separate 'control plane' concern in agent architectures, sitting above both tool integration and orchestration layers," explains Sarah Johnson, cloud infrastructure analyst at Tech Insights. "In this context, approaches such as Cloudflare's can be seen as part of a wider movement toward externalizing control, rather than something inherent to MCP itself."
Comparative Analysis with Alternative Approaches
Cloudflare's approach differs significantly from other MCP implementation strategies emerging in the market:
Local Deployment Models: Many early MCP adopters have implemented servers locally within their infrastructure, providing maximum control but introducing security and maintenance burdens. Cloudflare's remote model shifts these responsibilities to a specialized provider.
Cloud-Native Implementations: Providers like AWS and Microsoft are developing MCP integrations within their cloud ecosystems, creating vendor lock-in risks. Cloudflare's approach emphasizes portability while still leveraging cloud infrastructure benefits.
Open Source Governance Projects: Community initiatives focus on creating governance frameworks for MCP but often lack the integration depth needed for enterprise environments. Cloudflare's solution provides a cohesive platform combining security, cost controls, and governance.
Business Impact and Recommendations
For organizations evaluating MCP adoption, Cloudflare's architecture offers several business advantages:
Reduced Security Overhead: By centralizing MCP server management and security controls, organizations can reduce the security team's operational burden while maintaining robust protection.
Cost Predictability: The AI Gateway and Code Mode features provide more predictable cost structures, making it easier to budget for AI agent deployments.
Compliance Facilitation: Centralized governance simplifies compliance with regulatory requirements such as GDPR, HIPAA, and industry-specific standards.
Scalability: The reference architecture provides a foundation for scaling MCP deployments across departments and regions without proportional increases in management complexity.
Enterprises considering MCP implementations should evaluate whether a centralized governance model aligns with their existing security frameworks and operational capabilities. Organizations with strict data sovereignty requirements may need to supplement Cloudflare's approach with additional controls, while those with limited security resources may find particular value in the comprehensive security posture.
As AI agent systems continue evolving, the distinction between transport protocols and governance layers will become increasingly important. Cloudflare's reference architecture represents one approach to addressing this complexity, but organizations should anticipate further innovation in MCP governance and control mechanisms in the coming months.
For more information on Cloudflare's MCP architecture, visit their official documentation or explore the reference architecture whitepaper.
About the Author
Matt Foster is a Technical Principal with Thoughtworks, specializing in application modernization and legacy architecture transformation. He has led multidisciplinary teams across businesses of various sizes in Europe and North America, and has collaborated with industry leaders including Martin Fowler on topics such as Domain-Driven Design and Legacy Displacement Patterns.

Comments
Please log in or register to join the discussion