A major security flaw in the UK's Companies House website allowed anyone to access private company dashboards, view directors' personal information, and potentially modify company details or file fraudulent accounts.
A critical security vulnerability in the UK's Companies House website has exposed the personal information of approximately five million company directors and potentially enabled widespread corporate hijacking. The flaw, discovered by John Hewitt of Ghost Mail, allowed anyone with a Companies House account to access the private dashboards of any registered company in the UK simply by navigating back through their browser after attempting to file documents for another company.
The Vulnerability: Two-Click Access to Any Company
The exploit was remarkably simple. Users logged into their own Companies House account, attempted to file documents for another company by entering its registration number, and when prompted for an authentication code, used their browser's back button to return to what appeared to be their own dashboard. Instead, they were presented with the complete dashboard of the target company, including sensitive information not visible through normal public searches.
This included directors' full dates of birth, personal email addresses, and home addresses—information that Companies House typically keeps private and only displays to authorized users. The vulnerability also appeared to allow modifications to company details and potentially filing of fraudulent accounts, though the extent of these capabilities remains under investigation.
Verification and Immediate Response
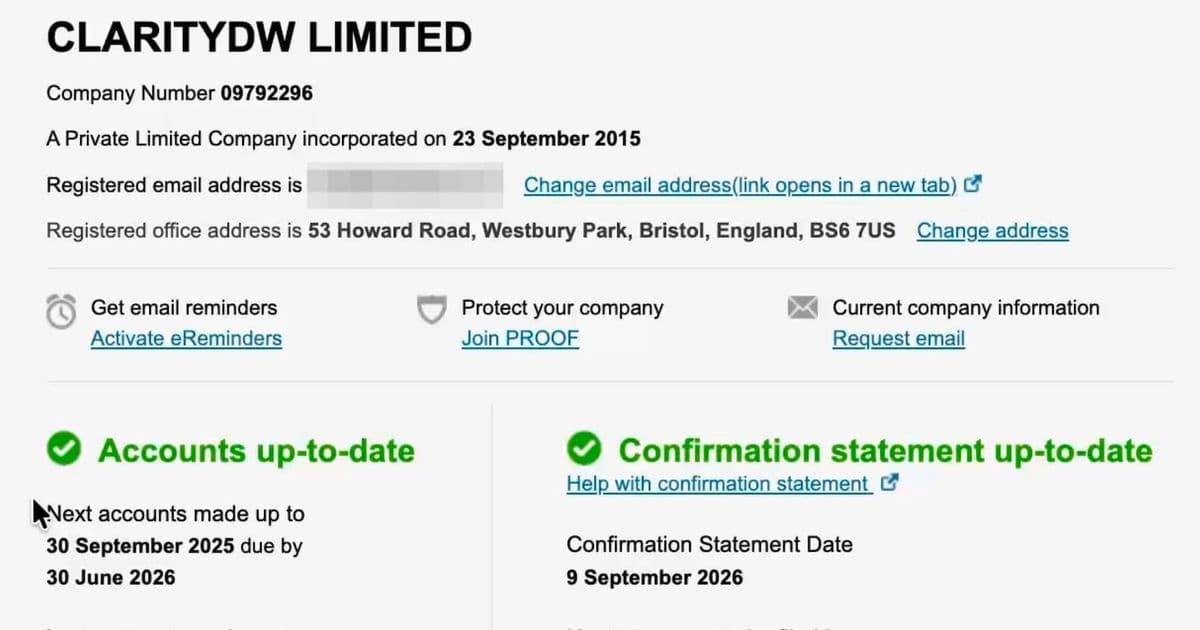
When first informed of the issue, Tax Policy Associates initially suspected a highly technical exploit. However, upon verification, they found the vulnerability worked immediately and consistently. With permission from Jonathan Phillips, owner of ClarityDW Ltd, they demonstrated the flaw in a video showing complete access to a private company dashboard.
Companies House responded promptly after being notified, temporarily shutting down their web filing system. The service availability page now displays a message stating that the WebFiling service is unavailable due to a technical issue, with guidance for customers who may have missed filing deadlines.
Scale and Security Implications
With five million companies registered in the UK, the potential impact is enormous. Research suggests that security vulnerabilities are typically exploited within an average of 15 days of discovery, raising questions about how long this flaw may have been active before detection. The simplicity of the exploit means it could have been widely used without leaving obvious traces.
The GDPR implications are significant, as the exposure of personal data for millions of directors constitutes a major data breach. More concerning is the uncertainty about which specific companies were affected and whether any fraudulent modifications or filings occurred during the vulnerability window.
Context of Ongoing Companies House Security Issues
This incident is particularly troubling given the UK's recent efforts to improve corporate transparency and combat fraud. Companies House has faced criticism for inadequate verification processes that have allowed fake banks and fraudulent companies to be registered with minimal scrutiny. The ease with which this vulnerability was discovered and exploited suggests systemic security weaknesses in what should be a critical piece of national infrastructure.
The vulnerability comes at a time when corporate fraud is increasingly sophisticated, with criminals using fake directors, shell companies, and identity theft to commit financial crimes. Access to company dashboards provides not just personal information but the ability to manipulate corporate records, potentially enabling everything from tax fraud to money laundering.
Next Steps and Accountability
Key questions remain unanswered: How long was the system vulnerable? Can Companies House track and identify which companies were accessed? What measures are being implemented to prevent similar vulnerabilities in the future? The temporary shutdown of web filing services indicates the severity of the issue, but the full scope of potential damage may take considerable time to assess.
John Hewitt's responsible disclosure—immediately reporting the vulnerability rather than exploiting it—highlights the importance of ethical security research. His actions likely prevented widespread abuse of this critical flaw. Companies House will need to provide transparent communication about the incident's full impact and the steps being taken to secure their systems and protect affected directors.
The incident serves as a stark reminder that even government-operated services handling sensitive corporate and personal data remain vulnerable to surprisingly simple exploits. As businesses and individuals increasingly rely on digital platforms for critical operations, the consequences of security failures extend far beyond inconvenience to potentially devastating financial and personal harm.
Comments
Please log in or register to join the discussion