SolarWinds patched four critical vulnerabilities in its Serv-U file transfer software that could allow authenticated attackers to gain root-level control over servers, continuing a pattern of high-risk flaws in widely used enterprise software.
 SolarWinds has released urgent security updates addressing four critical vulnerabilities in its Serv-U Managed File Transfer software. The most severe flaw, tracked as CVE-2025-40538, allows attackers with administrative privileges to gain root or system-level access to both Windows and Linux servers running unpatched versions.
SolarWinds has released urgent security updates addressing four critical vulnerabilities in its Serv-U Managed File Transfer software. The most severe flaw, tracked as CVE-2025-40538, allows attackers with administrative privileges to gain root or system-level access to both Windows and Linux servers running unpatched versions.
Serv-U provides secure file transfer capabilities via protocols including FTP, SFTP, and HTTP/S, making it a core component in many organizations' data exchange infrastructure. According to SolarWinds' advisory: "A broken access control vulnerability exists in Serv-U which, when exploited, gives an attacker the ability to create a system admin user and execute arbitrary code as root via domain admin or group admin privileges."
The vulnerabilities include:
- CVE-2025-40538: Broken access control enabling root/admin escalation
- Two type confusion flaws allowing remote code execution
- An Insecure Direct Object Reference (IDOR) vulnerability
All flaws require attackers to already possess high-privilege credentials on target systems. This significantly reduces widespread exploitation risk but creates dangerous escalation opportunities in compromised environments. Attackers could chain these vulnerabilities with stolen credentials or other privilege escalation exploits.
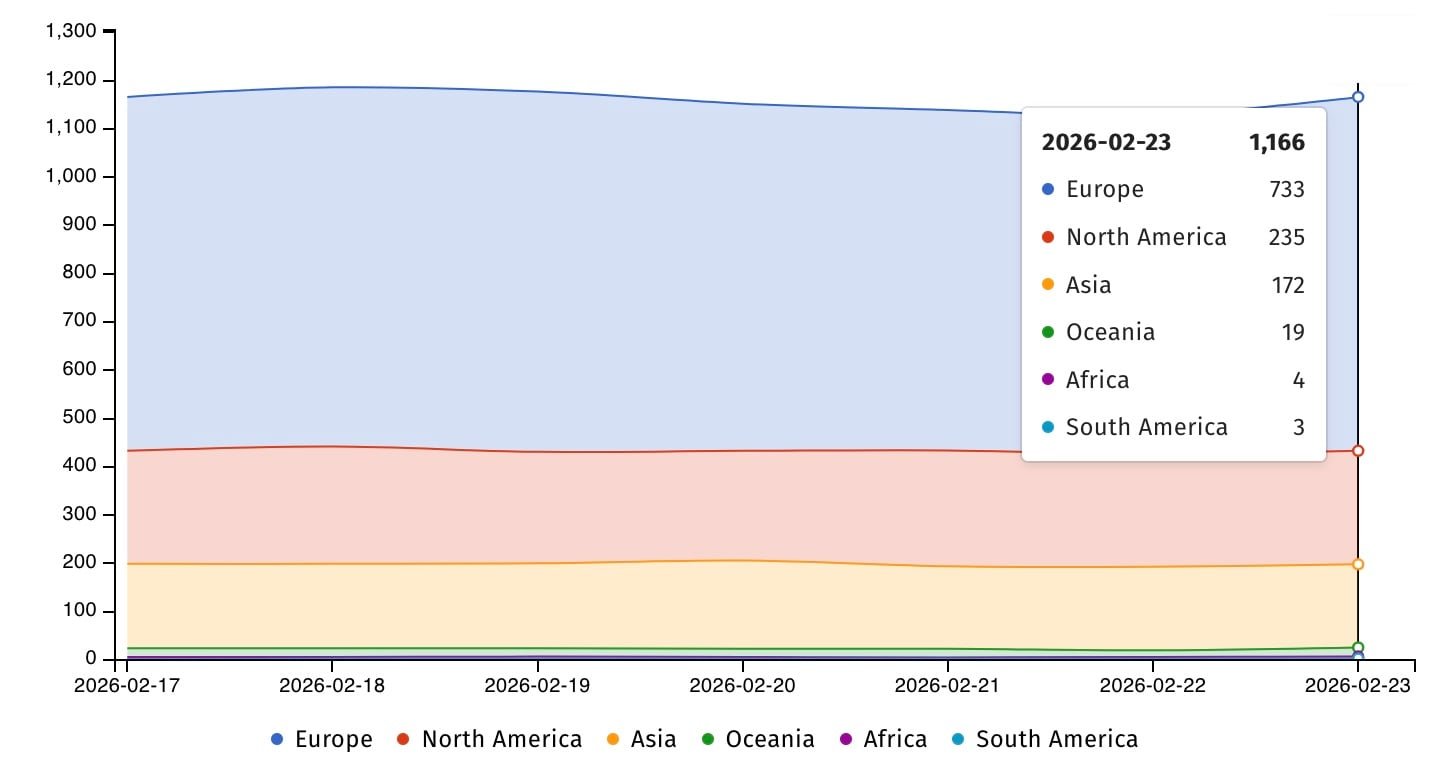
Current exposure metrics show conflicting counts of internet-facing Serv-U instances, with Shodan reporting over 12,000 systems while Shadowserver identifies approximately 1,200 exposed servers. File transfer solutions like Serv-U remain prime targets due to their access to sensitive corporate data.
Historical context reveals persistent targeting of Serv-U vulnerabilities:
- The Clop ransomware group exploited CVE-2021-35211 in 2021 attacks
- Chinese state-sponsored group DEV-0322 weaponized the same flaw
- CVE-2024-28995 was actively exploited in June 2024 using public proof-of-concept code
The U.S. Cybersecurity and Infrastructure Security Agency currently tracks nine actively exploited SolarWinds vulnerabilities. Organizations using Serv-U should:
- Immediately upgrade to Serv-U version 15.5.4 or later
- Audit administrative account privileges and monitor for unusual activity
- Restrict external access to Serv-U interfaces through network segmentation
- Review CISA's known exploited vulnerabilities catalog for additional SolarWinds patches
While these flaws require initial privileged access, their severity warrants prioritized patching given Serv-U's history of targeted exploitation and the catastrophic impact of root-level compromise.

Comments
Please log in or register to join the discussion