ManoMano, a major European DIY marketplace, confirms a data breach affecting 38 million customers after hackers compromised a third-party service provider. The incident exposed personal information including names, emails, phone numbers, and customer service communications, though passwords remained secure.
European DIY chain ManoMano has confirmed a significant data breach affecting 38 million customers after hackers compromised one of its third-party service providers. The company discovered the unauthorized access in January 2026 and has since notified both affected customers and relevant authorities.
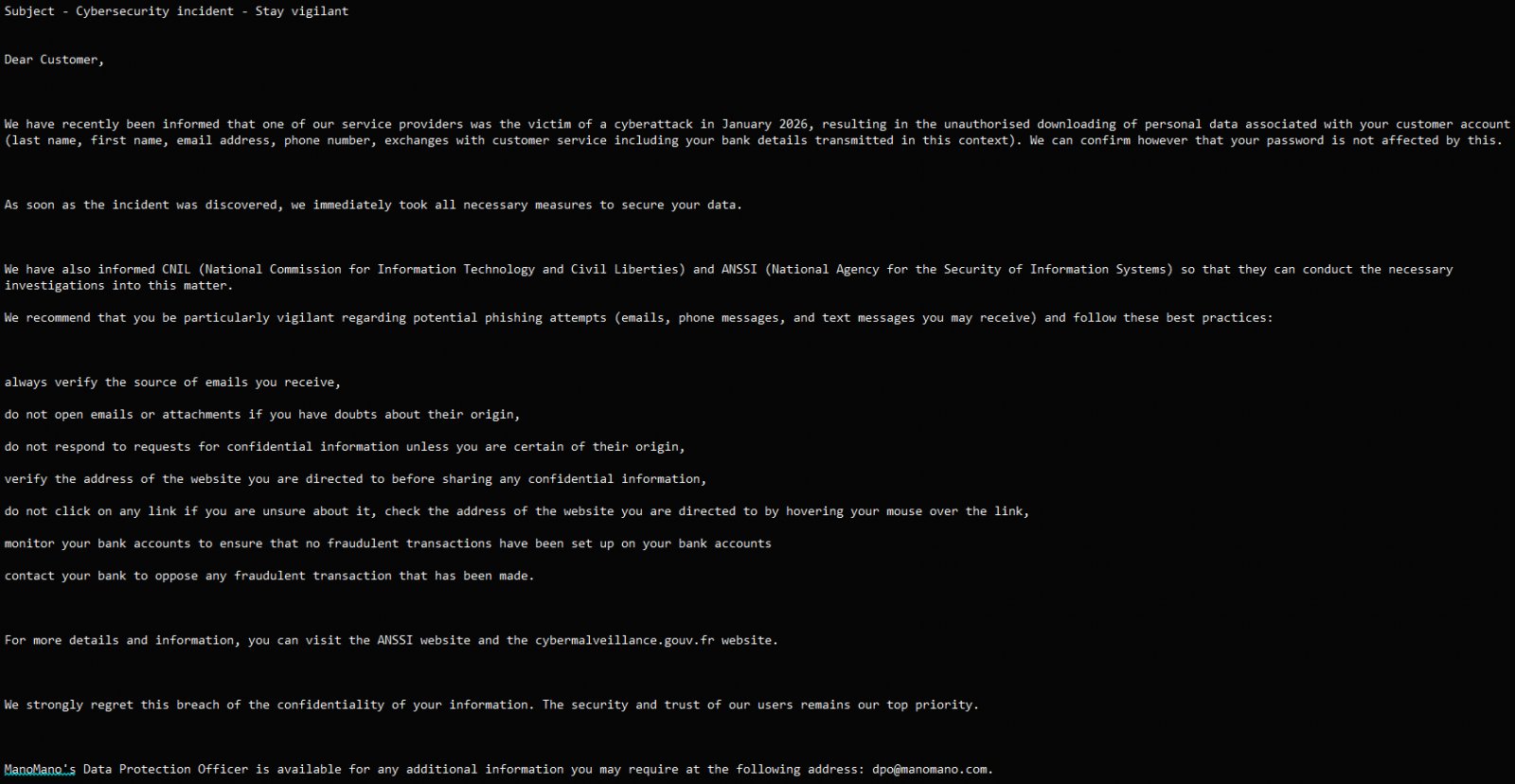
Notice sent to customers Source: ManoMano
The breach was first publicly claimed earlier this month by a threat actor using the alias "Indra" on a hacker forum, who alleged possession of 37.8 million user account details along with thousands of support tickets and attachments. While these numbers closely align with ManoMano's official disclosure, the company has not confirmed the specific claims made by the hacker.
According to cybersecurity firm Hackmanac, the compromised organization was identified as a Tunis-based customer support service provider that suffered a Zendesk breach. This highlights the growing risk posed by third-party vendors in supply chain attacks, where a single compromised partner can expose millions of customer records across multiple organizations.
ManoMano operates as a French e-commerce marketplace specializing in DIY, home improvement, gardening, and related products. The company serves customers across France, Belgium, Spain, Italy, Germany, and the United Kingdom, with its e-stores reportedly attracting 50 million unique visitors per month. This massive customer base makes the breach particularly concerning from both a privacy and security perspective.
What Data Was Exposed? The exposed information varies per individual, depending on their interactions with the platform. According to ManoMano's notification to customers, the compromised data includes:
- Full name
- Email address
- Phone number
- Customer service communications
Importantly, ManoMano emphasizes that no account passwords were accessed during the breach, and no data modifications occurred on the company's systems. This distinction is crucial for customers concerned about account takeover attempts.
Company Response and Security Measures Upon discovering the breach, ManoMano took immediate action to secure its environment. The company's response included:
- Disabling the relevant access points used by the compromised third-party provider
- Revoking the subcontractor's access to customer data
- Strengthening access controls and monitoring systems
- Notifying relevant authorities, including CNIL (France's data protection authority) and ANSSI (France's cybersecurity agency)
- Informing impacted customers with guidance on protecting themselves
The company's notification to customers contains practical recommendations for protecting against potential phishing and social engineering attempts. These include verifying incoming communications and sender identity, monitoring bank accounts for fraudulent transactions, and avoiding clicking on suspicious links or downloading email attachments.
The Growing Threat of Third-Party Breaches This incident underscores a critical vulnerability in modern business operations: third-party risk. As companies increasingly rely on external service providers for customer support, data processing, and other functions, the attack surface expands beyond their direct control.
The Zendesk connection is particularly noteworthy, as the customer service platform is widely used across industries. When a service provider like Zendesk experiences a breach, it can potentially impact hundreds or thousands of client organizations simultaneously.
Customer Protection Recommendations While ManoMano has taken steps to secure its systems, customers should remain vigilant. Here are key actions affected individuals should consider:
Monitor communications carefully: Be extra cautious of any emails or messages claiming to be from ManoMano or related services. Verify sender addresses and contact the company directly if unsure.
Watch financial accounts: Although financial data wasn't directly exposed in this breach, the combination of personal information could be used for social engineering attacks targeting banks or other financial institutions.
Enable multi-factor authentication: If you use the same email address for other accounts, ensure those accounts have additional security measures enabled.
Be skeptical of unsolicited contact: Scammers often exploit data breaches by contacting victims with convincing but fraudulent messages designed to extract more information or money.
Consider credit monitoring: While not directly related to this breach, it's generally good practice to monitor your credit report for any unusual activity following a data exposure.
Industry Context Data breaches affecting millions of customers have become increasingly common in recent years. Similar incidents have impacted major companies across various sectors:
- PayPal recently disclosed a data breach that exposed user information for six months
- Eurail reported that stolen traveler data was put up for sale on the dark web
- Major luxury brands including Louis Vuitton, Dior, and Tiffany were fined $25 million over data breaches
- Odido experienced a breach exposing personal information of 6.2 million customers
These incidents collectively demonstrate that no industry or company size is immune to cyber threats, and the consequences can be severe both financially and reputationally.
Ongoing Investigation ManoMano notes that the investigation is ongoing and that they cannot share additional technical details at this stage. This is standard practice in breach investigations, as premature disclosure of technical details could interfere with law enforcement efforts or reveal additional vulnerabilities.
The company's transparent communication with customers and authorities is a positive sign, though affected individuals will likely need to remain vigilant for months or even years following the breach, as stolen personal information can be used in various types of fraud long after the initial incident.
As the digital economy continues to grow and more personal data is collected and processed by companies worldwide, incidents like this serve as a reminder of the importance of robust cybersecurity practices, careful vendor management, and proactive customer protection measures.

Comments
Please log in or register to join the discussion