Common business tools like PDF readers, email clients, and document processors represent a significant but often overlooked attack surface, with security experts emphasizing the need for comprehensive third-party patching strategies.
The security landscape is shifting as organizations recognize that the most significant vulnerabilities often reside not in core infrastructure, but in the everyday applications that power business operations. Security teams are increasingly turning their attention to third-party applications as a critical component of their attack surface strategy.
According to recent analysis, common business tools such as PDF readers, email clients, document processors, and browsers represent one of the most consistent yet undermanaged aspects of enterprise security. These applications, while essential for daily operations, often fall outside regular patching cycles, creating vulnerabilities that threat actors can exploit with remarkable precision.
"The standardization of business tools has created a predictable environment for attackers," noted cybersecurity analyst Dr. Sarah Jenkins. "When nearly every organization uses the same PDF reader or email client, attackers can develop exploits with high confidence they'll find vulnerable systems. This commonality is both a business necessity and a security challenge."
The business footprint paradox
Organizations often assume their security posture is primarily defined by their operating systems, networks, and identity systems. However, the reality is that the actual attack surface is shaped by the applications employees use daily. These tools—PDF readers, compression utilities, remote access clients, and office suites—create a shared business footprint across organizations.
"What makes these applications particularly dangerous is their combination of ubiquity and familiarity," explained Michael Torres, CISO at a financial services firm. "Users interact with them dozens of times daily, often without hesitation. An attacker who weaponizes a common file format or email attachment is exploiting not just a technical vulnerability, but human behavior."
The probability-driven attacks
Security researchers observe that modern attacks are increasingly probability-driven rather than targeting specific organizations. Attackers focus on vulnerabilities in widely deployed applications, knowing the likelihood of finding compatible systems is high.
"We're seeing a shift from spray-and-pray attacks to precision exploitation based on common application footprints," stated Elena Petrova, threat intelligence researcher at CyberSec Labs. "When a vulnerability is discovered in a popular PDF reader, it's not just a potential risk—it's a near certainty that somewhere in your organization, someone will encounter that vulnerability."
The challenge of third-party patching
Unlike operating systems, third-party applications present unique patching challenges. Different vendors have different update mechanisms, some applications auto-update while others require manual intervention, and some are intentionally kept at older versions due to compatibility concerns.
"Enterprises have sophisticated processes for patching Windows, macOS, and Linux systems, but third-party applications often fall through the cracks," commented David Chen, security operations manager at a healthcare provider. "We've found multiple versions of the same application across our environment, some with known vulnerabilities that are years old."
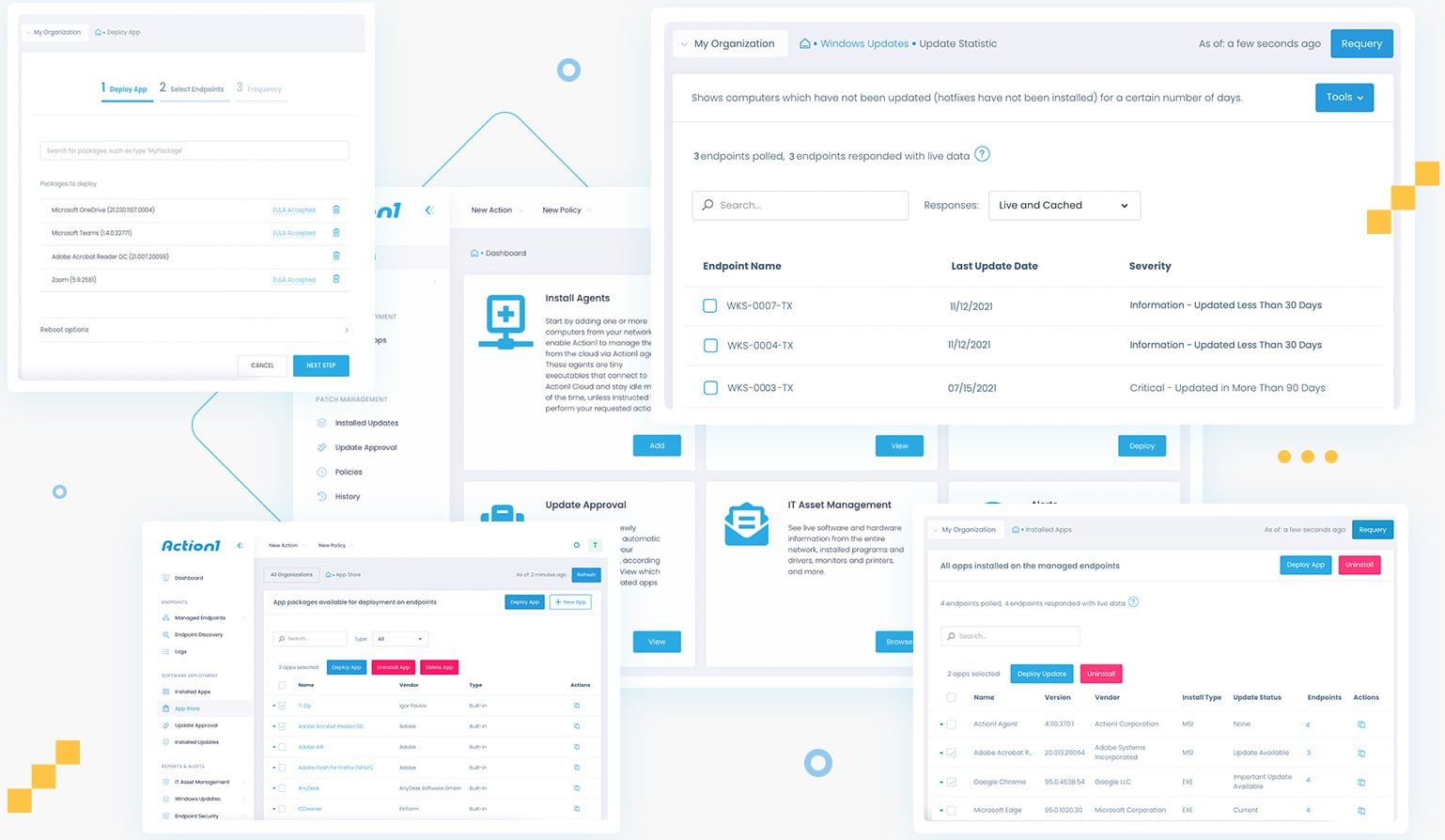
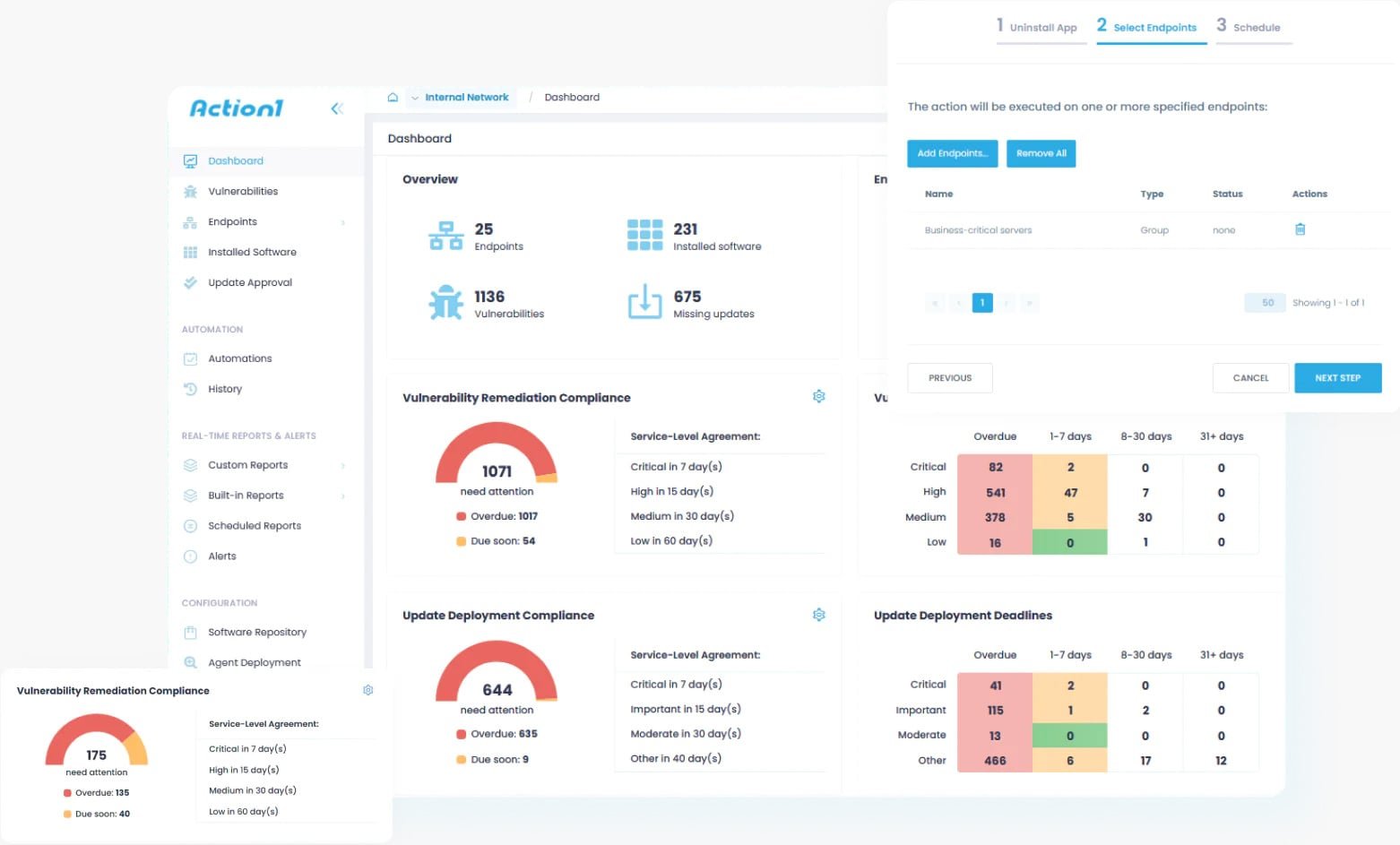
Organizations are turning to solutions that provide visibility into third-party application vulnerabilities across endpoints. Action1, a patch management platform, has extended its capabilities to include comprehensive third-party application monitoring and remediation.
"Third-party applications are not adjacent to the platform—they are part of how the platform operates," said Alex Vovk, CEO of Action1. "Effective security requires understanding this complete footprint. Our platform provides real-time visibility into all applications across endpoints, regardless of whether they're part of the standard OS deployment."
The human factor in third-party security
Beyond technical challenges, third-party applications exploit human behavior. Employees routinely open PDFs, Word documents, and email attachments without considering potential risks. This routine interaction creates opportunities for attackers who craft exploits targeting these common behaviors.
"Security awareness training often focuses on phishing and suspicious links, but we need to extend that to everyday applications," warned Dr. Lisa Park, human factors researcher in cybersecurity. "The line between 'work document' and 'malicious payload' is often invisible to users until it's too late."
Practical recommendations for third-party security
Security experts recommend several approaches to managing third-party application risks:
- Comprehensive inventory: Maintain a complete inventory of all applications across endpoints, not just those deployed through official channels
- Regular vulnerability assessment: Continuously scan for vulnerabilities in third-party applications, including those that may not be part of standard patch cycles
- Prioritization based on business footprint: Focus patching efforts on applications that are most common in your environment
- User education: Train employees to recognize potential threats in common file formats and applications
- Automated remediation: Implement solutions that can automatically detect and remediate vulnerabilities in third-party applications
The future of third-party security
As work becomes increasingly distributed and application footprints expand, third-party security will become even more critical. Organizations that develop comprehensive strategies for managing these applications will have a significant advantage in reducing their overall attack surface.
"We're moving toward a model where security is defined by the complete application ecosystem, not just the operating system," predicted James Mitchell, security architect at a global consulting firm. "This requires new approaches to visibility, prioritization, and remediation that can handle the diversity and scale of modern business applications."
For organizations looking to strengthen their third-party security posture, solutions like Action1 offer a way to gain visibility across endpoints and implement consistent patching policies for both operating systems and third-party applications. The platform supports Windows, macOS, and Linux environments with real-time monitoring and automated remediation capabilities.
"Addressing modern risk requires continuous visibility into third-party software and the ability to remediate vulnerable applications across endpoints quickly and consistently," added Vovk. "When teams evaluate modern patch management solutions, they need platforms designed around this reality."
As the threat landscape evolves, organizations that treat third-party applications as a core component of their security strategy will be better positioned to defend against increasingly sophisticated attacks that target the common tools of everyday business.

Comments
Please log in or register to join the discussion