Research reveals how PCI DSS-compliant masked credit card numbers can be brute forced using validation endpoints, putting millions of cards at risk.
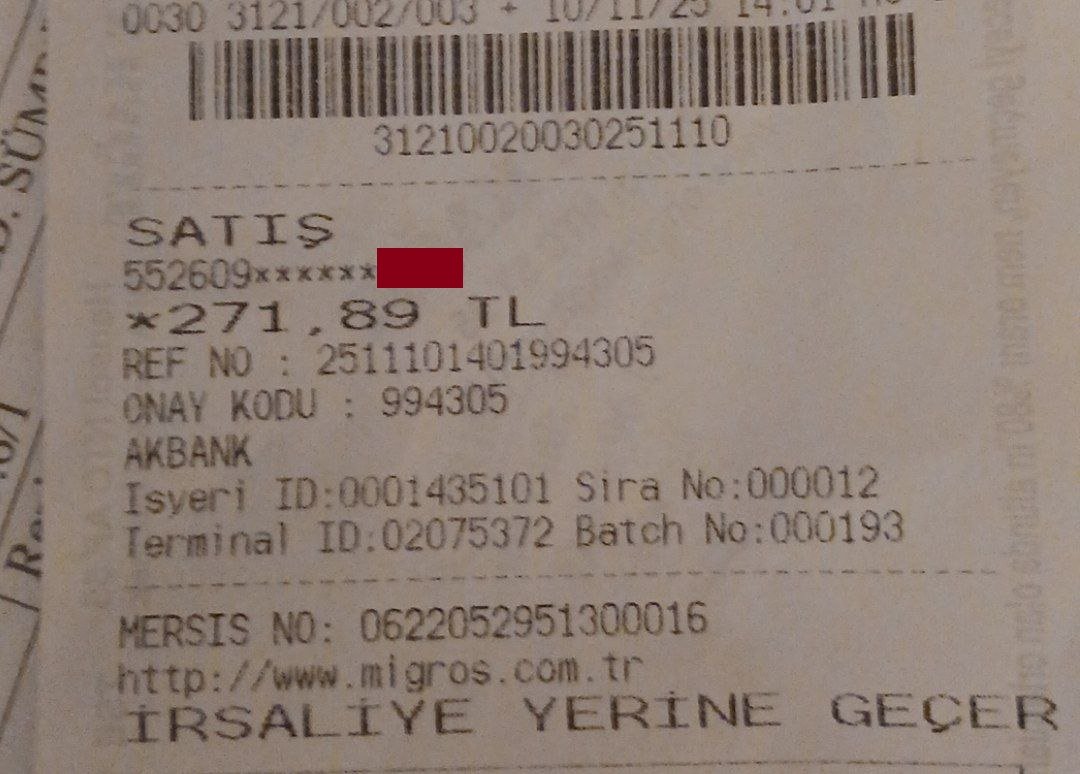
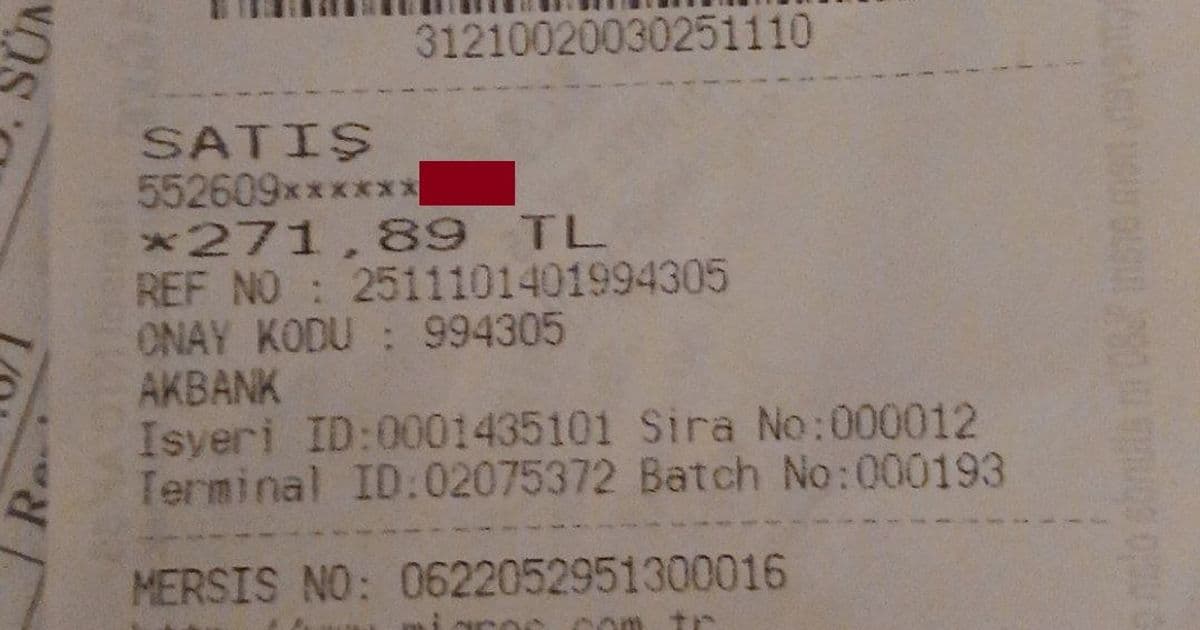
Credit card security standards designed to protect consumers may actually be creating vulnerabilities that attackers can exploit, according to recent analysis of payment system weaknesses. The PCI DSS (Payment Card Industry Data Security Standard) requires merchants to mask credit card numbers, showing only the first six and last four digits, but this practice combined with payment validation systems creates a brute force opportunity for determined attackers.
The vulnerability stems from how payment gateways validate card information. When an attacker obtains a masked credit card number (showing first 6 and last 4 digits) along with the expiration date, they only need to determine the 6 missing digits in the middle. With 16-digit cards, this leaves 100,000 possible combinations (10^6), which can be tested in a matter of hours using automated systems.
"The payment industry has standardized showing partial card numbers for security, but this creates a false sense of security," explains Metin, a security researcher who experienced this vulnerability firsthand. "When I had my account breached on an e-commerce platform, attackers used the masked card number from my profile to brute force the complete card details through multiple merchant endpoints."
The attack works by testing combinations of the missing digits against payment validation systems. Many payment gateways return specific error messages like "That card is expired" or "You got all the details right but CVV is not correct," which actually helps attackers narrow down their brute force attempts.
"The error messages from payment gateways are essentially telling attackers exactly what they need to fix," notes Metin. "It's like the system is helping them complete the puzzle."
The vulnerability is exacerbated by several factors in the payment ecosystem:
Multiple Validation Endpoints: Attackers can use stolen API credentials from various merchants to test combinations without triggering rate limits from a single source.
3D Secure Exemptions: Some merchants are exempt from requiring 3D Secure authentication, making them prime targets for completing transactions once the full card number is discovered.
Rate Limiting Gaps: While individual merchants may have rate limiting, attackers can distribute their requests across multiple endpoints, making detection difficult.
Inconsistent Implementation: Not all payment processors implement the same security measures, creating weak points in the system.
The attack described by Metin involved testing approximately 6 requests per second across multiple endpoints, with attackers successfully brute forcing the complete card number within 6 hours. Once the full number was obtained, they targeted merchants exempt from 3D Secure requirements to complete unauthorized transactions.
Industry experts acknowledge the issue but note the complexity of addressing it.
"Everyone in the payments space is aware of this vulnerability," shares Pavel, a payments engineer. "The challenge is balancing security with user experience and cost. Implementing stronger validation would require changes to the entire payment ecosystem, which moves slowly."
Potential solutions include:
- Implementing randomized error messages that don't reveal specific missing information
- Adding additional validation layers beyond just card number, expiration, and CVV
- Reducing brute force opportunities by implementing stricter rate limiting across the payment ecosystem
- Eliminating 3D Secure exemptions for high-value transactions
The PCI Security Standards Council, which manages the PCI DSS, has been gradually strengthening requirements. The latest version (4.0) includes enhanced authentication requirements but doesn't specifically address the brute force vulnerability in masked card numbers.
For consumers, the incident highlights the importance of monitoring accounts, using virtual credit cards with limits, and properly disposing of receipts that display partial card information. As Metin discovered, even following security best practices may not be enough when systemic vulnerabilities exist.
The payments industry faces a delicate balance between maintaining usability and implementing robust security measures. As digital transactions continue to grow, addressing fundamental vulnerabilities like this one will become increasingly important to maintain consumer trust in the payment ecosystem.
References:
Comments
Please log in or register to join the discussion