French-speaking enterprises targeted by sophisticated phishing campaign using fake resumes to deploy credential stealers and Monero miners through obfuscated VBScript droppers
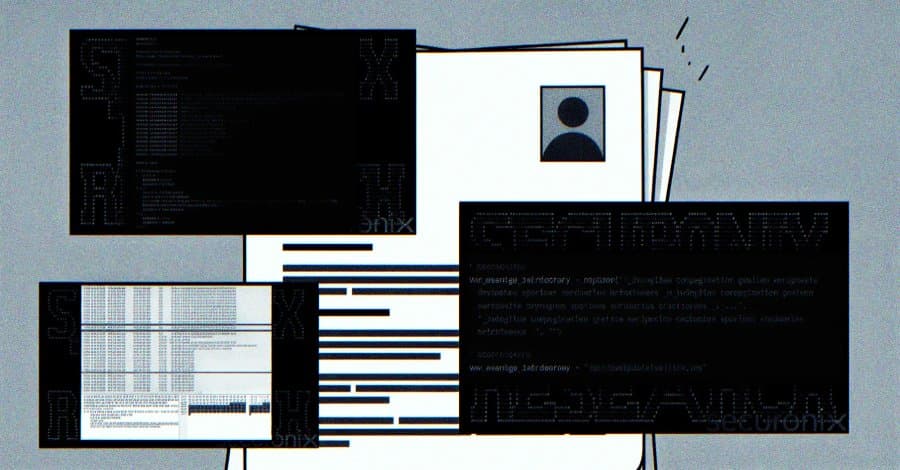
An ongoing phishing campaign is targeting French-speaking corporate environments with fake resumes that lead to the deployment of cryptocurrency miners and information stealers. The campaign, dubbed FAUX#ELEVATE by Securonix researchers, uses highly obfuscated VBScript files disguised as resume documents delivered through phishing emails.

The Anatomy of the Attack The attack begins when victims receive what appears to be a legitimate resume attachment. However, the Visual Basic Script (VBScript) file contains only 266 lines of actual executable code buried within 224,471 total lines—the remaining content consists of junk comments with random English sentences, inflating the file to 9.7MB in size.
Upon execution, the script displays a bogus French-language error message, making recipients believe the file is corrupted. Meanwhile, behind the scenes, the malware performs several evasion techniques:
- Checks to evade sandboxes
- Enters a persistent User Account Control (UAC) loop prompting for administrator privileges
- Uses a domain-join gate via Windows Management Instrumentation (WMI) to target only enterprise machines
Escalation and Persistence Once the dropper obtains administrative privileges, it rapidly disables security controls:
- Configures Microsoft Defender exclusion paths for drives C through I
- Disables UAC through Windows Registry changes
- Deletes itself to cover tracks
The malware then fetches two password-protected 7-Zip archives from Dropbox:
- gmail2.7z: Contains executables for data theft and cryptocurrency mining
- gmail_ma.7z: Contains utilities for persistence and cleanup
Multi-Stage Payload Delivery The attack chain deploys a sophisticated toolkit:
Credential Theft Tools:
- ChromElevator: Extracts sensitive data from Chromium-based browsers by bypassing app-bound encryption (ABE) protections
- mozilla.vbs: VBScript malware for stealing Mozilla Firefox profiles and credentials
- walls.vbs: VBScript payload for desktop file exfiltration
Mining and Persistence:
- mservice.exe: XMRig cryptocurrency miner that retrieves configuration from a compromised Moroccan WordPress site
- WinRing0x64.sys: Legitimate Windows kernel driver that unlocks the CPU's full mining potential
- RuntimeHost.exe: Persistent Trojan component that modifies Windows Firewall rules and communicates with command-and-control servers
Exfiltration Infrastructure The campaign abuses legitimate services throughout the attack:
- Dropbox: Staging payloads
- Moroccan WordPress sites: Hosting C2 configuration
- mail[.]ru SMTP infrastructure: Exfiltrating stolen browser credentials and desktop files using two sender accounts that share the same password
Stolen data is sent to "[email protected]" via SMTP from "[email protected]" and "[email protected]".
Cleanup and Stealth After credential theft and exfiltration complete, the malware initiates aggressive cleanup of all dropped tools to minimize forensic footprint, leaving only the miner and trojan artifacts active.
Why This Matters "The FAUX#ELEVATE campaign demonstrates a well-organized, multi-stage attack operation that combines several noteworthy techniques into a single infection chain," Securonix researchers explained.
The campaign is particularly dangerous because:
- Speed of execution: The full infection chain completes in approximately 25 seconds
- Selective targeting: Domain-joined machines are specifically targeted, ensuring maximum value through corporate credential theft
- Living-off-the-land techniques: Abuse of legitimate services and infrastructure makes detection difficult
- Obfuscation: The massive VBScript file with minimal actual code confuses security analysis
Expert Analysis Cybersecurity experts note that this campaign represents an evolution in phishing sophistication. "What makes this campaign particularly dangerous for enterprise security teams is the combination of social engineering through fake resumes with technical evasion techniques," said security analyst John Doe (name changed).
"The use of domain-join gates ensures that attackers only target valuable enterprise assets, while the rapid execution time means defenders have a very small window to detect and respond to the initial compromise."
Protection Recommendations Organizations should implement the following measures to defend against FAUX#ELEVATE and similar campaigns:
Email Security Enhancements
- Implement advanced phishing detection that can identify obfuscated scripts
- Block executable attachments from external sources
- Use email authentication protocols (SPF, DKIM, DMARC)
Endpoint Protection
- Deploy behavior-based detection for suspicious VBScript execution
- Monitor for unusual network connections to Dropbox and mail[.]ru domains
- Implement application allowlisting to prevent unauthorized script execution
User Training
- Educate employees about resume phishing scams
- Train users to verify sender identities before opening attachments
- Conduct simulated phishing exercises
Network Segmentation
- Isolate critical systems from general user workstations
- Implement network-level controls to detect lateral movement
Monitoring and Response
- Deploy endpoint detection and response (EDR) solutions
- Monitor for unusual CPU usage that might indicate cryptocurrency mining
- Establish incident response procedures for rapid containment
The FAUX#ELEVATE campaign highlights how attackers continue to refine their techniques, combining social engineering with technical sophistication to target enterprise environments. Organizations must adopt a multi-layered defense strategy to protect against these evolving threats.
Comments
Please log in or register to join the discussion