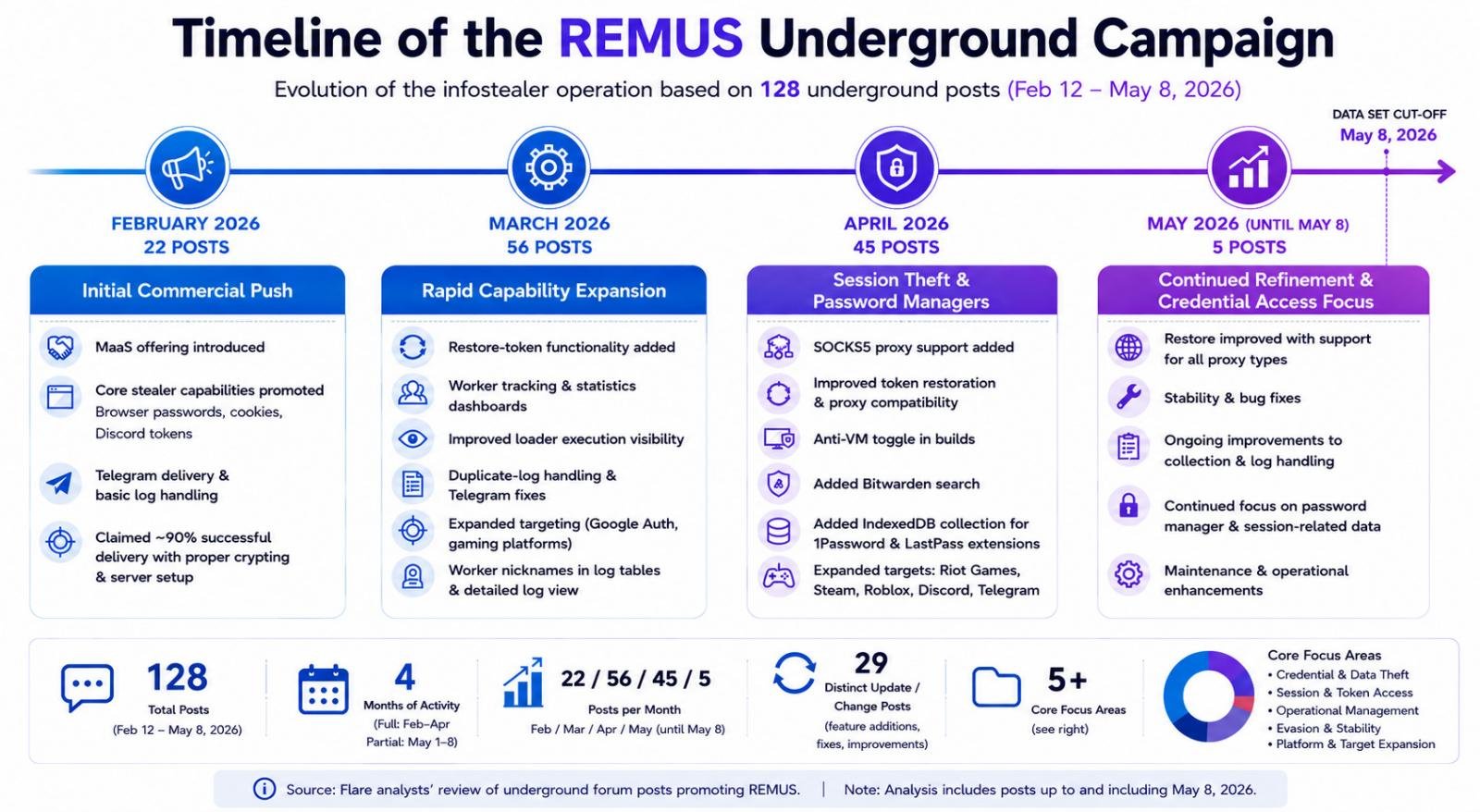
Flare’s analysis of 128 underground posts reveals how the REMUS infostealer has morphed from a simple credential‑stealer into a full‑featured malware‑as‑a‑service platform, emphasizing session theft, password‑manager collection, and a software‑business style development cycle.
Inside the REMUS Infostealer: Session Theft, MaaS, and Rapid Evolution
In the spring of 2026 a new infostealer surfaced on dark‑web forums, quickly drawing the attention of security researchers. Named REMUS, the malware shares code‑level traits with the older Lumma Stealer, but its underground footprint tells a richer story. Flare’s researchers examined 128 posts linked to the REMUS operation between 12 February and 8 May 2026, uncovering a tightly run Malware‑as‑a‑Service (MaaS) business that iterates on features almost as fast as a commercial SaaS product.
From Promo‑Copy to Platform
February – the commercial launch
The earliest advertisements framed REMUS as a "plug‑and‑play" stealer. The operator boasted a ~90 % callback rate when paired with “good crypting and a dedicated intermediary server.” Support promises read like a consumer‑software warranty: “24/7 support” and “simple enough that even a child can figure it out.”
“With good crypting and a dedicated intermediary server, the callback rate is ~90%.” – REMUS post, 3 Feb 2026
The focus was on classic theft vectors – Chrome/Edge/Firefox credentials, Discord tokens, and Telegram delivery – but the language already hinted at a product mindset: version numbers, changelogs, and a public roadmap.
March – operational visibility becomes a feature
During the most active development month, the operator released a cascade of updates:
- Restore‑token functionality – allowing stolen sessions to be re‑authenticated without fresh credentials.
- Worker nicknames and statistics pages – giving buyers a dashboard to see infection counts, failed loads, and duplicate‑log filtering.
- Improved Telegram delivery – ensuring exfiltrated data reaches the buyer’s channel reliably.
These additions shifted the conversation from “what we steal” to “how we manage the campaign.” By exposing internal metrics, the operator turned the botnet into a service that could be monitored and tuned, a hallmark of mature MaaS operations.
April – the session‑theft pivot
April’s changelog marks a clear strategic pivot toward session continuity:
- SOCKS5 proxy support for token restoration, enabling attackers to route stolen sessions through clean IPs.
- IndexedDB collection for 1Password and LastPass extensions; similar code targeted Bitwarden. This is the first explicit mention of password‑manager data.
- Anti‑VM toggles and gaming‑platform targeting (e.g., Steam, Riot Games) broadened the value proposition beyond corporate credentials.
“Added IndexedDB collection for 1Password and LastPass extensions.” – REMUS post, 22 Apr 2026
The emphasis on cookies, authentication tokens, and browser‑side storage reflects a broader underground trend: stealing an already‑authenticated session is more valuable than a raw password because it bypasses MFA, device‑verification prompts, and risk‑based login challenges.
May – stabilization and bug‑fixes
The final weeks of the data set show fewer headline‑grabbing features and more polish:
- Refined restore workflows to reduce false positives.
- Minor bug fixes in log parsing and delivery pipelines.
- Continued performance tweaks to keep the advertised 90 % success rate.
The shift from rapid feature expansion to stability mirrors the lifecycle of legitimate software products, where early‑stage innovation gives way to reliability engineering.
Why session theft matters more than passwords
Traditional infostealers harvested usernames and passwords, leaving the victim to re‑authenticate and often trigger MFA alerts. REMUS, by contrast, focuses on persistent authentication artifacts:
- Cookies and tokens grant immediate access to web services without any additional login step.
- Proxy‑assisted restoration lets attackers spin up clean IPs, making detection harder.
- Password‑manager data provides a vault of credentials across services, amplifying the impact of a single infection.
Flare’s telemetry shows a spike in “high‑value cookie” alerts coinciding with REMUS activity, confirming that the underground market is paying a premium for these artifacts.
The MaaS business model in practice
The REMUS operation illustrates how modern cybercrime groups are adopting software‑development best practices:
- Versioned releases (e.g., v1.3.2, v1.4.0) with changelogs.
- Customer support tickets handled via private Telegram groups.
- Metrics dashboards that expose worker health, infection rates, and duplicate logs.
- Continuous integration‑style testing, evident from rapid bug‑fix cycles.
Such professionalism lowers the barrier for low‑skill actors to run profitable campaigns, while the developers can focus on feature work and infrastructure scaling.
Practical takeaways for defenders
| Recommendation | How to implement |
|---|---|
| Monitor for session artifacts – cookies, Discord tokens, Steam session IDs – in outbound traffic and endpoint logs. | Deploy a SIEM rule that flags large volumes of Set‑Cookie or Authorization header exfiltration to unknown domains. |
| Detect proxy‑enabled loaders – REMUS uses SOCKS5 for token restoration. | Look for sudden spikes in outbound SOCKS5 connections from workstations that normally use direct internet access. |
| Secure password‑manager data – enable hardware‑backed vaults and enforce master‑password re‑prompt on extension access. | Configure enterprise policies that restrict IndexedDB access for extensions not on an approved list. |
| Threat‑intel feed integration – ingest Flare’s REMUS indicators (C2 domains, loader hashes) into your detection stack. | Automate feed ingestion via STIX/TAXII or simple CSV import into your EDR/NGAV solution. |
Looking ahead
REMUS’s rapid evolution over just three months underscores a new normal for infostealer operations: they are no longer static binaries sold on a forum, but evolving platforms that prioritize session theft, password‑manager harvesting, and operational transparency. As the underground continues to professionalize, defenders must shift focus from “what the malware does” to “how the service is delivered and monetized.”
Staying ahead means tracking underground chatter, monitoring for session‑related exfiltration, and hardening browser extensions and password‑manager integrations.
For a deeper dive into the raw data and the full set of indicators, see Flare’s public report and consider signing up for their free trial.
Comments
Please log in or register to join the discussion