Handala, an Iranian hacktivist group, claims responsibility for wiping 200,000+ devices at medical tech giant Stryker, citing retaliation for a deadly missile strike.
An Iranian hacktivist group with ties to Tehran's intelligence services has claimed responsibility for a massive data-wiping attack against Stryker, a major American medical technology company, in what appears to be retaliation for a deadly missile strike in Iran earlier this year.
Iranian Hacktivist Group Claims Responsibility
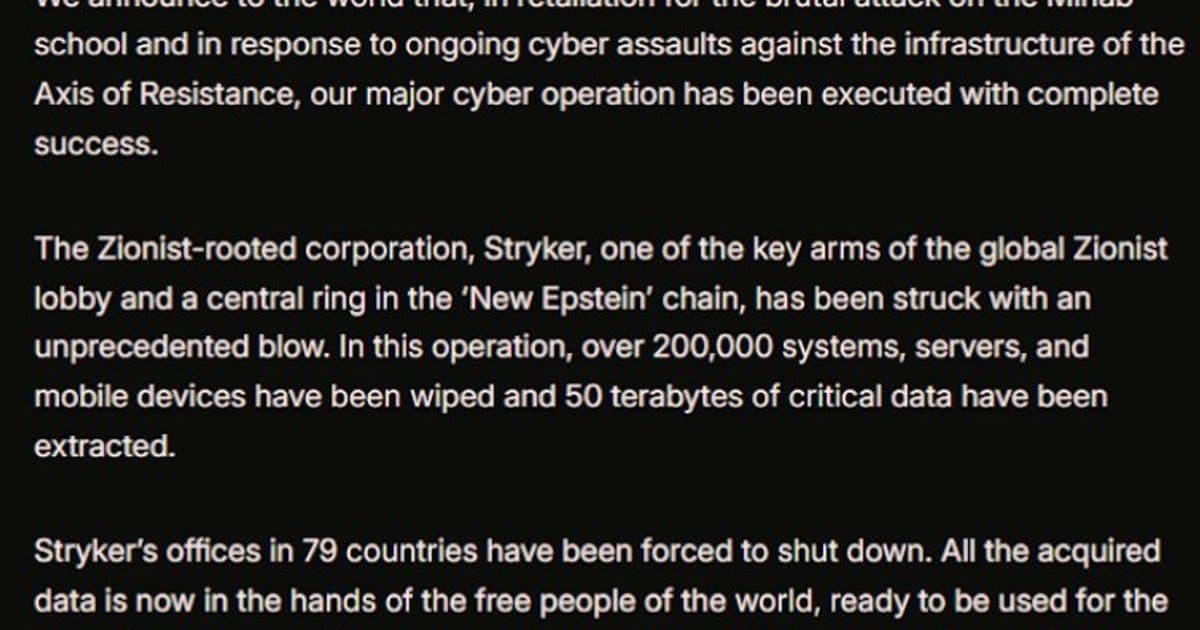
The group, known as Handala (also called Handala Hack Team), posted a lengthy manifesto on Telegram claiming it erased data from more than 200,000 systems, servers, and mobile devices across Stryker's global operations. The attack has forced the company to shut down offices in 79 countries, according to the hackers' claims.
Handala justified the attack as retaliation for a February 28 missile strike that killed at least 175 people, most of them children, at an Iranian school. The New York Times reported Wednesday that a military investigation determined the United States was responsible for the deadly Tomahawk missile strike.
Global Impact on Medical Technology Giant
Stryker, headquartered in Kalamazoo, Michigan, is a global leader in medical and surgical equipment with $25 billion in annual sales and 56,000 employees across 61 countries. The company's largest hub outside the United States is in Ireland, where reports indicate more than 5,000 workers were sent home as a result of the attack.
Multiple sources have confirmed that systems at Stryker's Cork headquarters have been shut down, with devices wiped clean. Employees report that Microsoft Outlook on personal phones was affected, and login pages have been defaced with Handala's logo.
Technical Details Emerge
According to a trusted source familiar with the attack who spoke on condition of anonymity, the perpetrators appear to have used Microsoft's Intune service to issue a remote wipe command against all connected devices. Intune is a cloud-based solution that IT teams use to enforce security and data compliance policies across devices regardless of location.
This technical detail is supported by discussions on Reddit, where several users claiming to be Stryker employees said they were instructed to urgently uninstall Intune.
Healthcare Supply Chain Concerns
The attack has already begun affecting healthcare providers. A healthcare professional at a major U.S. university medical system told KrebsOnSecurity they are currently unable to order surgical supplies normally sourced through Stryker. "This is a real-world supply chain attack," the expert said, noting that most U.S. hospitals performing surgeries rely on Stryker supplies.
However, John Riggi, national advisor for the American Hospital Association, said the organization is not yet aware of any supply chain disruptions. "We are aware of reports of the cyber attack against Stryker and are actively exchanging information with the hospital field and the federal government to understand the nature of the threat and assess any impact to hospital operations," Riggi said in an email.
Who Is Handala?
Palo Alto Networks recently profiled Handala as one of several Iran-linked hacker groups, linking it to Iran's Ministry of Intelligence and Security (MOIS). The security firm says Handala surfaced in late 2023 and is assessed as one of several online personas maintained by Void Manticore, a MOIS-affiliated actor.
The group's manifesto referred to Stryker as a "Zionist-rooted corporation," likely referencing the company's 2019 acquisition of the Israeli company OrthoSpace. Handala's hack-and-leak activities are primarily focused on Israel, with occasional targeting outside that scope when it serves a specific agenda.
The Growing Threat of Wiper Attacks
Wiper attacks, which involve malicious software designed to overwrite existing data on infected devices, have become an increasingly common tool in cyber warfare. What makes this attack particularly concerning is the use of legitimate administrative tools like Microsoft Intune to execute the wipe commands, potentially making detection and prevention more difficult.
The attack highlights the vulnerability of healthcare supply chains to cyber incidents and raises questions about the security of critical medical infrastructure. As hospitals and healthcare systems become increasingly reliant on technology and connected devices, the potential for supply chain disruptions through cyber means grows significantly.
For now, Stryker's operations remain severely disrupted, with employees communicating via WhatsApp for updates and the company's main headquarters reporting a "building emergency." The full extent of the damage and the timeline for recovery remain unclear as investigations continue.
Comments
Please log in or register to join the discussion