Toronto police dismantle first-of-its-kind SMS blaster operation that infiltrated tens of thousands of devices, highlighting growing security threats from mobile signal interception technology.
Toronto authorities have arrested three individuals operating mobile SMS blasters that caused 13 million network disruptions and compromised tens of thousands of mobile devices across the city. The operation, dubbed "Project Lighthouse" by police, represents Canada's first documented case of this particular form of cybercrime, which not only facilitates large-scale smishing attacks but also interferes with critical emergency services like 911.
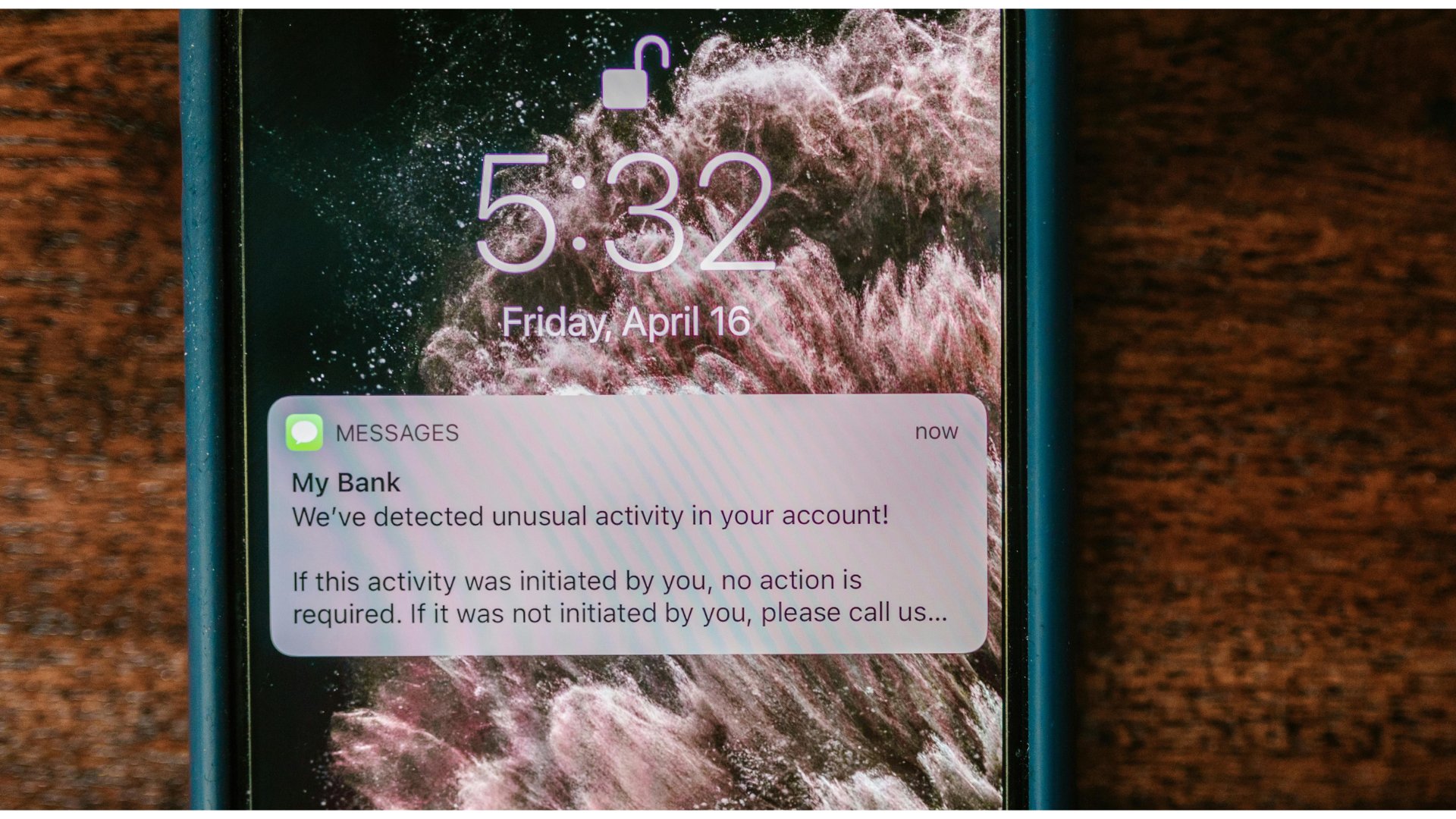
The SMS blaster devices, which were being operated from vehicles moving through downtown Toronto, function by impersonating legitimate cellular network base stations. When nearby mobile devices automatically connect to these stronger fake signals, the operators can intercept communications and send fraudulent text messages that appear to originate from official institutions such as banks or government agencies.
"What makes this particularly concerning is the scale and impact," Toronto Police Deputy Chief Robert Johnson stated during a news conference streamed on YouTube. "This wasn't targeting a single individual or business. It had the ability to reach thousands of devices at once. And beyond the financial risk, there are real public safety implications. For instance, when devices are diverted from legitimate networks, even briefly, it interferes with a person's ability to connect to emergency services."
Technical Operation of SMS Blasters
SMS blasters exploit a fundamental aspect of mobile network connectivity: devices automatically connect to the strongest available cellular signal. The devices used in Toronto were "uniquely built," according to Detective Sergeant Lindsay Riddell, who explained that police aren't sharing specific details about the seized hardware for security reasons.
Unlike more sophisticated IMSI catchers (also known as "stingrays") that can intercept and route all communications, SMS blasters primarily focus on mass text message distribution. They broadcast signals stronger than legitimate cell towers, causing nearby phones to connect to the fake network. Once connected, the blaster can send SMS messages to all connected devices simultaneously.
The fraudulent messages typically impersonate trusted institutions, displaying names rather than phone numbers, which increases the likelihood of recipients trusting and interacting with the content. These messages often contain links to phishing websites designed to steal credentials or facilitate fraudulent charges.
Impact Assessment
The Canadian investigation revealed that the SMS blaster operation resulted in:
- 13 million network disruptions
- Infiltration of tens of thousands of mobile devices
- Blocking of legitimate network access for affected devices
- Prevention of emergency calls, including 911 services
- Potential data theft from compromised devices
This scale of disruption represents a significant challenge to both individual security and public safety infrastructure. The ability to divert devices from legitimate networks, even temporarily, creates a window during which emergency services may be inaccessible.
Global Context and Emerging Threats
While this represents Canada's first documented SMS blaster operation, similar threats have been identified globally. In February 2026, Philippine authorities arrested two Chinese nationals operating a comparable scheme using IMSI devices near government installations, military bases, and the U.S. embassy.
The distinction between SMS blasters and IMSI catchers is important for understanding the threat landscape:
- SMS blasters primarily focus on mass text distribution for smishing attacks
- IMSI catchers can intercept and route all cellular communications, potentially capturing voice calls and metadata
Both technologies, however, share the same fundamental vulnerability: they exploit the automatic connectivity behavior of mobile devices to stronger signals.
Security Implications and Future Considerations
The Toronto operation highlights several critical security concerns:
Scale of Impact: A single mobile device can compromise thousands of targets simultaneously, making it an attractive tool for organized crime groups.
Evolving Technology: As documented in the police statement, the devices are becoming more sophisticated and customized, suggesting a maturing criminal market for such equipment.
Public Safety Risks: The ability to disrupt emergency services represents a direct threat to public safety that goes beyond typical cybercrime concerns.
Regulatory Challenges: The operation underscores difficulties in regulating hardware that, while designed for criminal purposes, may have legitimate applications in network testing and security research.
As mobile networks continue to evolve with 5G deployment and increased IoT connectivity, the attack surface for signal interception technologies may expand. The Toronto Police Service has urged citizens to remain vigilant about traditional smishing attempts, even as this particular mobile threat has been neutralized.
For more information about the operation, you can watch the Toronto Police news conference or visit the official Toronto Police Service website for ongoing updates.

Comments
Please log in or register to join the discussion