A malicious npm package masquerading as an OpenClaw installer has been downloaded 178 times, deploying a sophisticated remote access trojan that steals macOS credentials, browser data, crypto wallets, and other sensitive information through social engineering and persistent backdoor access.
Cybersecurity researchers have uncovered a malicious npm package that poses as an OpenClaw installer to deploy a sophisticated remote access trojan (RAT) capable of stealing sensitive data from macOS systems. The package, named "@openclaw-ai/openclawai," was uploaded to the npm registry on March 3, 2026, by a user named "openclaw-ai" and has been downloaded 178 times to date.
Sophisticated Social Engineering Attack
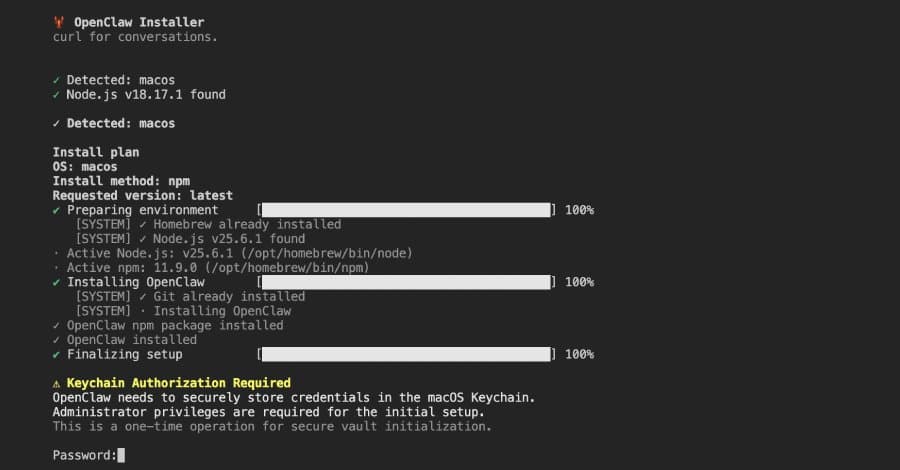
The malicious package employs a multi-stage attack that begins with a convincing fake command-line interface displaying animated progress bars to simulate OpenClaw installation. After the purported installation completes, the script presents a bogus iCloud Keychain authorization prompt, requesting users to enter their system password.
"The attack is notable for its broad data collection, its use of social engineering to harvest the victim's system password, and the sophistication of its persistence and C2 [command-and-control] infrastructure," said Meitar Palas, a security researcher at JFrog, which discovered the package.
Multi-Stage Malware Deployment
Once installed, the package triggers a postinstall hook that re-installs itself globally using the command: "npm i -g @openclaw-ai/openclawai." The OpenClaw binary then points to "scripts/setup.js" through the "bin" property in the "package.json" file, turning the package into a globally accessible command-line tool.
The setup.js file serves as the first-stage dropper, displaying the fake CLI interface before retrieving an encrypted second-stage JavaScript payload from the command-and-control server at "trackpipe[.]dev." This payload is decoded, written to a temporary file, and spawned as a detached child process to continue running in the background.
Comprehensive Data Theft Capabilities
The second-stage payload, comprising approximately 11,700 lines of code, functions as a full-fledged information stealer and RAT framework. It can:
- Steal macOS Keychain databases, including local login.keychain-db and iCloud Keychain
- Extract credentials, cookies, credit cards, and autofill data from all Chromium-based browsers
- Access cryptocurrency wallet applications and browser extensions
- Steal SSH keys and developer credentials for AWS, Azure, Google Cloud, Kubernetes, Docker, and GitHub
- Capture AI agent configurations
- Access data protected by Full Disk Access, including Apple Notes, iMessage history, Safari browsing history, Mail account configurations, and Apple account information
If Safari directory access is blocked due to lack of Full Disk Access, the script displays an AppleScript dialog with step-by-step instructions to grant Terminal FDA permissions, enabling the malware to steal protected data.
Persistent Backdoor and Advanced Features
After data collection, the malware compresses the stolen information into a tar.gz archive and exfiltrates it through multiple channels, including the C2 server, Telegram Bot API, and GoFile.io. The malware then enters a persistent daemon mode that monitors clipboard content every three seconds, transmitting any data matching pre-defined patterns for private keys, cryptocurrency addresses, AWS keys, and other sensitive information.
Additional capabilities include:
- Monitoring running processes
- Scanning incoming iMessage chats in real-time
- Executing commands from the C2 server, including arbitrary shell commands, URL opening, payload downloads, file uploads, SOCKS5 proxy management, and browser cloning
- Self-destruct and update functions
The browser cloning feature is particularly dangerous, launching a headless Chromium instance with the victim's existing browser profile containing cookies, login credentials, and browsing history. This provides the attacker with a fully authenticated browser session without needing to access credentials directly.
Ongoing Threat
Despite being identified, the malicious package remains available for download on the npm registry. JFrog emphasized that the combination of social engineering, encrypted payload delivery, broad data collection, and persistent RAT functionality makes this a particularly dangerous threat to macOS developers and users.
The attack demonstrates how attackers are increasingly targeting developer ecosystems and supply chain security, using sophisticated social engineering techniques to bypass macOS security protections and gain persistent access to sensitive systems and data.
Comments
Please log in or register to join the discussion