Security researcher Chaotic Eclipse has revealed a critical zero-day vulnerability in Microsoft's BitLocker encryption that allows full access to protected drives without authentication, raising serious questions about enterprise security and potential backdoors.
Microsoft BitLocker Vulnerability Exposes Millions of Drives to Zero-Day Exploit
Security researcher Chaotic Eclipse has published details of a critical zero-day vulnerability affecting Microsoft's BitLocker encryption technology that could compromise millions of systems worldwide. The exploit, named YellowKey, allows attackers to bypass BitLocker protection entirely, gaining full access to encrypted drives without requiring authentication keys.
Technical Breakdown of the YellowKey Exploit
The YellowKey exploit represents a fundamental weakness in BitLocker's implementation. Unlike traditional attacks that focus on cracking encryption algorithms, this vulnerability bypasses the authentication mechanism entirely, rendering the encryption effectively useless in affected systems.
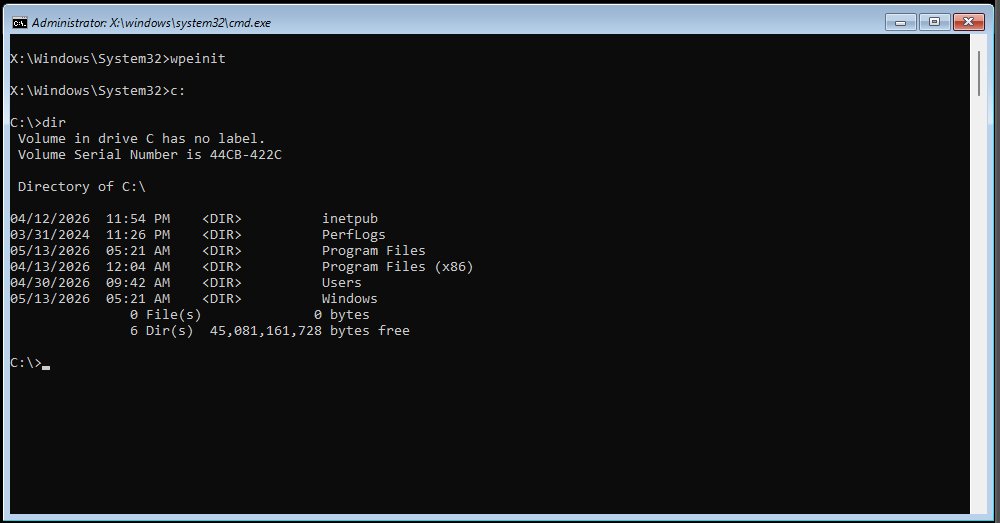
The exploit process is alarmingly simple:
- An attacker requires physical access to a target machine for approximately 30 seconds
- A standard USB stick is used to gain write access to the "System Volume Information" directory
- The attacker copies the "FsTx" folder and its contents to the USB drive
- The system is rebooted while holding the Control key during the Windows Recovery Environment phase
- The machine boots directly to an elevated command prompt with full access to the formerly Bitlocked drive
Notably, the exploit files automatically disappear from the USB drive after use, making detection difficult and adding to suspicions of a potential backdoor in the system. This characteristic has raised uncomfortable questions about whether this vulnerability was intentionally introduced or exists as an unintended consequence of the implementation.
The vulnerability affects Windows Server 2022 and 2025, as well as recent consumer versions of Windows, but does not impact Windows 10. This discrepancy suggests that Microsoft may have inadvertently introduced the vulnerability in newer versions during updates to the recovery environment or related components.
Exploit Context and Researcher Motivations
Chaotic Eclipse, who has previously published other significant zero-day exploits including BlueHammer and RedSun, claims these disclosures are a response to Microsoft's security team allegedly dismissing their previous vulnerability reports. The researcher stated in their disclosure: "I could have made some insane cash selling this, but no amount of money will stand between me and my determination against Microsoft."
This pattern of disclosure following alleged dismissals suggests a potential systemic issue in Microsoft's vulnerability handling process. The researcher has demonstrated technical competence with previous exploits that were later confirmed and patched, lending credibility to their current claims.
Impact Assessment and Market Implications
The implications of the YellowKey exploit extend far beyond simple data breaches. BitLocker is Microsoft's proprietary full-disk encryption, enabled by default in Windows 11 and widely deployed across enterprise, government, and military systems. The U.S. government alone has over 4 million federal employees using systems that potentially contain this vulnerability.
Financial impact estimates for organizations affected by this vulnerability could reach billions of dollars when considering:
- Data breach remediation costs
- Regulatory compliance penalties
- Re-encryption of affected systems
- Potential class-action lawsuits
- Stock valuation impacts for affected companies
Enterprise security experts have expressed particular concern about the exploit's ability to bypass even enhanced security configurations. The researcher noted that a full TPM-and-PIN setup doesn't protect against this vulnerability, though they claim to have developed a variant specifically for that scenario which they haven't published.
The GreenPlasma Complementary Exploit
Alongside YellowKey, Eclipse also published details of GreenPlasma, a local privilege escalation vulnerability that allows attackers to gain system-level access beyond standard administrator privileges. This exploit works by manipulating the CTFMon process to place crafted memory section objects in Windows Object Manager sections accessible to the SYSTEM user.
While GreenPlasma currently lacks a complete proof-of-concept, Eclipse's track record suggests the vulnerability is legitimate. The combination of YellowKey and GreenPlasma would allow an attacker to first access encrypted data and then gain complete control over the system.
Industry Response and Mitigation
As of this writing, Microsoft has not issued an official response regarding either YellowKey or GreenPlasma. This silence is particularly concerning given the severity of the vulnerabilities. BlueHammer has been patched in recent updates, and Eclipse claims RedSun was silently patched by Microsoft, though this has not been officially confirmed.
Organizations should consider these immediate mitigation strategies:
- Implement additional encryption layers beyond BitLocker
- Require full disk encryption with separate authentication hardware
- Restrict physical access to critical systems
- Monitor for unusual recovery environment activities
- Consider alternative encryption solutions for sensitive data
The discovery of YellowKey represents a significant setback for trust in Microsoft's encryption technologies. For organizations relying on BitLocker for compliance with regulations like HIPAA, GDPR, or various government security standards, this vulnerability creates immediate compliance violations that must be addressed.
The broader semiconductor and security industries will be watching closely how Microsoft responds to this disclosure. The vulnerability's characteristics, particularly the self-deleting exploit files, suggest either an extremely sophisticated attacker or potentially an intentional backdoor feature that Microsoft may have difficulty explaining or defending.
Bruno Ferreira is a contributing writer with expertise in PC hardware security and development. His analysis combines technical understanding with market perspective to provide comprehensive insights into emerging vulnerabilities and their real-world implications.

Comments
Please log in or register to join the discussion