Cisco Talos researchers have uncovered LucidRook, a sophisticated Lua-based malware targeting Taiwanese organizations through spear-phishing campaigns, featuring modular design and advanced obfuscation techniques.
A new Lua-based malware called LucidRook has been discovered in targeted spear-phishing campaigns against non-governmental organizations and universities in Taiwan, according to researchers at Cisco Talos.

The malware, attributed to threat group UAT-10362, demonstrates "mature operational tradecraft" through its sophisticated infection chains and modular architecture. Cisco Talos first observed LucidRook in attacks during October 2025, where phishing emails delivered password-protected archives to victims.
Infection Chains and Delivery Methods
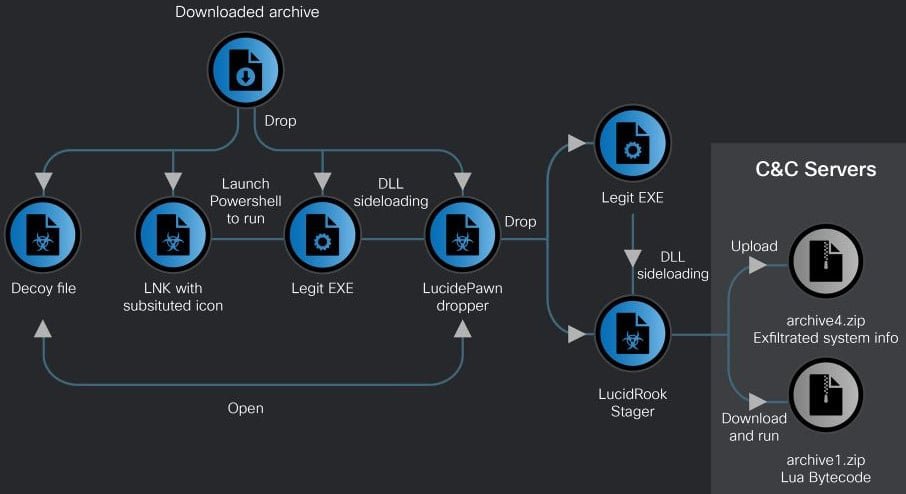
Cisco Talos identified two distinct infection chains used to deploy LucidRook:
LNK-based attack chain: This method uses a malicious shortcut (LNK) file that displays decoy documents designed to appear as official government correspondence from Taiwanese authorities. The decoy documents serve to distract users while the malware executes in the background. The attack chain ultimately delivers a malware dropper called LucidPawn.
EXE-based attack chain: This alternative approach leverages a fake antivirus executable that impersonates Trend Micro Worry-Free Business Security Services, exploiting users' trust in legitimate security software.
LucidPawn: The Initial Dropper
Once the LNK file is activated, LucidPawn performs several critical functions:
- Decrypts and deploys a legitimate executable
- Renames the legitimate executable to mimic Microsoft Edge
- Loads a malicious DLL (DismCore.dll) for sideloading LucidRook
The use of legitimate executable renaming and DLL sideloading represents a common technique for evading detection while maintaining persistence on compromised systems.
LucidRook's Modular Architecture
What makes LucidRook particularly noteworthy is its innovative use of Lua scripting:
- Built-in Lua execution environment allows retrieval and execution of second-stage payloads as Lua bytecode
- Modular design enables operators to update functionality without modifying the core malware
- Lua bytecode payloads can be hosted briefly and removed from command-and-control infrastructure after delivery
- Significantly reduces forensic visibility for incident responders
"Embedding the Lua interpreter effectively turns the native DLL into a stable execution platform while allowing the threat actor to update or tailor behavior for each target or campaigns by updating the Lua bytecode payload with a lighter and more flexible development process," Cisco Talos explains.
This architecture provides several operational advantages:
- Flexibility: Operators can quickly adapt malware behavior for different targets
- Stealth: Brief hosting of Lua payloads reduces detection opportunities
- Evasion: Hinders post-incident reconstruction when only the loader is recovered
Advanced Obfuscation Techniques
The malware employs extensive obfuscation across multiple components:
- Embedded strings are heavily obfuscated
- File extensions are disguised
- Internal identifiers are obscured
- Command-and-control addresses are encrypted
These obfuscation techniques significantly complicate reverse-engineering efforts, making analysis and detection more challenging for security researchers and defensive teams.
Post-Infection Activities
During execution, LucidRook performs comprehensive system reconnaissance:
- Collects user and computer names
- Identifies installed applications
- Monitors running processes
- Gathers system information
The collected data is encrypted using RSA encryption, packaged into password-protected archives, and exfiltrated to attacker-controlled infrastructure via FTP protocols.
Related Tools and Infrastructure
Cisco Talos also identified a related reconnaissance tool called "LucidKnight," which likely serves as a precursor to LucidRook deployment. Notable characteristics of LucidKnight include:
- Abuse of Gmail GMTP for data exfiltration
- Flexible toolkit approach for varying operational needs
- Suggests UAT-10362 maintains diverse capabilities
The use of legitimate email infrastructure for exfiltration demonstrates the threat group's sophisticated approach to avoiding traditional network-based detection methods.
Attribution and Campaign Assessment
Cisco Talos tracks the threat actor behind LucidRook as UAT-10362, describing them as a "capable adversary" with mature operational tradecraft. The researchers assess with medium confidence that these attacks represent a targeted intrusion campaign.
However, a significant limitation in the analysis exists: Cisco Talos was unable to capture a decryptable Lua bytecode payload fetched by LucidRook. This means the specific actions taken after the initial infection phase remain unknown, highlighting the challenges in fully understanding sophisticated malware operations.
Implications for Security Teams
The discovery of LucidRook carries several important implications:
- Targeted attacks on NGOs and educational institutions remain prevalent
- Lua-based malware represents an emerging trend in sophisticated attacks
- Modular malware architectures enable rapid adaptation to defensive measures
- Advanced obfuscation techniques continue to evolve
- Spear-phishing remains an effective initial access vector
Organizations in Taiwan and similar regions should be particularly vigilant, implementing robust email filtering, user awareness training, and endpoint detection capabilities to defend against such targeted campaigns.
The LucidRook campaign demonstrates how threat actors continue to innovate with new programming languages and architectures to achieve their objectives while evading detection. The combination of Lua scripting, modular design, and advanced obfuscation represents a significant evolution in malware development that security teams must adapt to defend against.

Comments
Please log in or register to join the discussion